Hi Guys,
Today I am gonna share how to locate ransomware encryption process using process monitor and pin point the function address in IDA to help you easier to debug.
As we know the basic behaviour of ransomware is encrypting the content of the file within its privilege range by reading and creating new file and at the end will remove the original file. With this behaviour we can use process monitor privided by sysinternal to pin point the address in IDA
Simple Ransomware
I wrote a simple code that mimic the behaviour of ransomware (read file, encrypt content and write file) to make our tutorial simpler
#include <iostream>
#include <fstream>
#include <string>
using namespace std;
void ReadFile() {
fstream newfile;
newfile.open("C:\\Temp\\file.txt", ios::in);
if (newfile.is_open()) {
string tp;
while (getline(newfile, tp)) {
cout << tp << "\n";
}
newfile.close();
}
}
void EncryptFile() {
cout << "Encrypting file here...." << endl;
cout << "Encrypting file here...." << endl;
cout << "Encrypting file here...." << endl;
cout << "Encrypting file here...." << endl;
cout << "Encrypting file here...." << endl;
cout << "Encrypting file here...." << endl;
}
void WriteFile() {
fstream newfile;
newfile.open("C:\\Temp\\file.txt", ios::out);
if (newfile.is_open())
{
newfile << "#$%#^$&%^%@#$%@#$%@%^@%^%FGHDGHGHDFH#%$#%@#$%@#$ \n";
newfile.close();
}
}
int main() {
string test;
cout << "Rio Ransomware" << endl;
ReadFile();
EncryptFile();
WriteFile();
cout << "Rio Finish ..." << endl;
cin >> test;
return 0;
}
As we see above the of the C++ code that I call 3 function ReadFile, EncryptFile, WriteFile in squence. Lets compile it with name MyRansom.exe
Process Monitor
Lets prepare the process monitor and setup the filter so that only our apps being monitored. Lets run process monitor
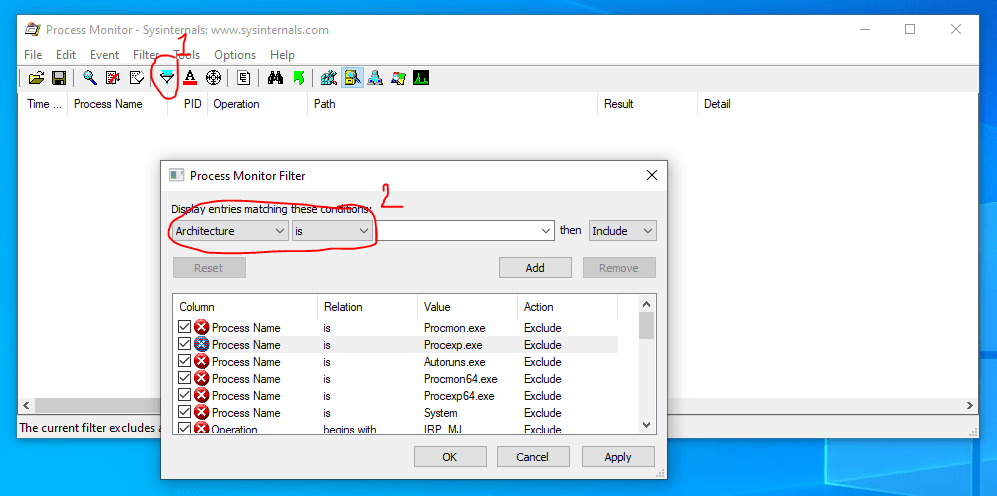
Press filter and input our application name with Process name containts MyRansom and press Add

when this is ready then you can start trigger the application by double clicking MyRansom console apps. Process monitor will start gathering all information of our application like below
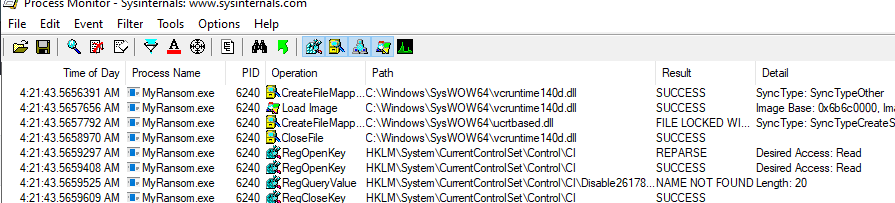
The above is a list of all the activities captured from the begining of the application triggered untill it exited the process. Now as we know this is a ransomware then what we should find in the operation is where the process start reading files from the disk and write it back to the disk.
