Hi Friends,
As we know that there is very limited tutorial about Core Impact application in the internet hence I would like to share my experience of using this during Pentest in my lab.
Core Impact provides a lot of high quality modules that enable you to work effectively during the Pentest or Red Team emulation. Core Impact has a very user friendly agent capability and quite powerful pivoting mechanism
Today, I am gonna share tutorial about the Core Impact agent to be used as socks 5 traffic pivoting from other host.
Below is the network topology that I am going to use for this tutorial
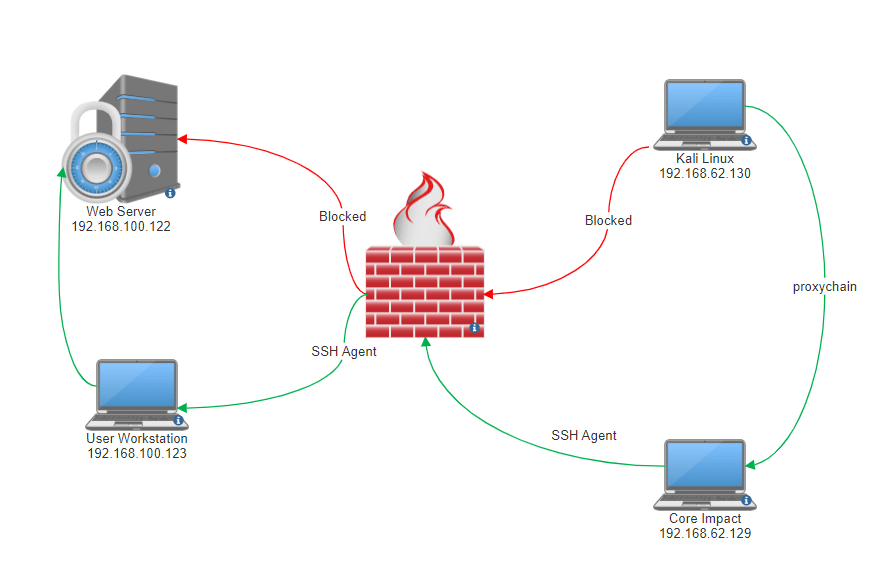
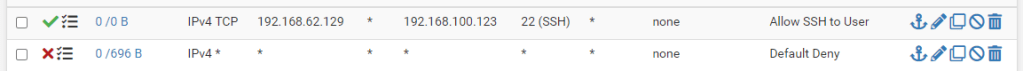
The following is the firewall rules that I am using. The firewall only allows the SSH connection from the Core Impact Machine to the User Workstation.
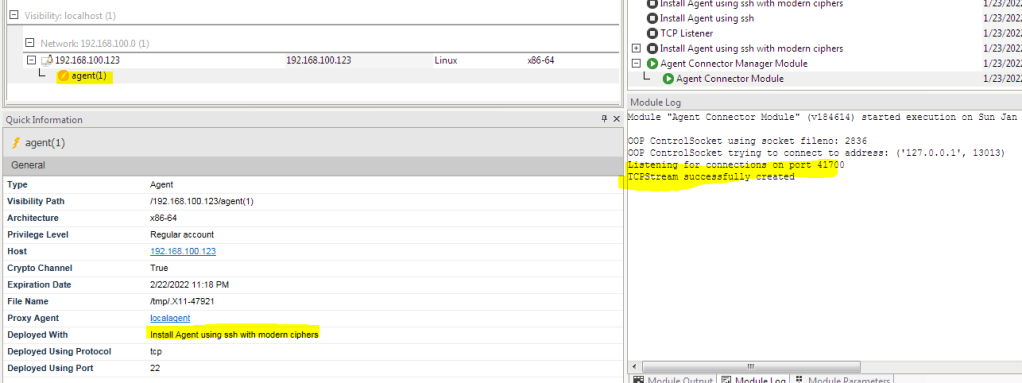
The Scenario is the user workstation has been compromised and we are successfully to install the Core Impact SSH agent to the on the user’s workstation.
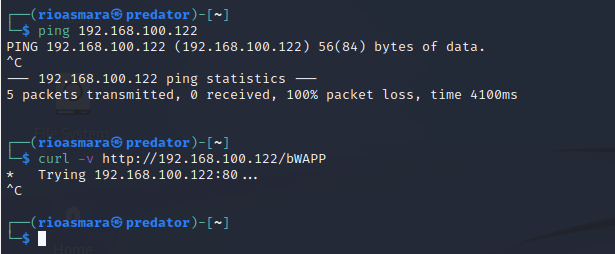
The next thing is we want to allow our Kali Linux machine to communicate with network 192.168.100.0/24 that has been blocked by the firewall. We want to attack web server with IP 192.168.100.122 from kali linux behind the firewall that does not have direct access.
