Hi Friend
It is been a while of not updating this blog. It does not mean I stop doing some research. Today, i would like to share one of adversaries technique to bypass detection.
As we know that one of the endpoint forensic is to check the file creation, modification and last access to identify potential of file that has been droped by the adversaries to compromise the endpoint
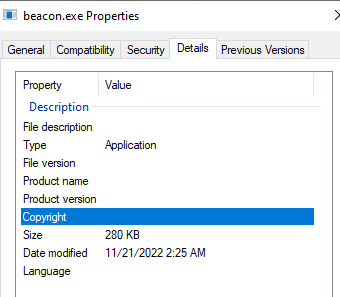
Just for example below that I droped a beacon.exe executable at C:\Temp of the compromised host that I created and modified at 11/21/2022. This file is very easy to be found by the forensic analyst because this file is very recent in C:\Temp which might give clue to the forensic that this file is malicious
Timestomping wth CobaltStrike
Cobaltstrike has a good function to help the adversaries to hide their malicious files
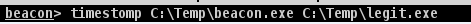
We can manipulate our beacon.exe to have the same the same time property of the legit.exe file. This could make the malicious files looks less suspicious during the endpoint forensic.
After the above operation, we can see that the beacon.exe and legit.exe have the same time porperty


Key Indicators of Timestomping
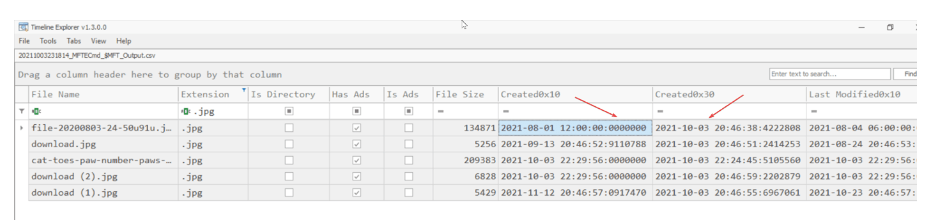
There are a few key indicators that could point to timestomping when looking for malicious files. These include:
- When the subseconds in the $MFT’s 0x10 timestamps is .000000
- If the 0x10 timestamp appears to occur before a 0x30 $MFT timestamp
- If the context of a file relating to its name, parent folder or other file details is inconsistent
These fields, SI<FN, u Sec Zeros and Copied. SI<FN and u Sec Zeros, are relevant for identifying timestomping
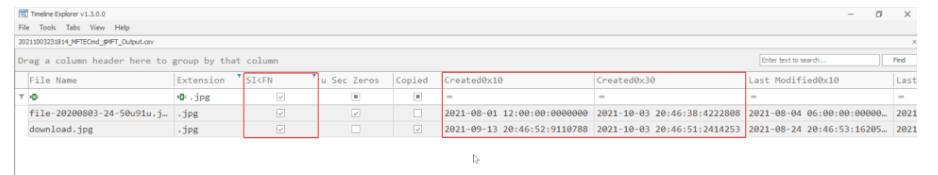
SI<FN assumes that files have been timestomped into the past. This translates to a 0x10 timestamp being earlier than a 0x30 timestamp. This logic will not notice the rare instance that a file is timestomped into the future, which should arguably stand out on its own accord.