Hello Hacker,
Lets have some fun again with database, I would like to share an idea on database exploitation due a common miss configuration occurred in the enterprise setup.
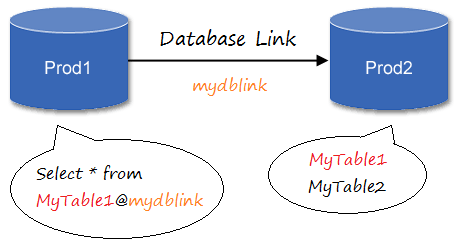
In many organizations that has so many application within their environment is using database external link to integrate some database to allow one database to retrieve data directly from other database using external link. As you know that external link is just link DB connection which use specific username and password to establish the connection and having defined privilege
I found a lot of lazy DB admin connect the DB external link with SA privilege which they think it is secure because it does not interact with application that normally can be abused. I took this sample setup from HTB setup which perfectly shows the vulnerability

The database POO_PUBLIC is a database which support an application where the application uses a user called “external_user” that has no privilege access to connect to the POO_PUBLIC database

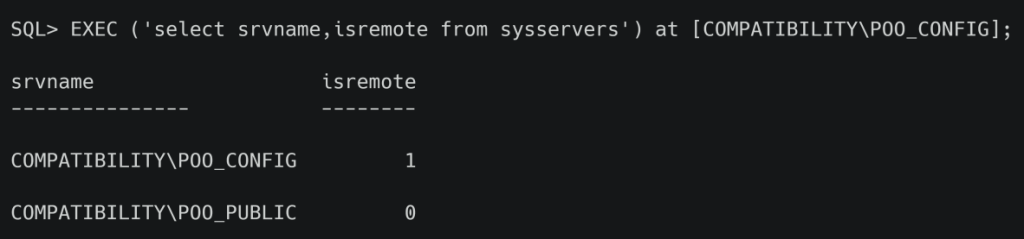
Database POO_PUBLIC has an external link to POO_CONFIG, The below query is to check the availability of external link. We can see that POO_CONFIG return flag 0 which says that it is remote database

Below is query to check what username to connect POO_PUBLIC to POO_CONFIG

We can also use this below query to check the external DB link from the perspective of POO_CONFIG but by querying the command from POO_PUBLIC. We can see that POO_PUBLIC is flagged as 0
So these two database are circular link like the picture given above. We can use a nested query to check what is the username that is used to connect POO_CONFIG to the POO_PUBLIC by using below query

From the output above, We can see that the lazy DB admin uses sa account to create external DB link from POO_CONFIG to POO_PUBLIC where allowing the hacker to execute SQL query as DBA (Sysadmin) on POO_PUBLIC
Exploitation
Having the understanding of the above situation, The hacker is able to develop a nested query to exploit the missed configuration between these two databases. The hacker is able to create a new user in POO_PUBLIC database and grant it with admin privilege so that the hacker would be able to escalate them self in the POO_PUBLIC database
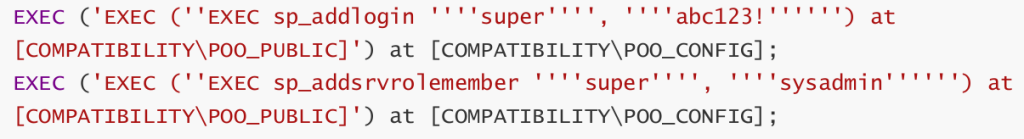
The first query above is to create new user called super with password abc123! at POO_PUBLIC. The second query is to grant the user called “super” as sysadmin in the POO_PUBLIC.
Then the hacker can start to utilize the newly created user to leverage the attack to go deeper into the server OS.