Hi Everyone,
Today I am going to talk about cookie security which implement encryption. Why do we need to put attention to the security of our application cookie? because it becomes the key to allow the web server to know who we are and maintain our session.
One of the way to improve the seurity some application do encrypt the authentication cookies to disable the variable being seen by human which reduce the attack surface.
But how do the attacker may handle this situation ? Burpsuite has a very powerfull function (Sequencer) that enable the attacker to analyze the encrypted cookie for the entrophy. Burp will do the statistic analyses on the token gathered from the sampling.
Lets do the attack.
The scenario of this attack there will be a web application requires login to enter to the application but before you are required to register to the application. The objective of the attack is to have the admin login in order to get the important information. I have analyzed the potential attack surface but for this box the attack surface is at the cookie. So we will analyze it using burp.
Initial information
- We know that there have been an account registered as admin as show below
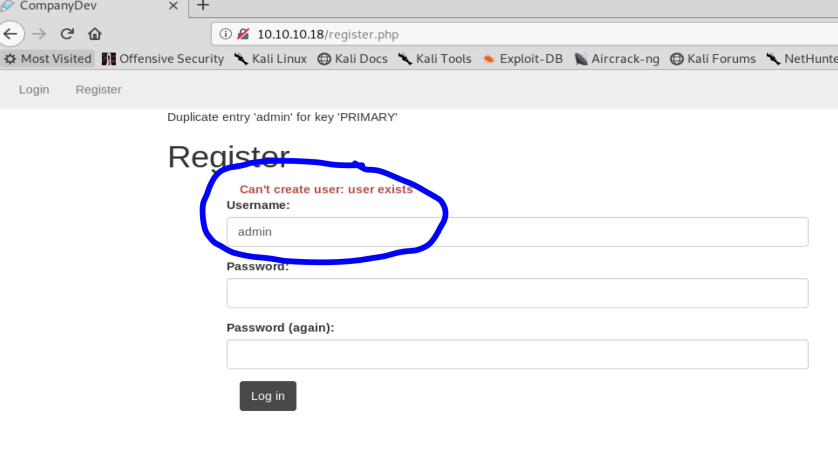
- We should register with another account to see the cookie. I will do create an account to be simillar with admin user name which is cdmin
- Lets check the cookie

- Let send it to sequence for analyses

- Press start live capture

- From the above result that Burp analyze the entropy is exellent which the randomnes is good. so we can not predic the next auth key set in the cookie.
Soooo how the attack would be ? We ca do bruteforce it by using burp intruder where the payload is bitflip which perhaps sometimes will make logged in to the application
- first we should get the cookie of our legitimate login which is cdmin
- Send to intruder
- Set the location is at the auth variable in the cookie

- Set the payloads with bit flipper as below

- Press Start Attack
- Analyze the output. To make life easier you can sort the output length and check are we logged in ?Below we see that we have an error that our padding is invalid. No problem just go forward .. 🙂

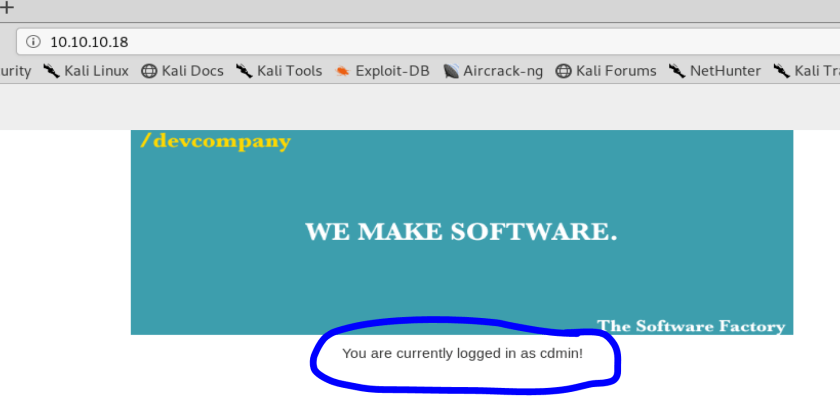
With this auth token we are logged as cdmin which is our account

Magically, We found the token to login as admin. You see below we are logged as admin. We can use the token to login as admin without using password.

OK hopefully this tutorial will give you an idea on how to bruteforce the cookie.
Great tutorials !!! Good job thanx and Good Luck Man 😉
Thank you Peter..