Hi Guys,
I want to share a feature in IDA that help you to do static analyses more easy. I have an application that will decrypt a string loaded from data section memory in the PE. We know that it is quite hard to static analyses where some data only available during debugging such as decryption of string.
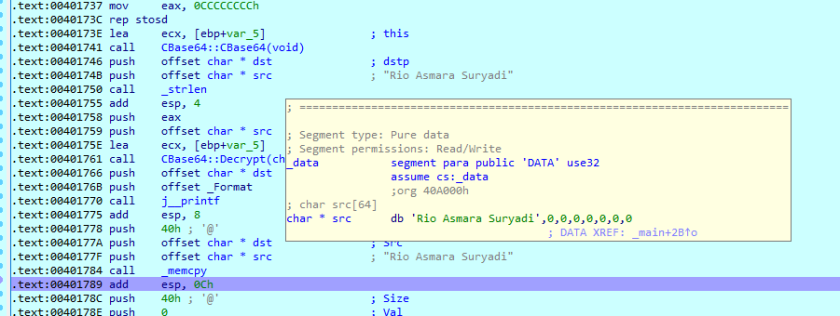
I made a simple application that will decrypt a string during runtime. Since the decrypted string will only available during runtime then it is hard to do static analyses such as code below. all string still in the encrypted form
Let see the original c codes
#include "stdafx.h"
#include "stdio.h"
#include "stdlib.h"
#include "string.h"
#include "Base64_RC4.h"
char src[64] = { 'U','m','l','v','I','E','F','z','b','W','F','y','Y','S','B','T','d','X','J','5','Y','W','R','p' };
char dst[64];
void main()
{
CBase64 base64;
base64.Decrypt(src,strlen(src),dst);
printf("Decoded string: %s\n",dst);
memcpy(src, dst, 64);
memset(dst, 0, sizeof(dst));
memset(src, 0, sizeof(src));
getchar();
}
We can see there the variable dst will be filled in with the decrypted string from the src variable and later the result in dst will be copied back to src using mempcy function.
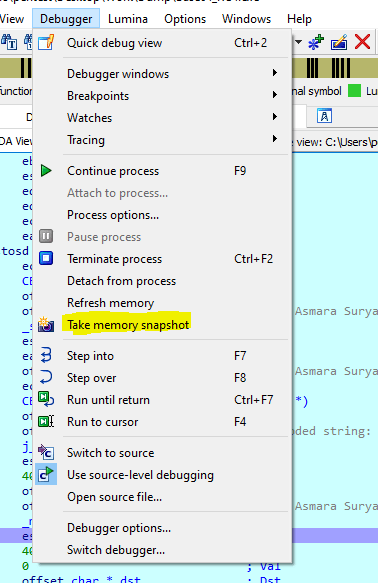
There is a functionality in IDA in order to take snapshot of the memory during debuggin mode.
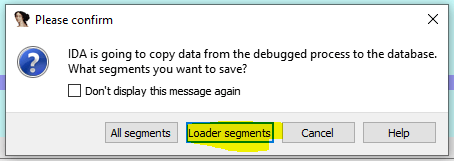
This command copies the contents of the process memory to the database. It is available during a debugging session. The memory contents will be copied to the database. The user may specify that only the segments with the ‘loader’ attribute will be saved in the database.
The segments with the loader attribute are created by the input file loader and usually contain information from the input file. However, in some cases (like attaching to an existing process), there will not be any loader segments because the input file was not loaded by IDA.
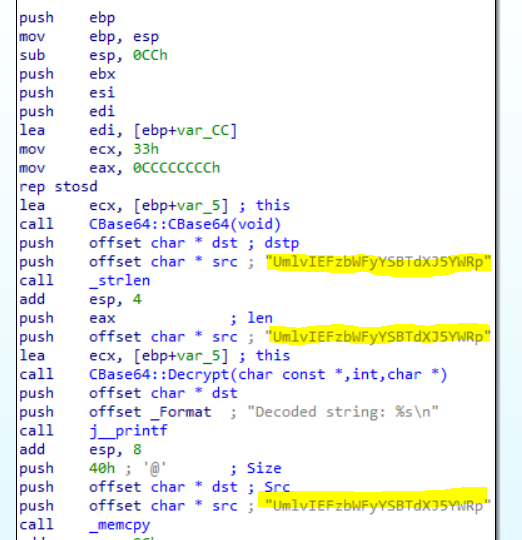
Ok now lets do the snapshot. We can identify the code that does the decyption in the assembly code as yellow highlighted below.
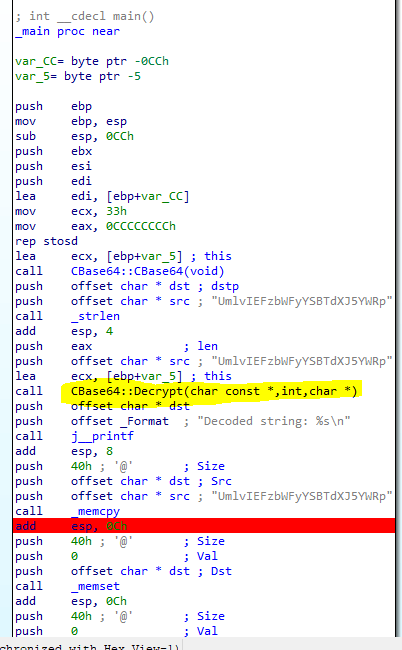
We can see that the above code after the decryption has been called we realize that the decrypted string will be copied back to the source memory address with the call memcpy.
Before mempcy src variable still has decrypted value

After memcpy src variable has been overwritten with the decrypted value
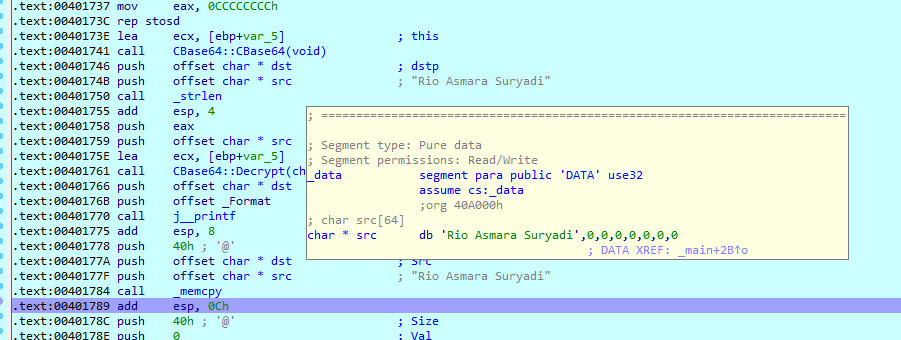
In order to do memory snapshot, the application should be in the state of paused with break point. So i put the break point just after the memcpy call.
Here is the steps
- Run the application with the debug mode after you set the break point
- Go to Debugger –> Take memory snapshot
- Select Loader segments
- After the process done and select File –> Save
- Then you can stop the debugging and continue with static analyses
Now, we can see the different here, although we are in the static mode we can see the string just like it has been decrypted

Now the data segment is just like it has been decrypted
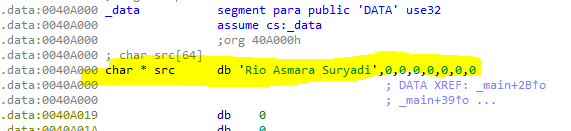
So with that string available for static analyses then it is easier for us to dig dive the code.