Hi Everyone,
We meet again after stop writting about 1 week, I stop writting because of my laptop was broken so that I could not do some research.
Today I am going to discuss about kerberoasting but from i am not going to discuss from the hacking perspective but I would discuss from the perspective of active directory perspective
Kerberoasting itself has been one of the most abused active directory configuration in order to gain privileges during read teaming activities. So basically what is kerberoasting ?
Kerberoasting
Kerberoasting is basically an attack that abuse the existence of windows account with SPN (Service Principle Name). SPN is used by the KDC to map between service that user want to access with the underlaying account (e.g HTTP/rio.corp = AppService1 ) so that KDC is able to encrypt the service ticket with the correct account’s hash. The adversaries will use the Ticket Granting Service (TGS) to get the password of the service by cracking it off-line
If you have access to the KDC (Domain Controller), you can list out all service that mapped to an account by using this below command
C:\Users\Administrator>setspn -l AppService1
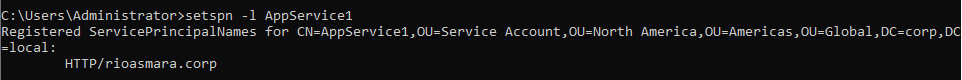
Or, With the advanced Features enabled, You can view the properties of the AD Object in the section of Attribute Editor to see where this account mapped to
Ticket Granting Service (TGS)
As we know that whenever an account want to access service, It needs to present the TGT to the KDC along with the destination service that it wants to access in order for this to get the TGS. KDC will generate one complete TGS and send it back to the initiator where half of its portion will be used by user and the other half will be sent to the target member service server.
Log Security Event Generated ID = 4769
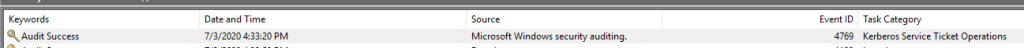
Sample windows security event log
A Kerberos service ticket was requested.
Account Information:
Account Name: test@CORP.LOCAL
Account Domain: CORP.LOCAL
Logon GUID: {f46ae56d-c311-908c-03f8-e0e95d99e9ef}
Service Information:
Service Name: AppService1
Service ID: CORP\AppService1
Network Information:
Client Address: ::ffff:192.168.100.128
Client Port: 49976
Additional Information:
Ticket Options: 0x40800010
Ticket Encryption Type: 0x17
Failure Code: 0x0
Transited Services: -
1st portion consist of Users Detail, Session Key (Match with 2nd portion)
2nd portion consist of validity time, Session Key (Match with 1st portion)
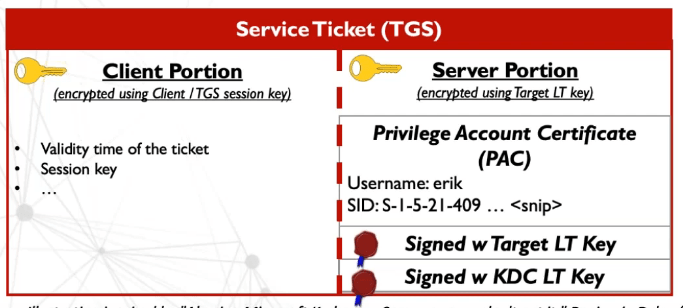
The first portion of the TGS that is sent to the member server will contain the account information called PAC (Privilege Attribute Certificate). This TGS is signed by the service hash (Password Hash) and KRBTGT hash
What is PAC ?
The Privileged Attribute Certificate (PAC) is an extension to Kerberos tickets that contains useful information about a user’s privileges. This information is added to Kerberos tickets by a domain controller when a user authenticates within an Active Directory domain. When users use their Kerberos tickets to authenticate to other systems, the PAC can be read and used to determine their level of privileges without reaching out to the domain controller to query for that information (more on that to follow)
The attack synopsis
- The attacker will scan the Active Directory for the account with SPN values set
- Once the list of target accounts is obtained, the attacker will send request service ticket from the AD using SPN values
- Using Mimikatz, the attacker then extract the service tickets to the memory and saves the information to the file
- Once the the ticket stored saved to the disk, the attacker passes them to off-line cracking script that will run dictionary attack of password as NTLM hashes.