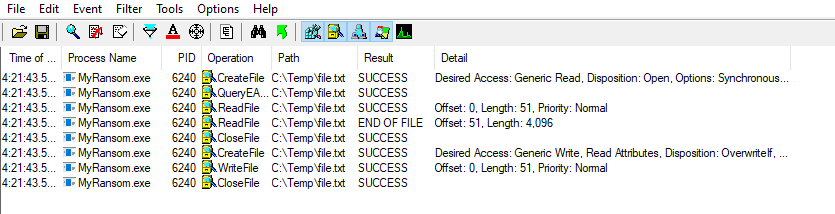
if we scroll down then we will find that the process will call ReadFile, WriteFile in among its opeation
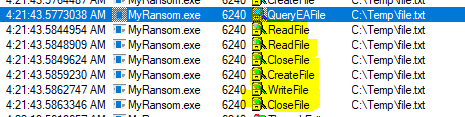
lets focus our analyses here because we know that based our sequence of function call in our code there will encryption in between of FileRead and FileWrite. We can now add filter so that the list will be shrinked to only that operation with specific path with below

The Function Address
Now lets find the address of the function. We can select one of the operation. I will select the read function and check the stack to get the address
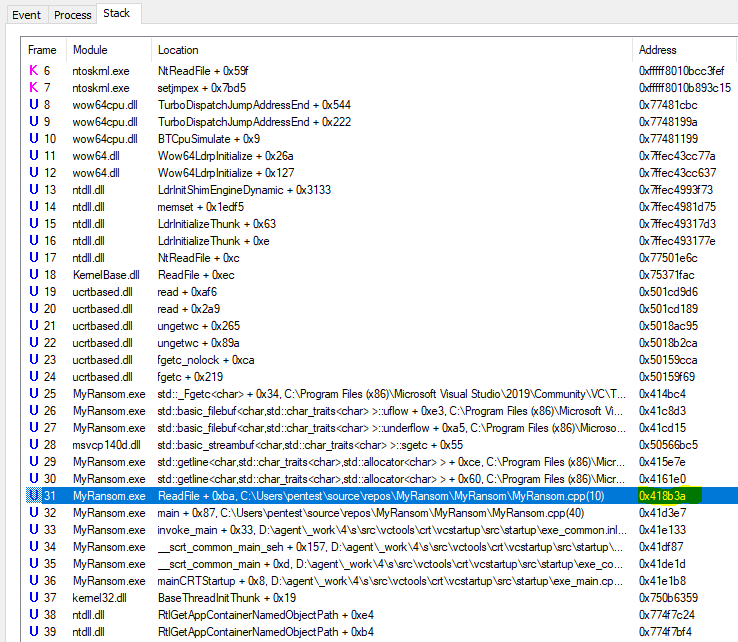
I will try to find the readfile that triggered from our main process as higlighted above. We can see that the ReadFile address is 0x418b3a
Hunt the Address
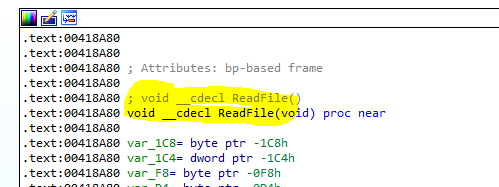
Now we can open our IDA to findout what is actually happening in that address 0x418b3a. You can press G in IDA to jump to the specified address and press OK


If we look where this code occurs is inside the ReadFile function. Let trace back this function in order to find out where the Encryption function being called.
