Hi Guys,
I am finally back after busy with my relocation back to home town. Today, I would like to share how to get the windows handles. Why this is important to understand windows handles because all the windows API that we interact with will require us to provide handles
Windows Handles
An object is a data structure that represents a system resource, such as a file, thread, or graphic image. An application cannot directly access object data or the system resource that an object represents. Instead, an application must obtain an object handle, which it can use to examine or modify the system resource. Each handle has an entry in an internally maintained table. These entries contain the addresses of the resources and the means to identify the resource type
What windows handles for?
The system uses objects and handles to regulate access to system resources for two main reasons. First, the use of objects ensures that Microsoft can update system functionality, as long as the original object interface is maintained. When subsequent versions of the system are released, you can use the updated object with little or no additional work.
Malware Analysis
Getting the handles information from the malware is very important because it will give you more detailed information that enables the analyst to have more idea of what the malware does during its operation
So let’s take a scenario if you are analyzing malware that interacts with windows API that writes the file to the disk, and you want to know the path and what is the content

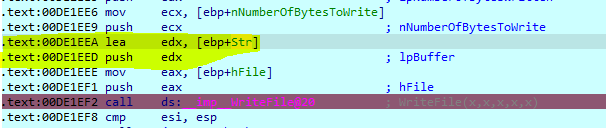
What you need to do is to put breakpoint each time the WriteFile API is called. It would be best if you found the X reference so that you can set the breakpoint at the correct line
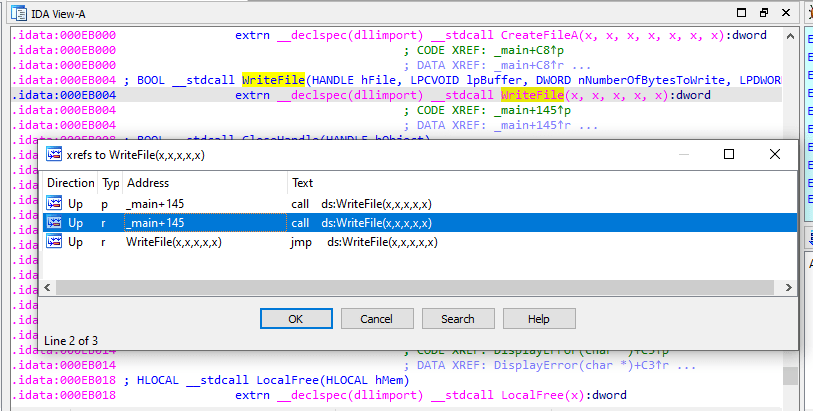
Call from the code and set the breakpoint here
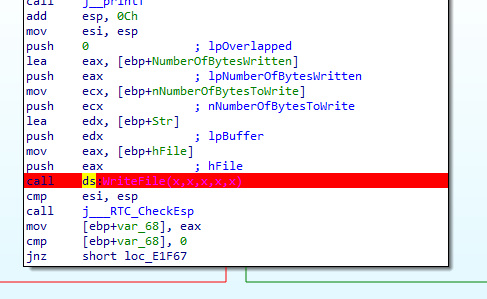
Lets Debug the application and wait until the break point hit

Now the breakpoint is hit. Now we need to find what is the handle information can be gathered. If we look at the Writefile function call below, the handle will be in the first parameter
BOOL WriteFile(
HANDLE hFile,
LPCVOID lpBuffer,
DWORD nNumberOfBytesToWrite,
LPDWORD lpNumberOfBytesWritten,
LPOVERLAPPED lpOverlapped
);
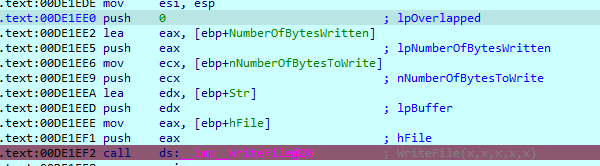
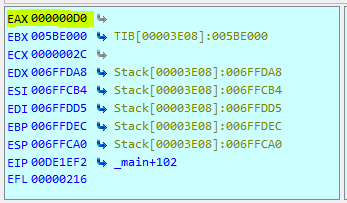
Below is the function call and the parameter that is pushed to the stack. We can now that the first parameter is handle and will be pushed to the stack in the last sequence which is in EAX
We can see that the handle ID is [00D0]
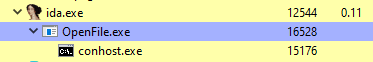
To make the life easier to find the handles detail we can find it using Process Hacker by double clicking on the program where in this case is OpenFile.exe
Go to handles tab and look for the same handles ID
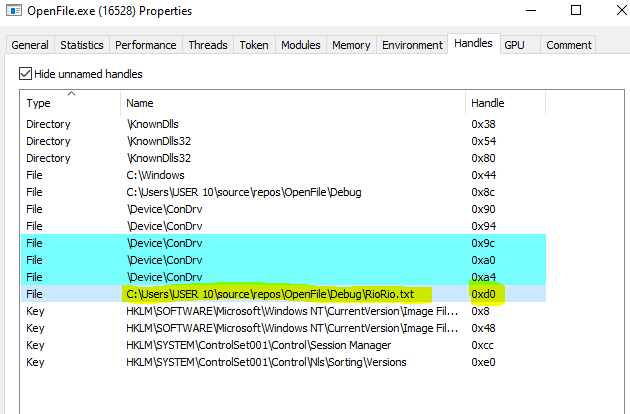
Now we can see that the file being written to the the disk is on that path (C:\Users\USER 10\source\repos\OpenFile\Debug\RioRio.txt). Based on that information we can know that the malware will write a file into that specific path for its own purpose
What is the content ?
in order to see what is the content. We can look for the 2nd parameter being passed to the WriteFile function. The content will be passed in the second parameter as buffer. So it will be pushed in the second last from the WriteFile call.
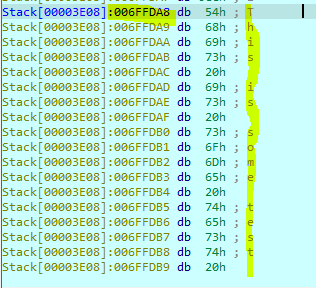
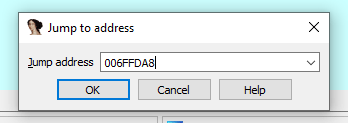
We can take a look on the stack. The 2nd value is pointing to 006FFDA8

We can jump to that address to verify the value
We can see that the message “This is some test” char array first address.