Hi Reverser,
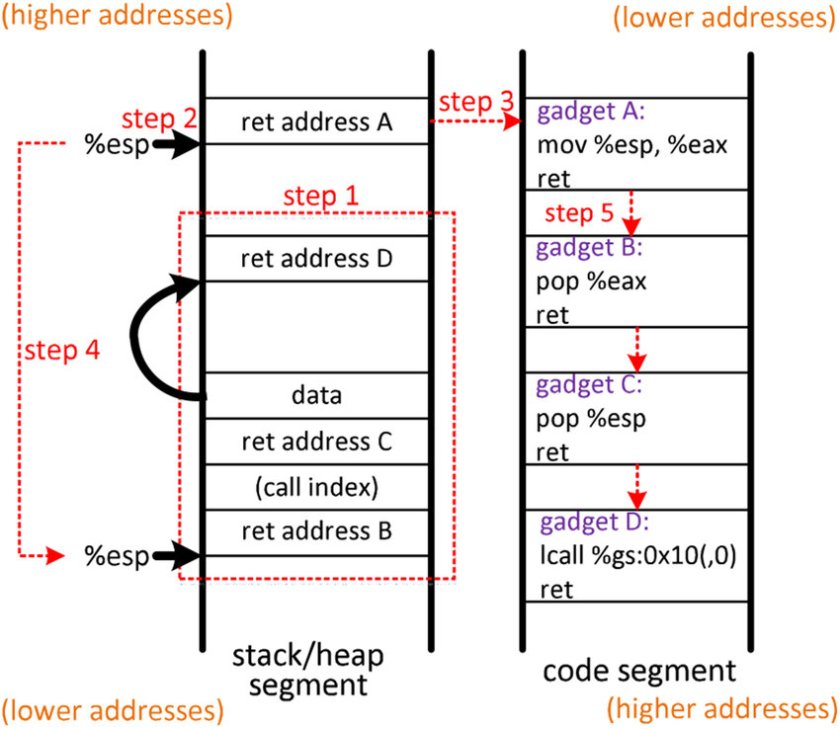
I am gonna share a basic malware or exploit development to bypass Data Execution Protection (DEP) by implementing ROP.
ROP exploitation is process hijacking the stack to manipulate control flow of the application. There is a small different methods to manipulate the control flow by using the sequence of code that already exist in the application called widget where sequence of code followed by RET
ROP Gadget
- ROP gadgets are sequences of CPU instructions that are already present in the program being exploited or its loaded shared libraries and can be used to execute almost any arbitrary code;
- ROP gagdgets most often end with the ret instruction;
- ROP gadgets bypass the DEP (NX bit protection), since there is no executable code being injected to and executed from the stack, instead existing executable code is used to achieve the same malicious intent.
The Basic
In the basic here we are going to analyze and manipulate the return of a function call to jump to another function by manipulating the stack.
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
void printMe_1() {
printf("Function Print Me 1");
}
void printMe_2() {
printf("Function Print Me 2");
}
void printMe_3() {
printf("Function Print Me 3");
}
void check() {
printf("Call Me Please");
}
int main(int argc, char** argv) {
check();
printf("Exiting...\n");
exit(0);
}
We can see from the above C code that there are 3 functions that never be called in the application printMe_1, printMe_2, printMe_3. We can manipulate the memory stack to control the flow of the application by manipulating the first RET function call in the stack.
Analyze The Stack
