Hi everyone,
Today I am going to write a little walk-through of a box from hack the box lab. I am going to explain the step by step of the box called Silo.
Overall the walk-through will be divided into three phases which are hacking the oracle database web exploitation and priv escalation.
Let start, As usual we should do recon. The best tools for recon is nmap. You can use the command below to do nmap
nmap -sS -sV -sC -vvv 10.10.10.82
-sS = SYN scan
-sC = banner grabbing
-sV = check the version of target service
-vvv = be verbose
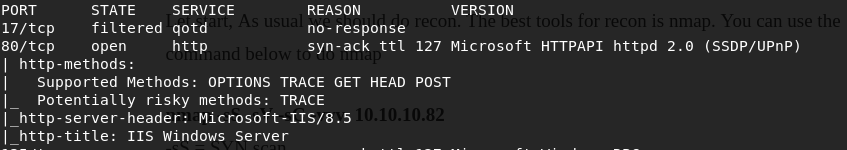

we can see that there is open port for oracle database 11.2 and port 80 for http. We have two attack surface that can be used to exploit. I will use an application called ODAT (Oracle Database Attacking Tool) to help me on analyzing the oracle database service. this tools can be download from https://github.com/quentinhardy/odat

first lets brute force for the SID that is available in the server. We use the command below
./odat.py sidguesser -s 10.10.10.82 -p 1521

We found 2 instances of database XE and XEXDB. Now the next step is to brute force the username and password. We can use odat to brute force with this command below
./odat.py passwordguesser -s 10.10.10.82 -p 1521 -d XE
But do not forget to provide the username and password wordlist in the directory accounts within odat directory. The username and password shall be formatted username/password just like below

we finally found the username and password of XE instance. here below the picture

the username is scott and password is tiger.
OK that is all about recon and enumeration phase of the Penetration Test Cycle. I will continue to the exploitation phase in the next blog.
