Hi All,
I would like to share a bit regarding the basic information about extracting malware from the dump memory using a powerful application called volatility. I called it basic knowledge because I want to give you some ideas on how to analyze things in the memory. However, there are a lot of other application that can help you to investigate running application in the memory in real-time such as Falcon Crowdstrike that enable detailed memory forensic that is able to visualize event to network graph.
In this tutorial, the scenario is we have a malware at Windows XP that is running silently and infect the host and start to connect back to it CnC server. You can download the memory dump for this exercise from http://files.sempersecurus.org/dumps/cridex_memdump.zip
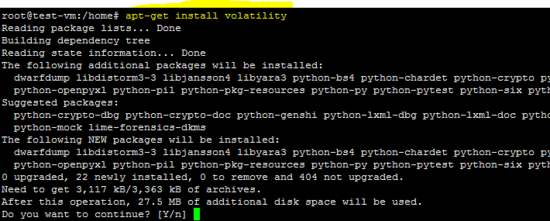
First of all, you must have installed volatility application. I am using kali linux for this but you can actually just install using the step below (I took the picture from internet)
OK now volatility is ready. Now you start analyzing the memory dump file that you downloaded but do not forget to unzip it first
As you know that information in the memory is formatted in different way that depend on the operating system. So the first step is to find the suitable profile of memory dump that we want to analyze. we can use the command
volatility -f cridex.vmem imageinfo

We can see from the information above that volatility suggest that it suit with profile WinXPSP2x86 or WinXPSP3x86. We can now further drill down our malware hunting.
The next step is to find out what application is running at the that time the dump was taken. we can use the command
volatility –profile WinXPSP2x86 -f cridex.vmem pstree

another way to find out what applications are running by using this command
volatility –profile WinXPSP2x86 -f cridex.vmem pslist

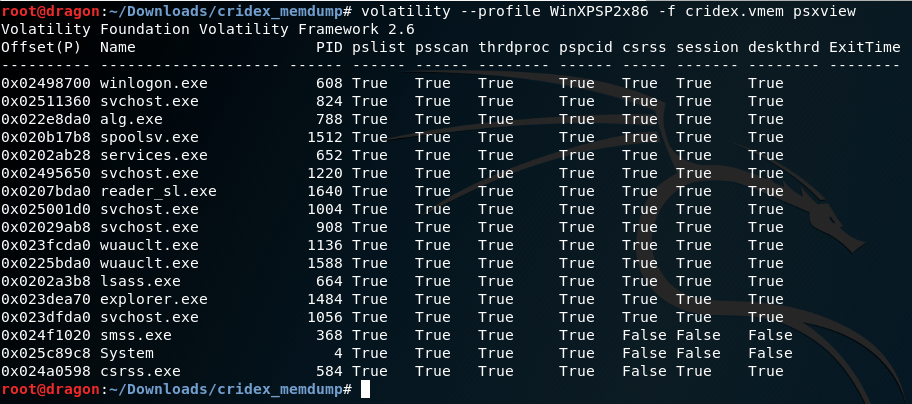
from the application list above we can see that there is an application that is suspicious with PID 1640 reader_sl.exe with the parent process is explorer.exe PID 1484 which mean that reader_sl.exe was triggered by explorer application.
it is also important that you check the application that tries to hide it self from the task list. You can use. if you see any process that is false in the pslist and psscan then you can assume this is the malware
volatility –profile WinXPSP2x86 -f cridex.vmem psxview
the next step to check is the connection event, usually malware will create connection back to the its CnC (Command and Control) in order to do its next task or sending the information to it for any information that the malware successfully extract from the host. We can use the command below to scan the connection
volatility –profile WinXPSP2x86 -f cridex.vmem connscan

We can see that the above PID 1484 established a connection to internet IP 41.168.5.140 port 8080 and IP 125.19.103.198 port 8080 that we are not sure what IP it is.
We can also further check the connection by using the socket plugin to analyze the connection status Listening for connection. You can use below command
volatility –profile WinXPSP2x86 -f cridex.vmem sockets