Create SPN in Active directory
in order for you to create SPN in active directory, the easiest way is to do it via the console by using the command setspn
C:\Users\Administrator>setspn -S HTTP/rioasmara.corp AppService1
Checking domain DC=corp,DC=local
Registering ServicePrincipalNames for CN=AppService1,OU=Service Account,OU=North America,OU=Americas,OU=Global,DC=corp,DC=local
HTTP/rioasmara.corp
Updated object
setspn –s command that creates and SPN and uses the –s switch to make sure a duplicate SPN does not exist.
HTTP/rioasmara.corp is the service that you want to assign, HTTP is the service class that you want the service attached on and specifially when the user access url domain rioamara.corp
Sample of other service class available
| Service Classes (Types) | Service Classes Description |
| MSSQLSvc | SQL Server Database Engine |
| MSOLAPSvc.3 | SQL Server Analysis Services |
| MSOLAPDisco | SQL Server Analysis Services Discovery Service |
| MSSQLDisco | SQL Server Browser |
| HTTP | IIS service |
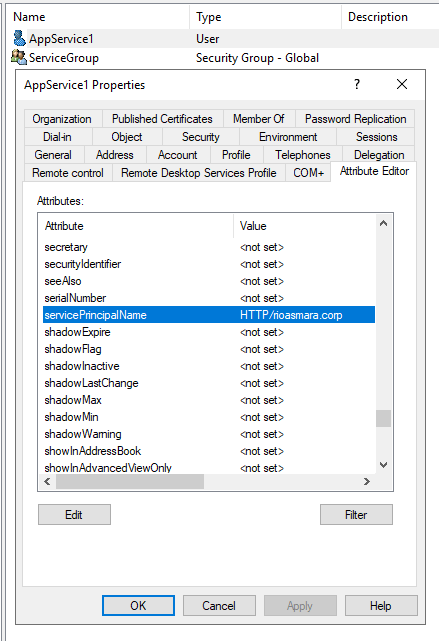
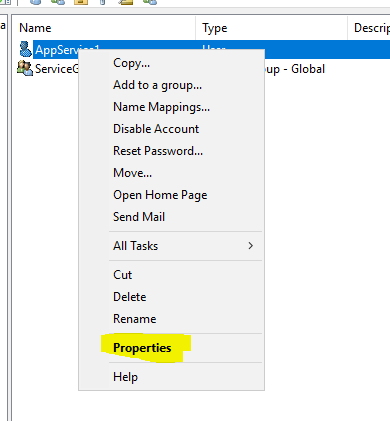
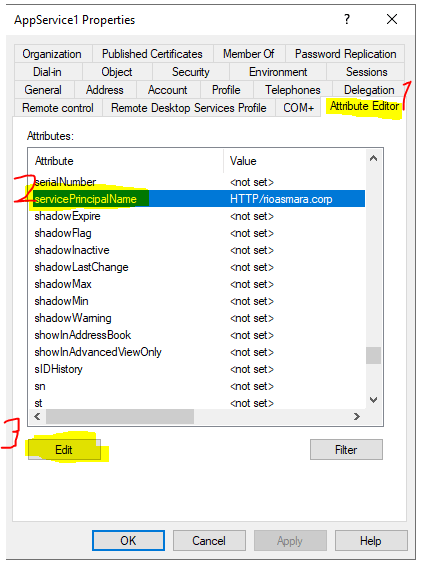
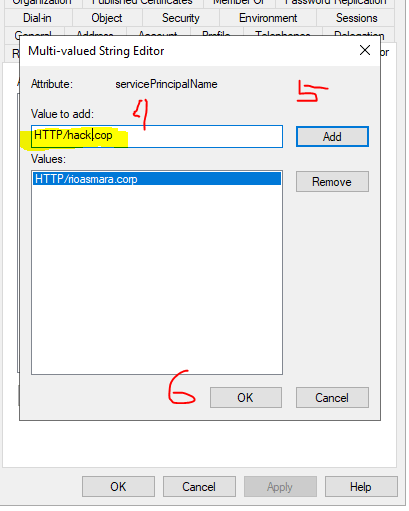
You can also set the SPN from the GUI by following this steps
Right click and go to properties of an account that you want to set the SPN
Got the tabe Attribute Editor –> servicePrincipalName –> Edit
Add the service –> press Add –> Press Ok
Ok I think that is all for today about SPN …