To allow the traffic from the Kali Linux to the Web server, We need to utilize the SSH agent that is connected to the User’s workstation as the Sock 5 tunnel
Create Sock Proxy Tunnel
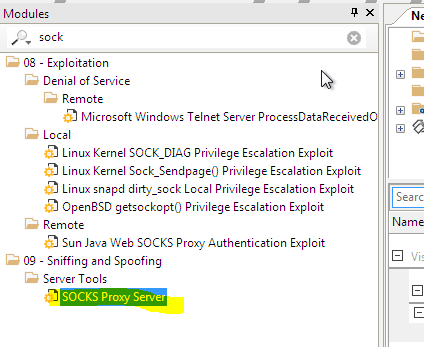
To create the proxy tunnel with Core Impact SSH agent. You need to find the module with name “Sock Proxy Server”
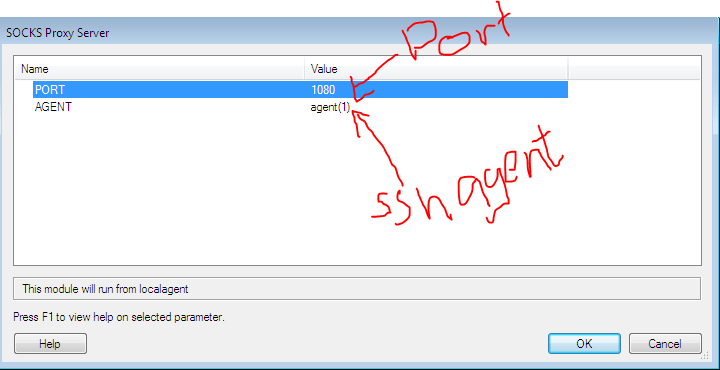
Then you must fill in the required parameter as below. Port to listen the incoming traffic. Agent is the agent that we are going to use as the tunnel to the user’s workstation
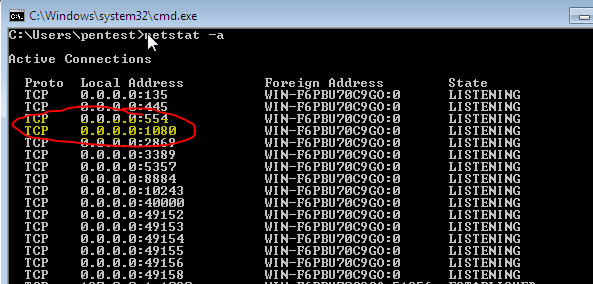
We can see that after we press button OK, then the Sock server will open a listener that accept connection from any source
Proxychain Kali Linux
Now the sock 5 tunnel is ready to accept the connection. We need to configure kali linux traffic to use that tunnel to reach the web server with the help of proxychain
Configure the Proxychain
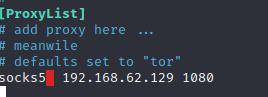