From the picture above we can also see that PID 1484 (explorer, the parent of reader_sl.exe) is actually waiting for TCP connection that accepting from any IP.
the next step is to analyze on how an application is triggered in the command line and what is the parameter and path of the application. We can use the command as below
volatility –profile WinXPSP2x86 -f cridex.vmem cmdline
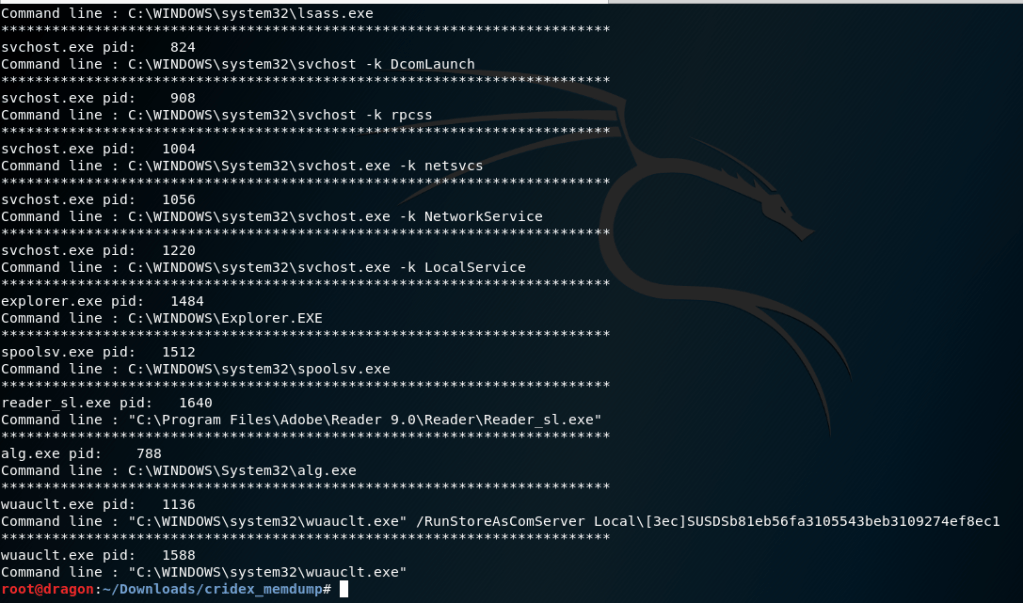
we can see that reader_sl.exe that we suspect as the malware is actually installed in “C:\Program Files\Adobe\Reader 9.0\Reader\Reader_sl.exe” and triggered without any parameter. we can compare the application that is triggered with parameter such as Command line : C:\WINDOWS\system32\svchost.exe -k LocalService
The next step that is to analyze the binary of Reader_sl.exe. We can extract that specific binary from the memory dump using this command
volatility –profile WinXPSP2x86 -f cridex.vmem procdump -p 1640 –dump-dir .
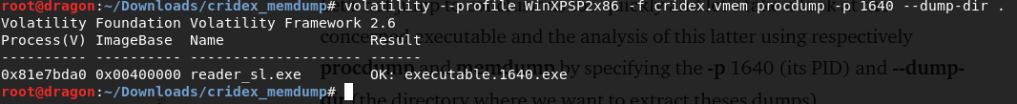
with the above command, volatitility extract the binary from the memory and name this binary with executable.1640.exe. By this binary then you can start analyzing it. You can upload it to virustotal.com to check what kind of malware it is
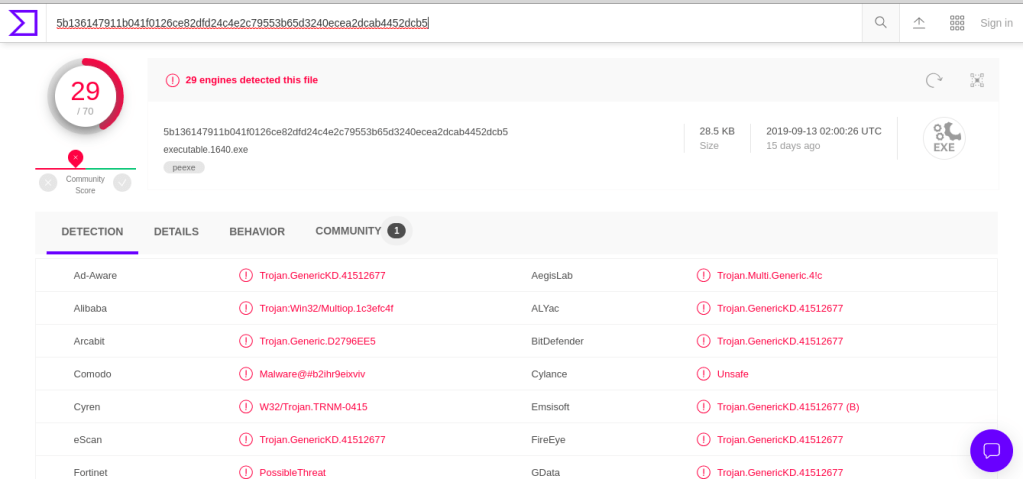
We can now can conclude that the binary is malware so that the first question of malware triage about existency of malware can be answered. But do not stop here. Triage malware is not just stop here. You should know what this malware is trying to do or what is the objective and how the malware could install it self in the host or how the malware could come to your premises.
