Hi Guys,
During the malware analyses, we sometimes require some ideas of what the malware is trying to do with our system, such as dropping files, reading files and executing some binary. There are many ways of gathering this information, but the easiest way is to use procmon
I have a very simple dll which let us assume this is our malware sample that we run and load using regsvr32. The dll is doing some activities such as writing a file, check file exist and start calculator
// dllmain.cpp : Defines the entry point for the DLL application.
#include "pch.h"
#include <stdio.h>
#include "Shlwapi.h"
#include <windows.h>
#include <stdlib.h>
BOOL APIENTRY DllMain( HMODULE hModule,
DWORD ul_reason_for_call,
LPVOID lpReserved
)
{
char buffer_1[] = "C:\\TEST\\file.txt";
switch (ul_reason_for_call)
{
case DLL_PROCESS_ATTACH:
MessageBox(nullptr, "Rio Malware Loaded", "Loaded", MB_OK);
FILE* fp;
fp = fopen("C:\\Temp\\test.txt", "w+");
fprintf(fp, "This is testing for fprintf...\n");
fputs("This is testing for fputs...\n", fp);
fclose(fp);
char* lpStr1;
lpStr1 = buffer_1;
int retval;
retval = PathFileExists(lpStr1);
if (retval != 1)
{
MessageBox(nullptr, "Rio Malware cannot find file", "Loaded", MB_OK);
}
WinExec("calc", SW_SHOWNORMAL);
case DLL_THREAD_ATTACH:
case DLL_THREAD_DETACH:
case DLL_PROCESS_DETACH:
break;
}
return TRUE;
}
Finding the file wirtting
Procmon allows you to analyze file operation such as file read, write, open and close. it can also track how many bytes read and write. Very handy right.
Lets start hunt the process. I will start my dll loading using below command
regsvr32 -s riomalware.dll
Before you run the riomalware.dll, you need to have the procmon be ready by clicking the capture button.

when the procmon is in capturing mode then you can run the malware sample.
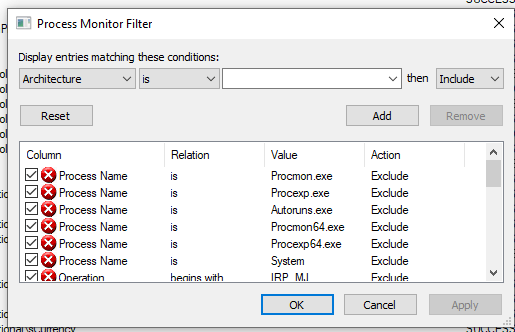
In the malware code, we found the first step is basically will write a file. But let us assume we don’t know the path and how big it is. We can filter out the events gathered by the procmon by using the filtering function

and adjust the filter parameter in this window
There is another way that is also easy to approach is by using process tree

it will give you tools like a task manager which listing all the application that is running and also application that has stop

Since we use regsvr32 to load our dll then we can filter based on this application name by following the image below

When you select that option then the main windows will onlys show events that related to regsrv32 like below image.

Because we are looking for an event that is related to file write, then basically, we can again filter out events that are not related to file system operation by clicking on the following. we only show for filesystem activities

We can see that there is file operation CreateFile in the C:\Temp\test.txt was SUCCESS

We can also see that the malware was also trying to look file C:\Test\file.txt but it could not find it.
New Process
As we can see from the malware code that it will also create new process that execute calculator. To analyze that we can filter with different group following the below image
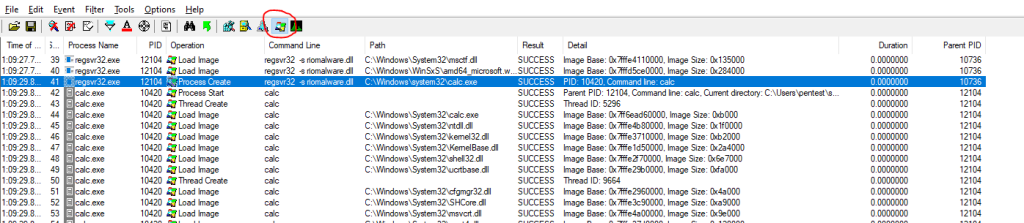
By activating the circled filter, Procmon will only show the process and thread events only.

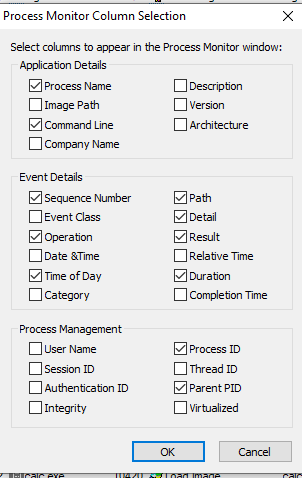
we can see that regsrv32 create process calc from the path C:\Windows\system32\calc.exe. To gathere more data, you can adjust the column to enable more information shown in the window using the following steps

this is my configuration. You can choose your own to suite your needs.
For the Blue Team (Living of the Land)
for the blue team who is monitoring the threat. The above steps would allow you to analyze malware behaviour easier.
For those monitoring the windows event log events, Loading malware with regsvr32 becomes one of the techniques to bypass malware detection because the malware was loaded into memory using a legitimate windows application. But there is a use case that you can build a base on the fact of following
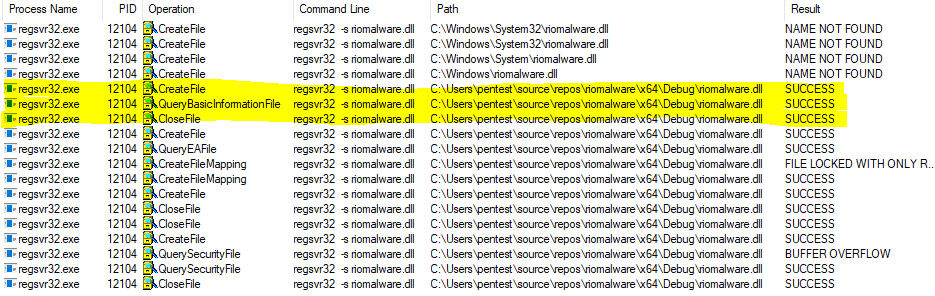
We can see that regsvr32 do some file processing CreateFile, QueryBasicInformationFile and CloseFile from non-legitimate windows path would become a good indication of the land technique being used by the adversaries to infect your system.