You need to edit the proxychain configuration to point the sock 5 proxy to the IP 192.168.62.129 port 1080

Then, You need to go down of the file and edit the proxy list and save the proxychains4.conf
Test access the web with Proxychain
Lets try to access the web server from the kali machine with the help of proxychain
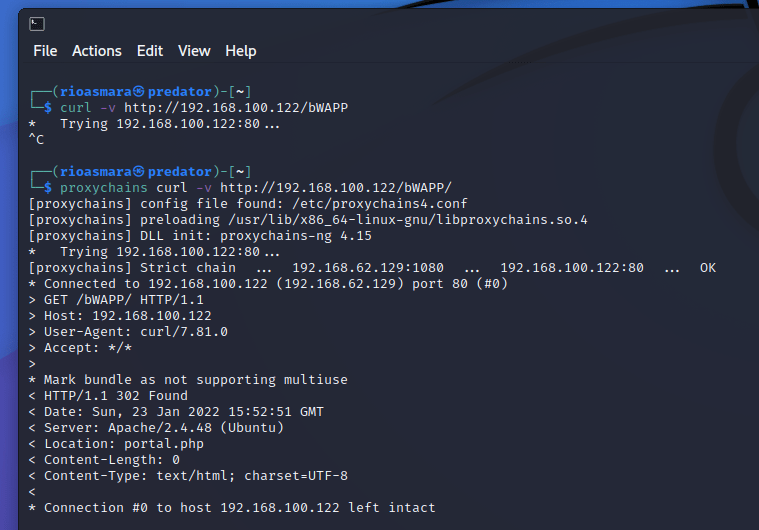
We can see that if we access directly then it does not work but if we proxychain the wget traffic via the Core Impact Sock Proxy Chain then wget is able to bypass the firewall restriction
Access via Web Browser
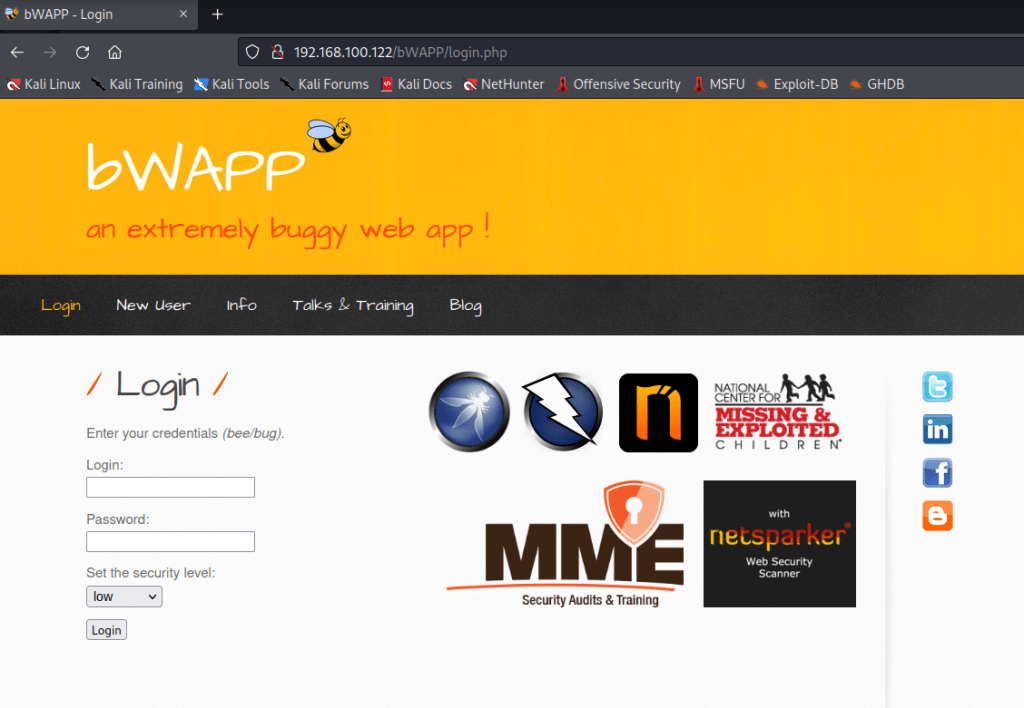
We can also access the web server using the web browser by configuring the proxy to use sock 5 tunnel

If we access the web server then the browser will now able to open the web application
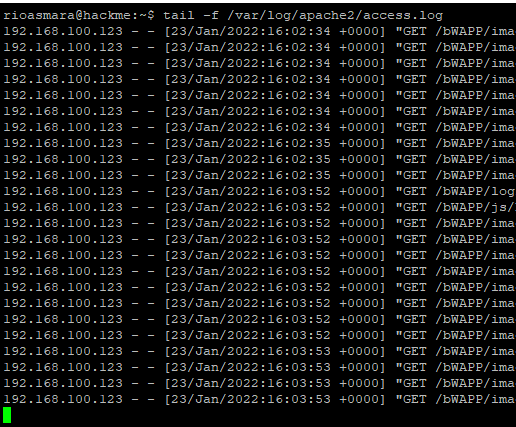
