Hi everyone,
I would like to follow up of getting the root access to billubox with 2nd alternative, As you know that during our scanning phase, we might get more than one way of getting the box due to some vulnerability found. In this case I would like to exploit the vulnerability of malicious file upload vulnerability.
The attack vector of this technique are below
- Uploading the malicious file by exploiting malicious file upload
- Searching for local file inclusion
- Gettting the server shell
- Enumerate the linux to find OS level vulnerability to get escalation
- Exploit
- Exploitation validation
Lets do the above attack vector
As we have analysed the upload code functionality at my previous post that it can be baypassed by manipulating the file magic number that the file upload validation falsely detect the correct file. To exploit this vulnerability we need to login to the application to have the full functionaility.
Searching the login
In the first page of the application, We need to supply username and password in order to login but for sure we don’t have it yet. But in our last exploitation using LFI we found the credential of db connection that is being used by the application where the username is billu and pasword b0x_billu. By this username we are allowed to login to the database and browse any data inside.
Login to the database
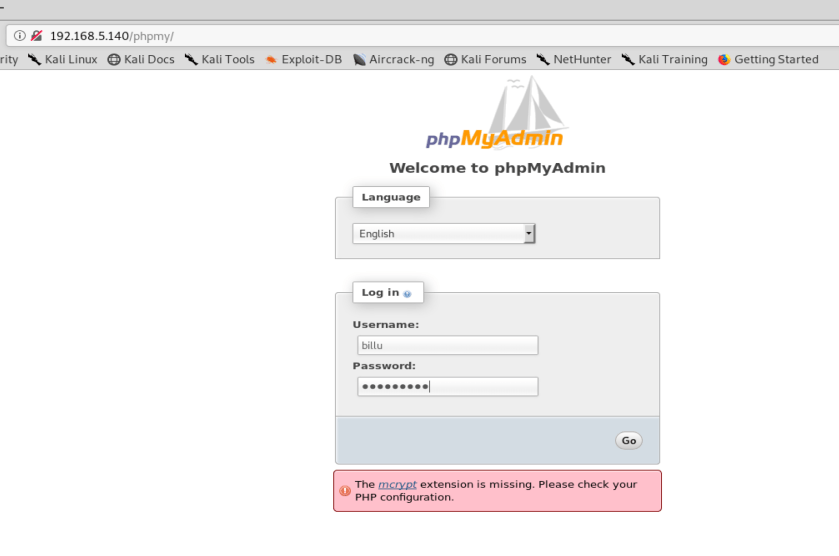
During our scanning phase that we also found there is a phpmyadmin page that can be accessed at http://192.168.5.140/phpmy. Let go login into it
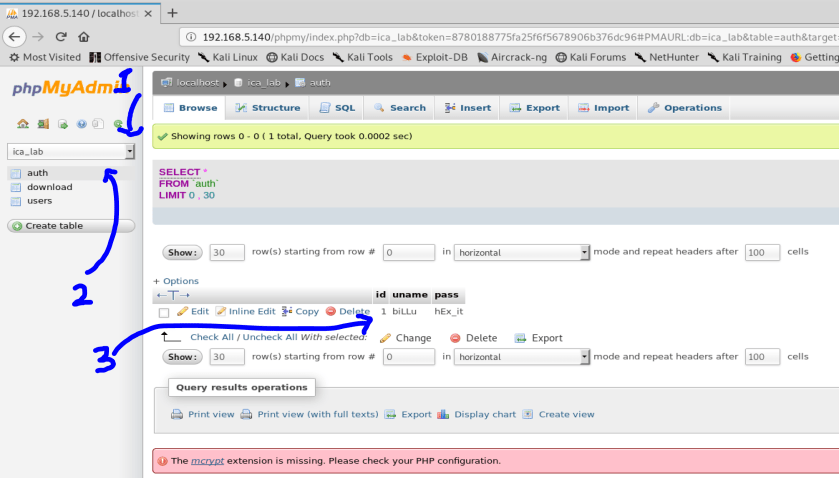
After you are logged in, lets browse information,
- Go to the database that the application use
- Lets directly go to the auth table (just by instinct that the password is saved there)
- Yeah we finally found the username biLLu and pasword hEx_it for the application
Login to the application

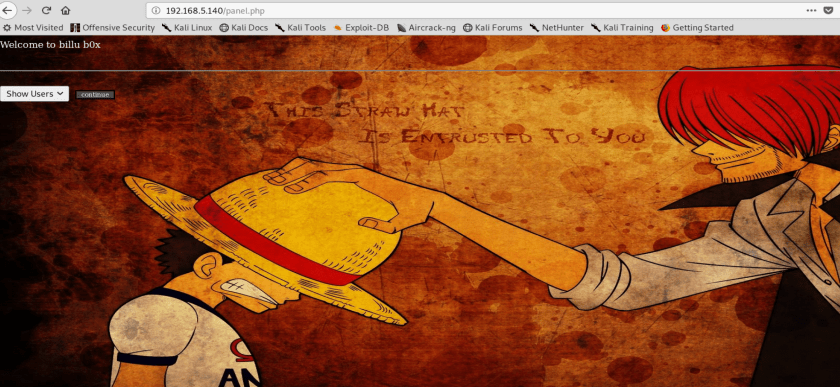
Uploading the malicious file
in order to bypass the image validation, we need to create a file image that has php embedded in the body, You can use the below sample to create it

Lets upload this file to the server using the new user functionality
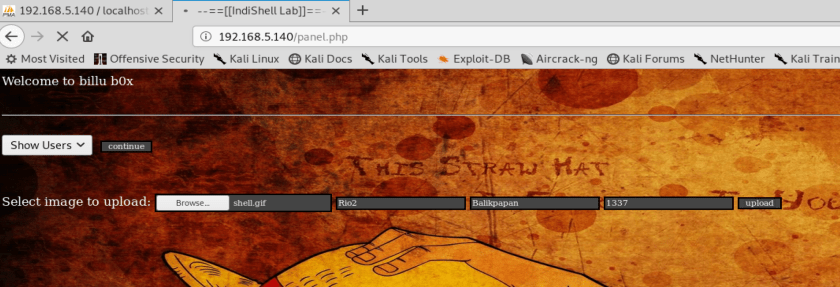
You can see from the above picture, we are uploading the shell.gif to the server using the uploading function. I am also catching the submit data to my burpsuite

we can see from the above picture, Our gif file payload is the same that we did using xxd in the console.
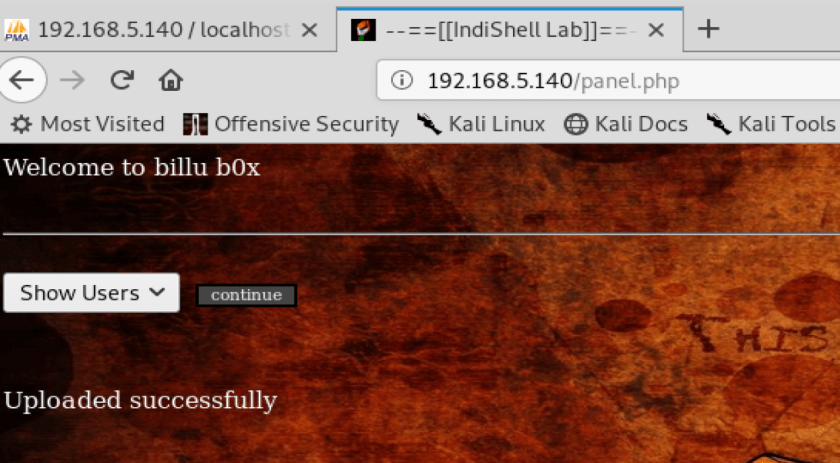
We successfully bypass the image validation code.
