Hi Guys,
After taking some times to take some doing many other things, I am finally back writting small tutorial at my blog.
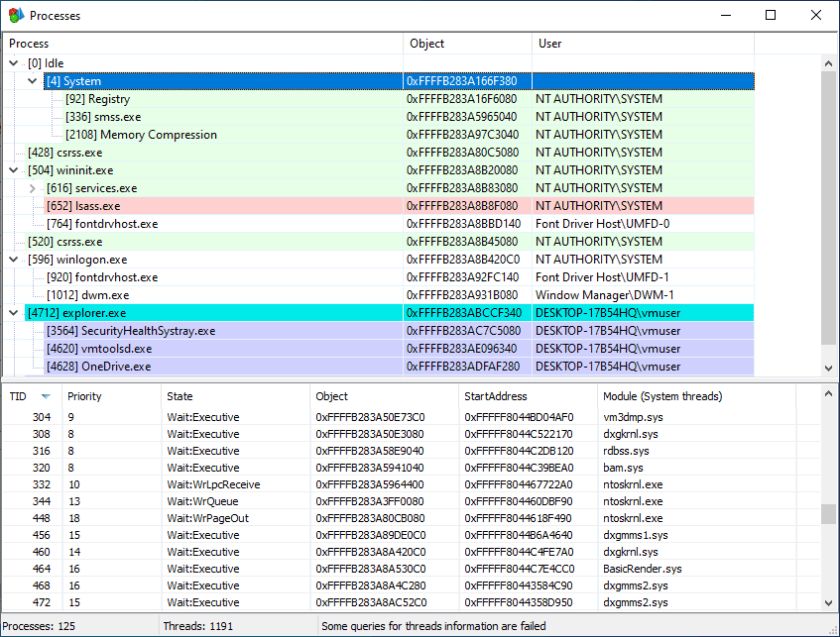
If you want to start learning exploit development but you dont know where to start and what kind of code to start with, you are landing on the right blog. Today, I am going to write a small code to iterate windows process and return it’s PID
Why this code is very important to understand in malware development because when you want to inject your malicious payload, you need to know what process is currently running in the target host.
int FindTarget(const char* procname) {
HANDLE hProcSnap;
PROCESSENTRY32 pe32;
int pid = 0;
hProcSnap = CreateToolhelp32Snapshot(TH32CS_SNAPPROCESS, 0);
if (INVALID_HANDLE_VALUE == hProcSnap) return 0;
pe32.dwSize = sizeof(PROCESSENTRY32);
if (!Process32First(hProcSnap, &pe32)) {
CloseHandle(hProcSnap);
return 0;
}
while (Process32Next(hProcSnap, &pe32)) {
printf("PID : %d --> : %s \n", pe32.th32ProcessID, pe32.szExeFile );
if (lstrcmpiA(procname, pe32.szExeFile) == 0) {
pid = pe32.th32ProcessID;
break;
}
}
CloseHandle(hProcSnap);
return pid;
}
int main(void) {
int pid = 0;
pid = FindTarget("notepad.exe");
return 0;
}
The above code will help to find the process based on it’s name. You need to pass the name of the targeted process that you are looking for and return its PID. The code above also prints out the other process and PID untill the targeted process is found

The code below is the one which compare the name of each process with the name we are looking for. If the name match then it will trigger break to exit the loop
if (lstrcmpiA(procname, pe32.szExeFile) == 0) {
pid = pe32.th32ProcessID;
break;
}
The Process32First function will return the first process available in the list that can be iterated with while (Process32Next(hProcSnap, &pe32)) to get the next process name
if (!Process32First(hProcSnap, &pe32)) {
CloseHandle(hProcSnap);
return 0;
}
Below is the IDA Pro pseudo code which was taken from our compiled binary.
__int64 __fastcall FindTarget(const char *procname)
{
HANDLE hSnapshot; // [rsp+20h] [rbp+0h]
PROCESSENTRY32 pe; // [rsp+30h] [rbp+10h] BYREF
unsigned int th32ProcessID; // [rsp+160h] [rbp+140h]
th32ProcessID = 0;
hSnapshot = j_CreateToolhelp32Snapshot_0(2u, 0);
if ( hSnapshot == (HANDLE)-1i64 )
return 0i64;
pe.dwSize = 304;
if ( j_Process32First_0(hSnapshot, &pe) )
{
while ( j_Process32Next_0(hSnapshot, &pe) )
{
j_printf("PID : %d --> : %s \n", pe.th32ProcessID, pe.szExeFile);
if ( !lstrcmpiA(procname, pe.szExeFile) )
{
th32ProcessID = pe.th32ProcessID;
break;
}
}
CloseHandle(hSnapshot);
return th32ProcessID;
}
else
{
CloseHandle(hSnapshot);
return 0i64;
}
}