If we looked at the apache access.log at the web server, the traffic is coming from the user workstation that has been compromised and being used as proxy from the kali linux machine with IP 192.168.100.123
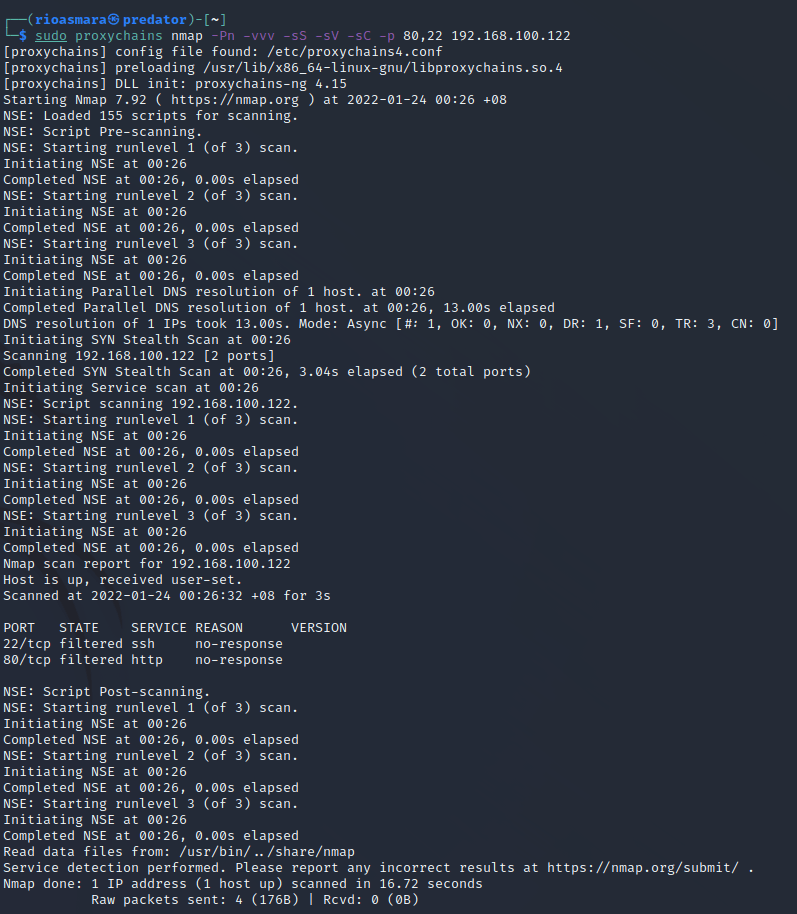
Nmap with Proxychain
We also do nmap scanning with the proxychain and the tunnel given by the Core Impact SSH agent. We can see that nmap is successfully identified the port 80 and 22 are open on the web server
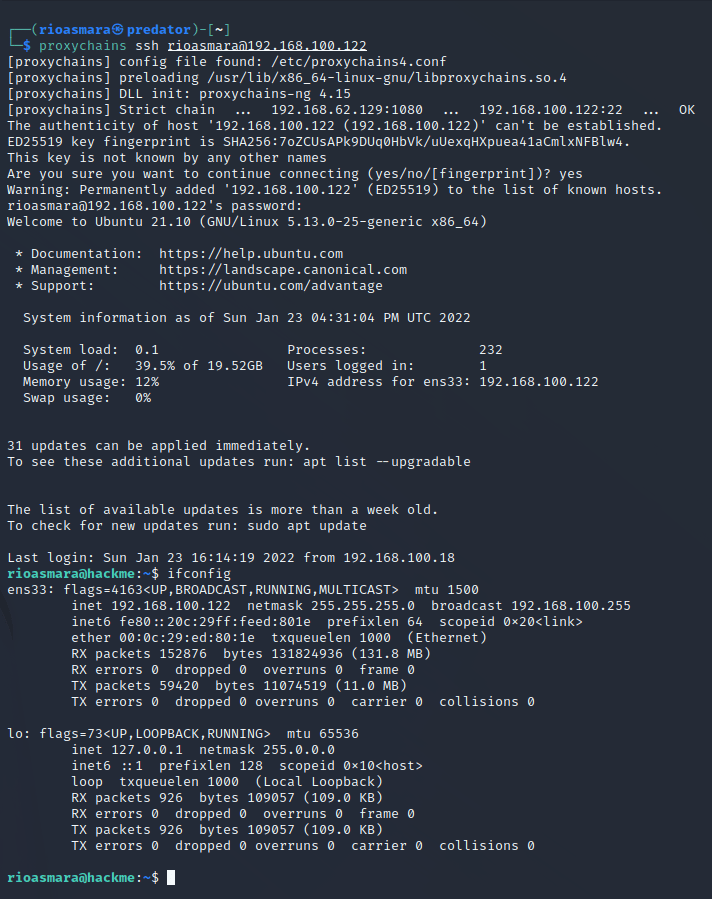
SSH with Proxychain
Now we can also do SSH directly to the web server with IP 192.168.100.122 via the proxychain that we have. We can see that login and authentication are smooth
That is it on how to make the Sock proxy server by utilizing the Core Impact agent to enable to bypass the firewall restriction so that the adversaries is able to pivot their traffic via the compromised user workstation. i can also see that the Sock Proxy Server attached to the SSH Agent is very robust and stable that I cannot see any degradation on the performance