Finding how to load the shell.gif file
We have successfully uploaded the file and we can verify it in the uploaded_images directory see the higligted file below.

the shell.gif need to be loaded somehow, it is actually php file where you can pass remote command injection to variable cmd.
in order to find the load function, You need analyze the variable passed to the application that perhaps contain the file inclusion vulnerability, or if you are at this stage that you can analyze the page code by using the LFI that we found in early phase.
Lets analyze the code, What we need to find the in the code is php function that include the file like include();
PHP: include(), include_once(), require(), require_once(), fopen(), readfile(), ...
JSP/Servlet: java.io.File(), java.io.FileReader(), ...
ASP.net: include file, include virtual, ..
this is the description of the function
Files are included based on the file path given or, if none is given, the include_path specified. If the file isn’t found in the include_path,include will finally check in the calling script’s own directory and the current working directory before failing. The include construct will emit awarning if it cannot find a file; this is different behavior from require, which will emit a fatal error.
If a path is defined — whether absolute (starting with a drive letter or \ on Windows, or / on Unix/Linux systems) or relative to the current directory (starting with . or ..) — the include_path will be ignored altogether. For example, if a filename begins with ../, the parser will look in the parent directory to find the requested file.
after look around to some files, I found the function is being used in the panel.php
if(isset($_POST['continue']))
{
$dir=getcwd();
$choice=str_replace('./','',$_POST['load']);
if($choice==='add')
{
include($dir.'/'.$choice.'.php');
die();
}
if($choice==='show')
{
include($dir.'/'.$choice.'.php');
die();
}
else
{
include($dir.'/'.$_POST['load']);
}
}
based on the code above, this file shall be called and should pass the parameter load but don’t forget in order to do the inclusion, we need to manipulate the path since it firstly check the the current directory
Definition and Usage
The getcwd() function returns the current working directory.
Syntax