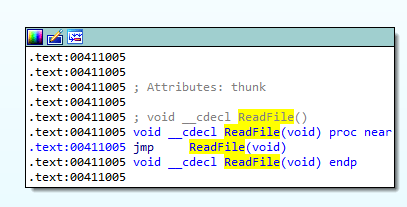
We can browse back by pressing ‘x‘
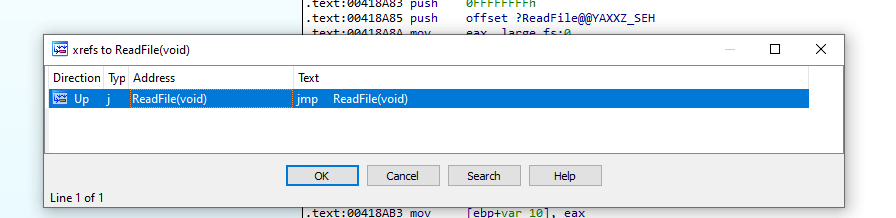
We found the call wrapper. We can press ‘x‘ again to go up again

Now we are arrived at main function where we can see the sequence of our function call
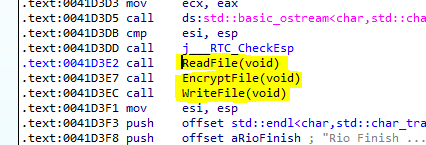
Finaly we found the encryption function being called here. Let see what is the encryption does here
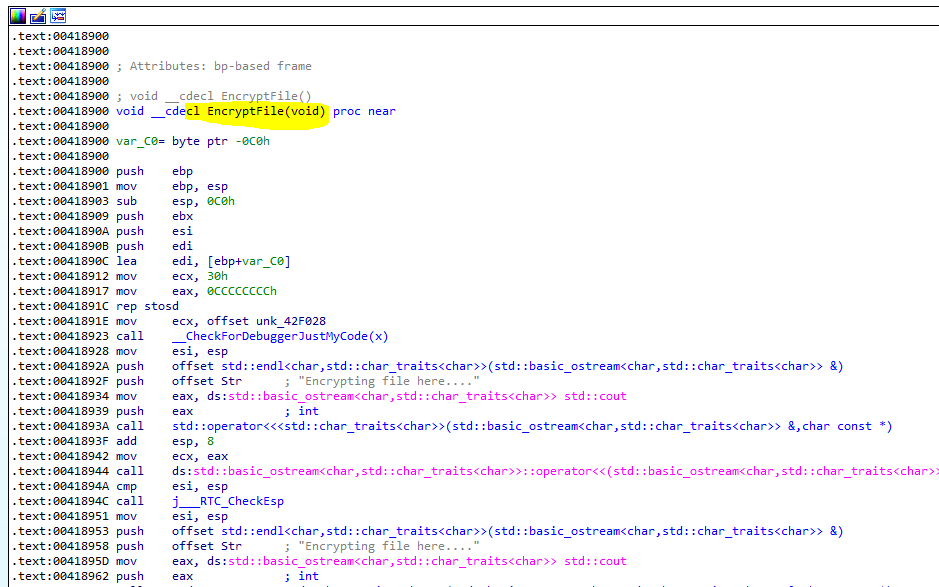
This is the code where the encryption happens. To make the code easier to be understood then IDA provide a handy tool to see the Pseudocode by pressing the F5 in the function
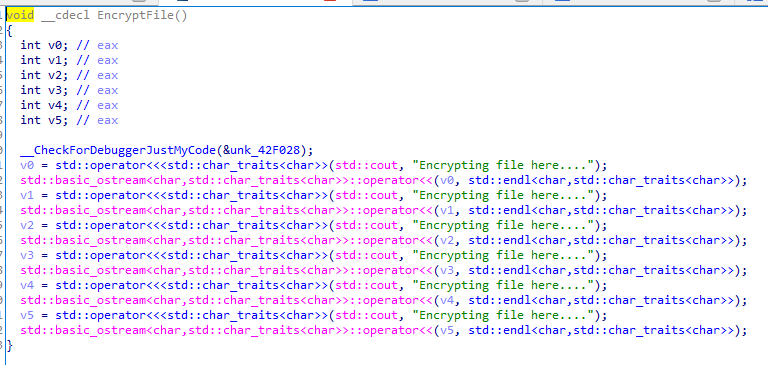
Ok .. we see that it only print out Ecrypting file here …. that match the original C++ code
That is all for the the tutorial to find out where the ransomware encryption function call.