Hi Everyone,
I want to share knowledge about the essential malware component. Malware application is just like another normal application developed by following the software development’s best practice.
Common malware is built from some component that has purpose during the malware attack.
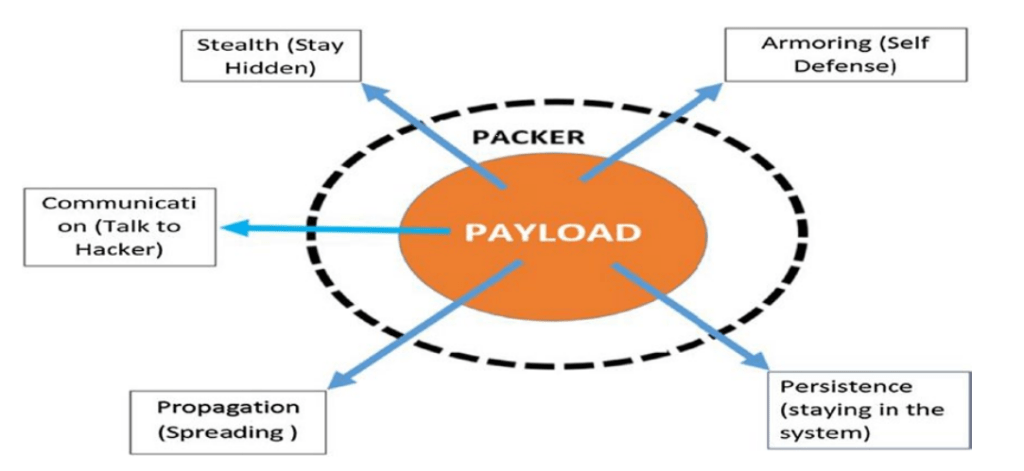
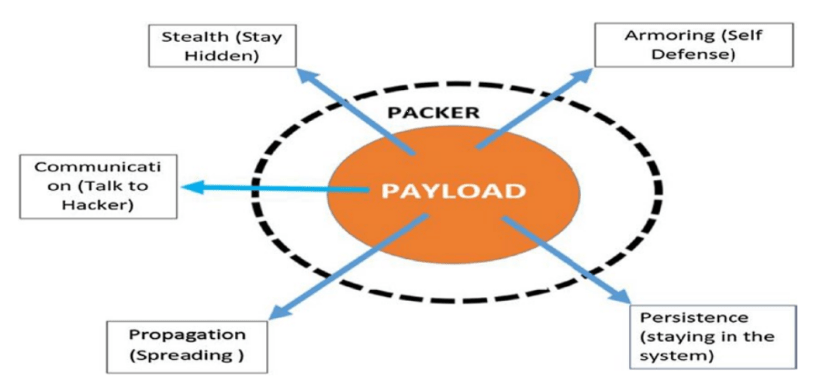
Payload
The payload is where the core of the code does the malware infection’s objective in the host. Most malware developers put their efforts into developing this code section since the attack’s success depends on this code quality.
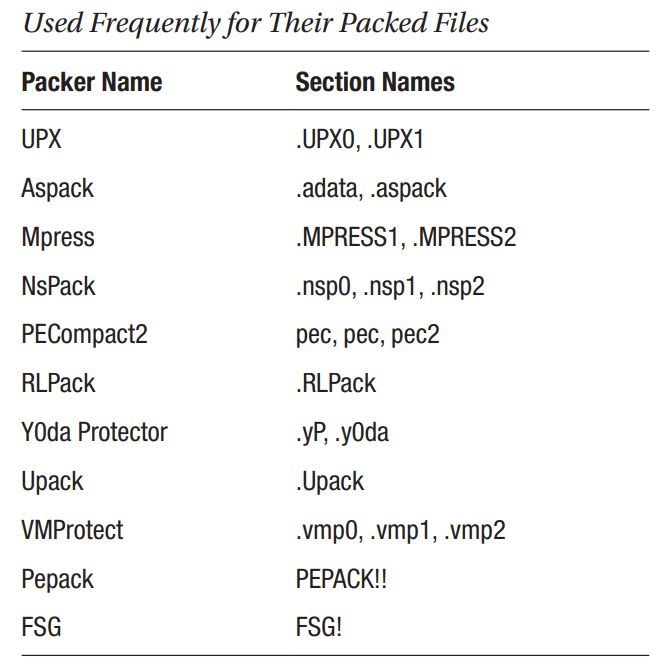
Packer
Packer is like eggshells that encapsulate the payload. Why does the payload need to be encapsulated? The answer is to hide the malicious code from the detection of anti-malware applications. Packer will compress and obfuscate the payload so that anti-malware applications will fail to detect the malware with static and signature-based analyses. The malware will unpack the actual payload with a defined algorithm made by the developer. Many algorithms in the wild can be used to pack the payload
Persistence
The malware that has infected the host will always try to persist their host’s presence even after the machine rebooted or user logoff. There are many ways that malware will tamper to persist, such as using the registry autorun
Path to start up folder
C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp
C:\Users\Username\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\
Startup
Registry Path for start up
HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
Registry RUN
HKLM\Software\Microsoft\Windows\CurrentVersion\Run
HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnce
HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnceEx
HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
Communication
Malware infects the host will usually connect back to the malware creator (C2, CnC, C2C). This connection is intended for many things; one is to exfiltrate the data from the machine back to the malware creator or retrieve new command to do the following action. Usually, they will use encrypted channel such as SSH, SSL, TOR to hide their communication from the network detection
Propagation
Besides infecting one host and getting the highest privilege in the host, The malware would also intents to spread to some other machine to gather more foothold in the network. It could use vulnerability found in the system or network and exploit it to copy itself to the other host.
Armoring
The malware creator will defend its code from the detection of anti-malware software such as antivirus, EDR, Sandbox, and many other products. Usually, when the malware is run in a machine and finds anti-malware present in its environment, it will exhibit benign activities to avoid detection. It would also detect malware analysis tools such as debuggers, IDA, Procmon, Process Hacker, and many other devices.
Stealth
The malware will need to hide its presence in the host or infected machine to avoid detecting plain sight or event anti-malware software. Stealth mechanisms can range from simple techniques like altering file properties that make it hidden to more complex techniques like infecting other clean programs on the system, code injection, process hollowing, and rootkits