getcwd();
At the panel file, when we want to show the user list it will call it self but passing a parameter load as the parameter to include which file either to load the user list or add user.
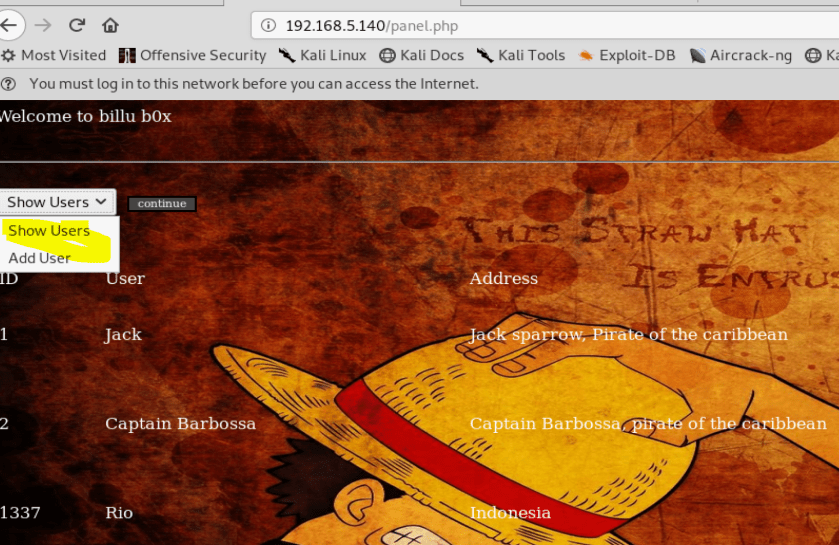
If we choose the show users from the drop down menu and press submit, it will post the request header like the below with parameter load and continue
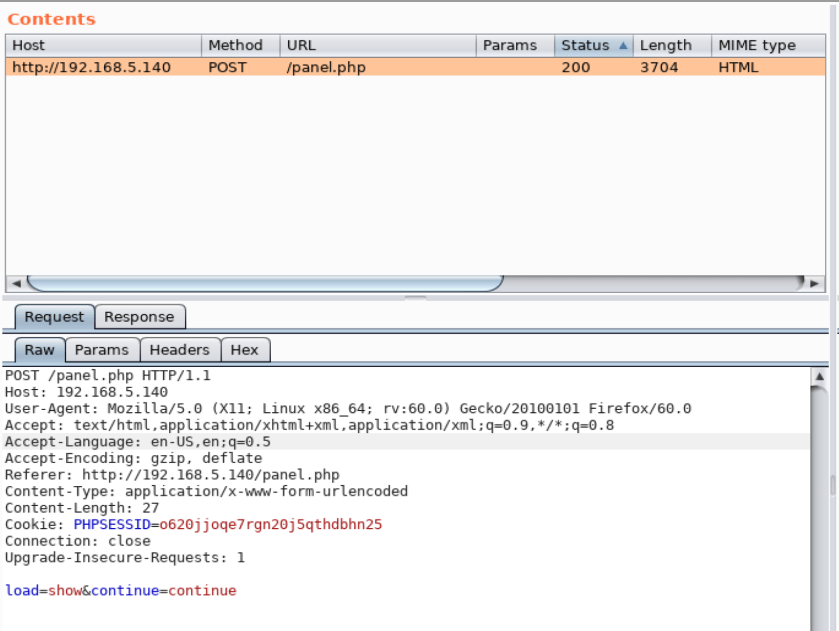
if we see the code above, it contain 3 condition which are
- if the load = add then it will load add.php at current directory. it will append .php right after the value from the parameter
- if the load = show then it will load show.php as the same as above
- if the load is other then the above, it will load what ever the file defined in the load variable
The 3rd operation could be exploited since we can post any file with specified path. This 3rd condition is the one that we can use to load the shell.gif file like the below image
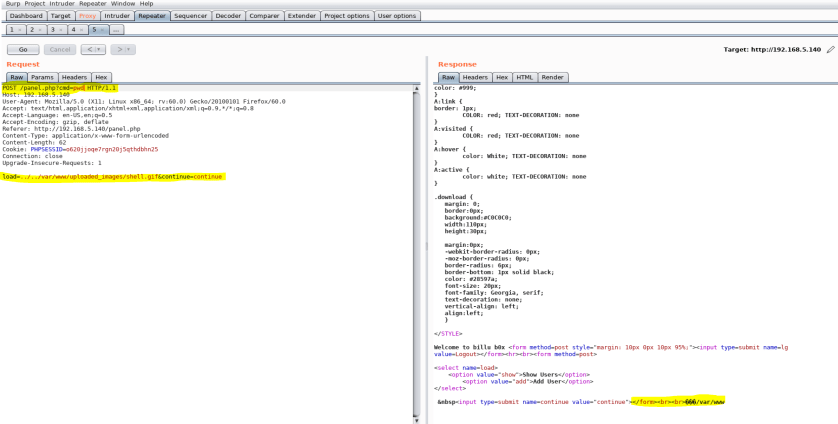
as the image show above then now we can load the shell.gif perfectly with the command injection. We can now go further to get the reverse shell.
Lesson learn
- Non restricted file inclusion on the application code lead the hacker to load malicious file on the server. Tips to defend this attack is to white list the page that could be loaded so that hacker would never be able to load other file otherwise they can override the code of white listed file :). The other way to defend it is to validate the path of to be loaded page.
- Password in the database is not hashed or it is stored in flat text, It is fatal. Hacker could be very easy to exploit certain bug e.g SQL Injection to view your database’s content. Password in the database should be stored in the form of hash or encrypted. You should use strong encryption or create your own algorithm before storing it in the database. I am not suggesting just to store an MD5 hash password in the database since it is very easy to trace, There are alot of websites providing MD5 databases hash which lead to the original text such as https://hashkiller.co.uk/md5-decrypter.aspx this would make the job of retrieving the original password in just a second.
I will post the escallation process in the final post. Thanks