Hi Friend,
I am writting this to share experience using an application called Cyber Triage which really helps on the endpoint investigation. https://www.cybertriage.com/
As you know that endpoint investigation is alot of manual task to find out how the adversaries could compromise the server or end user device. I found that Cyber Triage application could help to prioritise the investigation and giving alot of hints based on the artefact gathered
Data Collection
Cyber Triage has various way to collect artefact from the endpoint. The best collection that I experience is the live manual because we can just run the agent on the suspected machine with the admin privilege without any installation. The agent will connect and supply the artefact for realtime analysis

Data Analysis
The next is about the data analysis. Cyber Triage provide a realtime data analysis while we are collecting information from the endpoint hence the investigator can start the analysis as soon as possible the artefact are collected

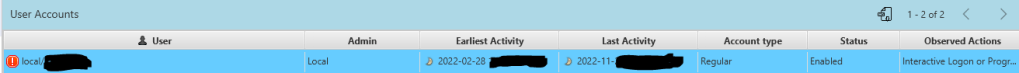
Cyber Triage make the analysis more effective because we dont need to think about parsing data here and there. It can correlate data from various artefact into single page hence by reading that the investigator could have an idea. Just for example the user information like below
From the screen capture below, we can see that there are 3 start up items which potentially 2 of them are malware.

Below is the .exe file analysis which show the result of initial analysis such as publisher name and know incident based on that files.

There are many more information that you can gathered from Cyber Triage. I have a good user experience with this application because it give me alot of hints to prioritize the direction of further manual analysis required.