To analyze the stack, We need to set break point in the Check function so that we can see the stack during the Check function execution
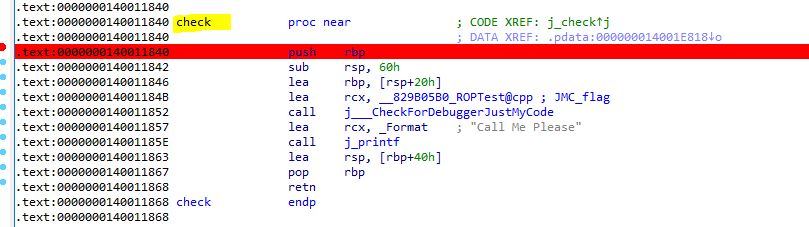
Manipulate RET address
We need to find in the stack where the RET address will go, in this case the RET address will point back to the main function right after the call to j_check which is 7FF7DCB918A4

We can confirm that when the break point is hit then we can see the return as below image pointing back to 7FF7DCB918A4
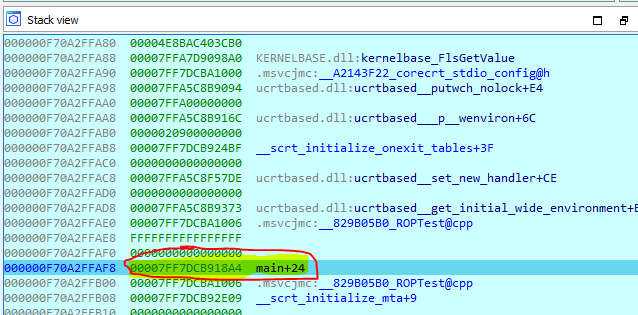
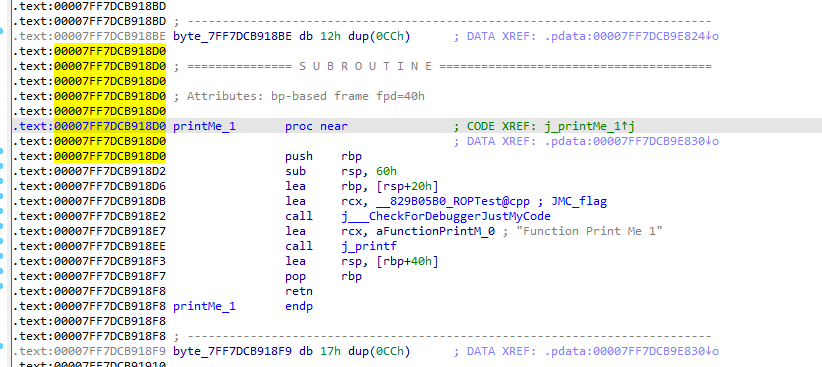
To do the attack, We can change the RET address from 7FF7DCB918A4 to another address, in this case we want to call printMe_1. We need to overwrite the address to point to printMe_1 address 7FF7DCB918D0
Lets Overwrite
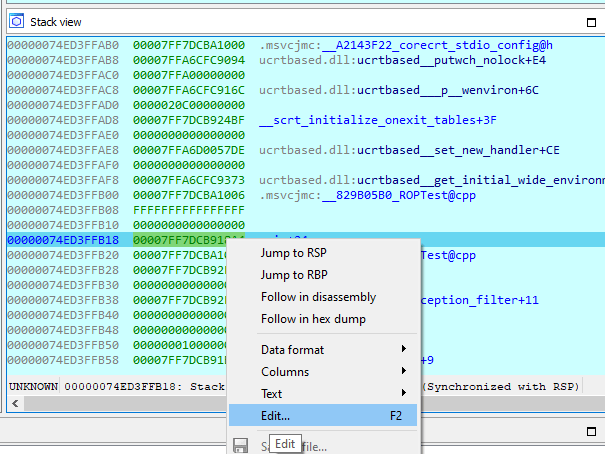
We can edit the RET address by pressing F2 on the address or just right click and select edit
after you select edit then you can start changing the address by manually input the new address 7FF7DCB918D0
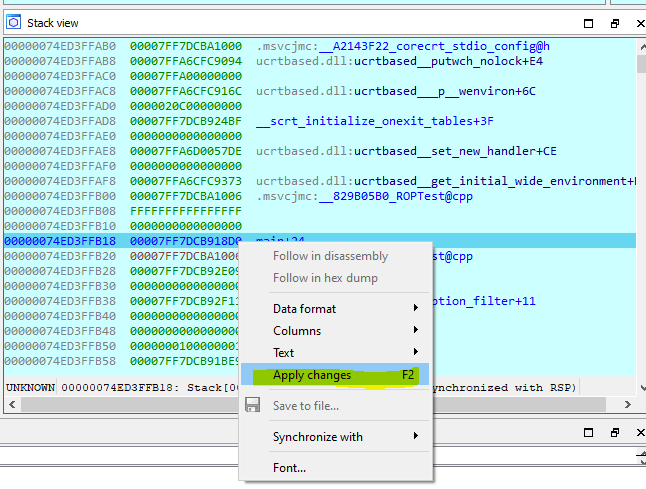
You need to set Apply Changes after you input the new value and see what is the different. Now the RET address is pointing to the new address printMe_1 where the old one is pointing back to main+24 function

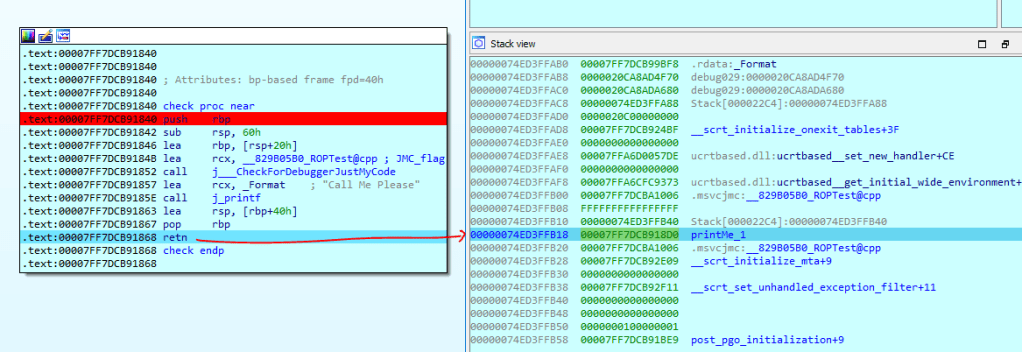
We can see that when Check function is going to return then we can see in the same time on the stack is pointing to printMe_1
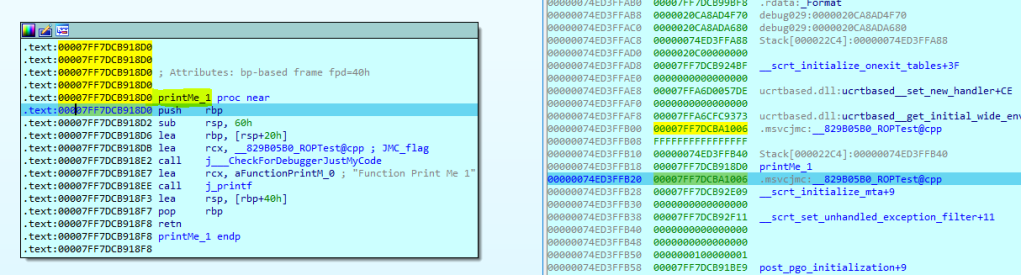
if we continue the process then we can see that we are successfully manipulate the flow from going back to main function to printme_1
I will continue the ROP Chaining in the next Post ..