Hi Everyone,
I would like to continue the journey of my penetration testing excercise. In the previous post that we have been able to load some of the web application .php file trough LFI vulnerability at test.php page.
During our analyses on that page, We could see that there are two credential found which is first is the connection db for application to connect to the back end db and other one is credential used by the phpmyadmin to connect to backend database.
We can see from the credential that we have been able gathered, there are two credential used where one is username = billu and password = b0x_billu and the other one is username = root and password = roottoor.
It is very interesting that phpmyadmin using root account to connect to the mysql database with specified password, what is this mean ? MySQL database that run on the box is still using the default setting which is using root account to manage the database. It does mean the account phpmyadmin using to connect to the MySQL is the system account, You can use this to log in to the system.
Let’s check how can we access the box using the root account ? If we check back the result of nmap, here is the snippet of nmap result
Nmap scan report for 192.168.5.140
Host is up, received arp-response (0.00068s latency).
Scanned at 2019-01-14 06:43:02 PST for 85s
Not shown: 998 closed ports
Reason: 998 resets
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 64 OpenSSH 5.9p1 Debian 5ubuntu1.4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 fa:cf:a2:52:c4:fa:f5:75:a7:e2:bd:60:83:3e:7b:de (DSA)
| ssh-dss
we found that SSH service is up on the box, Let try to connect to the box using ssh with root, can we log in ?
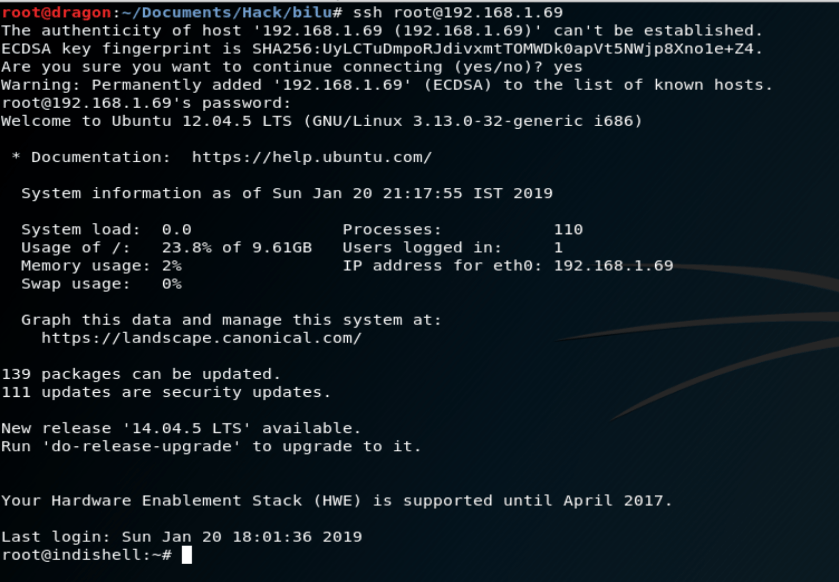
yeah we can get it using root. We own the system now.
I would like to give you a bit lesson learn that we find here so that the lesson from here can be used to harden your system
The mistakes
- MySQL database is still using the default username and password which is using root account. You can follow the step defined https://dev.mysql.com/doc/refman/8.0/en/resetting-permissions.html
- Phpmyadmin shall not use root to connect to the backend database. It should use another lower account to connect.
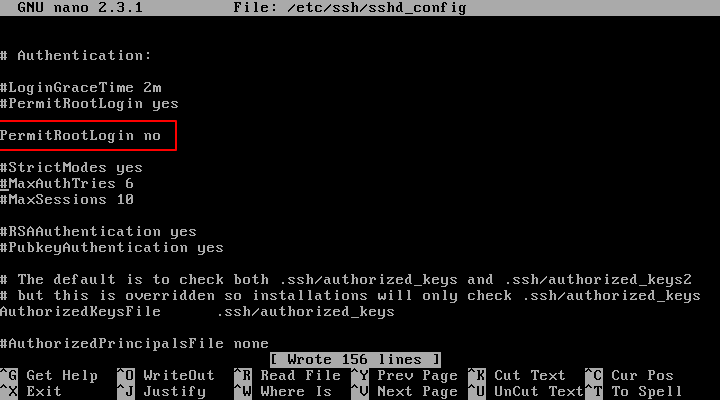
- Ssh server allow root to access remotely. For better security, Ssh shall not allow root to be accessed via remote ssh. You can edit the sshd_config file to become like below