Next thing to do is to also dump the memory area that the malware use so that we can narrow down our search for this particular malware only. We can use this below command to extract
volatility –profile WinXPSP2x86 -f cridex.vmem memdump -p 1640 –dump-dir .
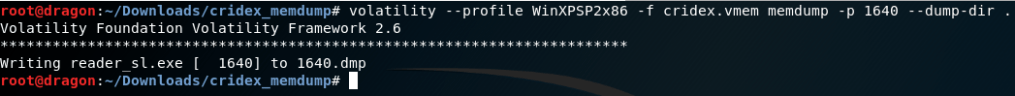
OK now we have the memory dump of the malware. We know that this malware is trying to connect to a server so that we need to find what kind of protocol it uses to connect to internet (CnC at 41.168.5.140 ). We can use find string toward the memory dump
strings 1640.dmp | grep -Fi “41.168.5.140” -C 5
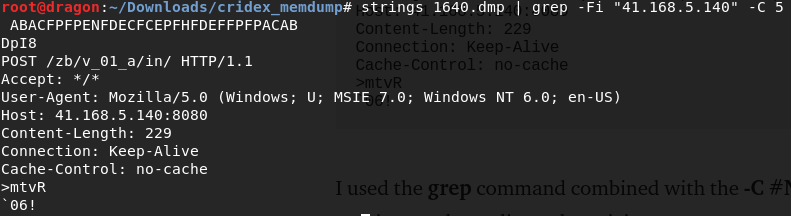
so that we can conclude that the communication with the CnC is using http protol. So by this we know that our perimeter protection is not able to detect the signature. We can see it is posting some data to the url http://41.168.5.140/zb/v_01_a/in/
Lets try to find the zb/v_01_a/in/ and see what will happen.
strings 1640.dmp | grep -Fi “zb/v_01_a/in/” -C 5

Ohhh we found another CnC IP 188.40.0.138 at port 8080
Lets go further to drill the memory, perhaps we can find some more information
strings 1640.dmp | less

we can see that this malware has a collection of domain that it tries to infect.
So we can conclude for our malware triage points as below
- Is the malware exist in our perimeter ? Yes, the malware exist within our perimeter
- How this malware come into the perimeter ? It is exploiting the pdf reader installation so high possibility of non updated PDF Reader get exploited via Phishing campaign
- What is the objective of this malware ? it is leaking data
OK that is all for today. I will make detail malware analyses of this malware using static and dynamic analyses using IDA tools.