Hi,
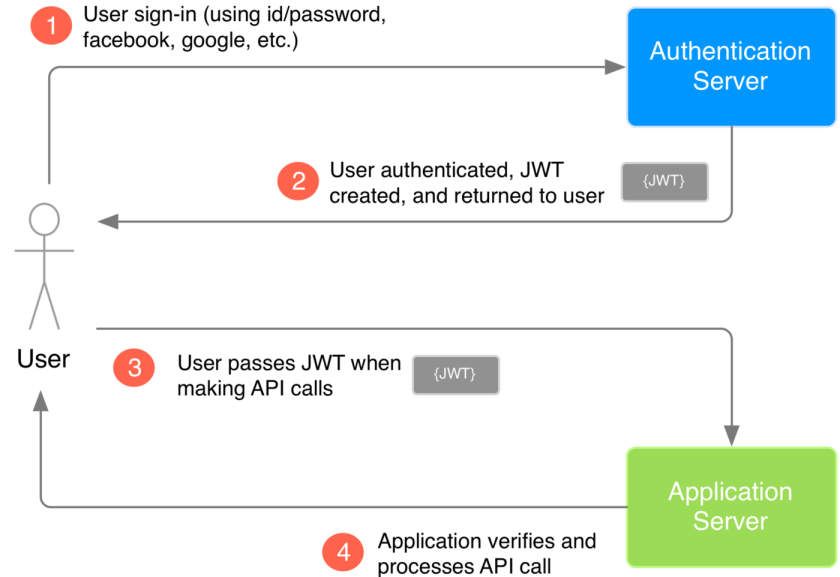
I am going to share on how to exploit JWT during the Pentest. Basically, I would share on how to compromise the JWT session from other vulnerability such as Local File Inclusion. So this article is not about exploiting JWT vulnerability
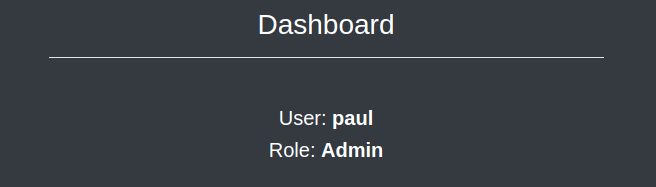
During the enumeration phase, I found a website that is using JWT to handle the session that is written to the cookies.

That token manage the the authorization of my account after I do the login process


So, We can see that JWT token is encoded with HS256 algorithm where we can see the payload contain the username of logged user to the application. So in order to forge the token then basically we need to find the signature secret key which probably hardcoded in the application code
I browsed the application for all the feature available then finally, I found vulnerability that allow me to do local file inclusion so that I can see the backend PHP code of the application.

After I managed to do the exploitation then I found a file that manages the JWT token creation for session management that allow me to steal the secret key for signature verification.
function validate(){
$ret = false;
$jwt = $_COOKIE['token'];
$secret_key = '6cb9c1a2786a483ca5e44571dcc5f3bfa298593a6376ad92185c3258acd5591e';
$ret = JWT::decode($jwt, $secret_key, array('HS256'));
return $ret;
}
With the leaked key then we can create a new token that we can inject into the cookies to jump to another user privilege
Lets create it, We can go to jwt.io to develop the new token
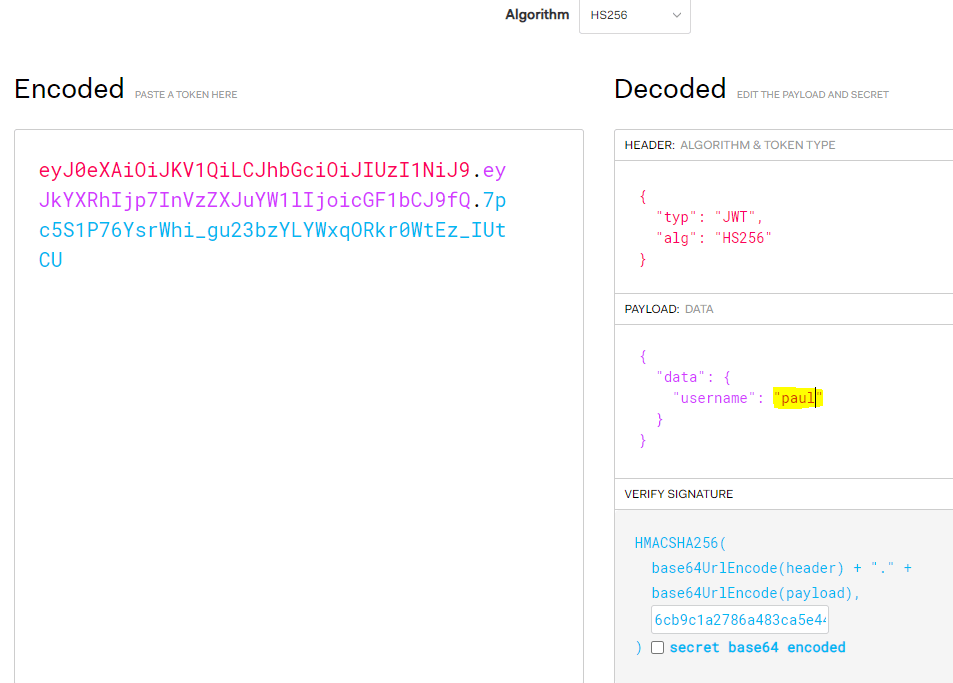
After you change the payload into an account that you want to jump into (e.g paul) then you can copy paste it into the cookies in the browser

We can see that after changing the token in the cookies then basically we can jump into another user account.