Hello hello,
I want to share about HTTP traffic analyzer, which is useful when you are analyzing malware. For sure modern malware will do some stages to deliver its core functionality to evade detection.
There is a handy tool that allows you to analyze HTTP traffic quickly. It will become the proxy of the entire system to catch all request and response from the server when it is running.
Let see the UI. Request history

All the necessary information are shown by default in sequence so that you see the what request is being made in time history.
When you execute malware intentionally for analysis purposes, you need to focuse your eyes to that malware activity. We can easily filter out the information based on the application that triggers the request by selecting the Quick Filters Application

When you select based on the application and then all the information in every section of the application will be directly updated
Traffic Statistic
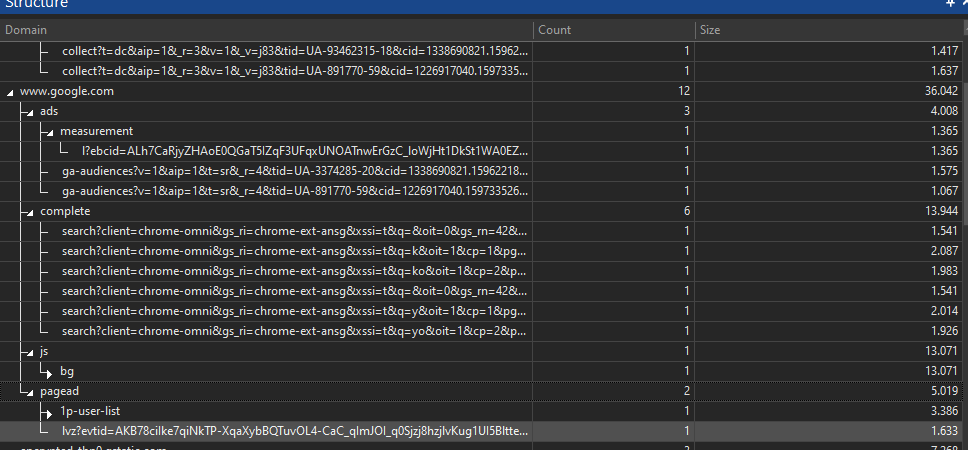
After we can filter out the information based on the application name, we need to know where this application is communicating. We can use the statistic window by following these steps. Go to Performance menu and select Domains

Domain Statistic Window will give you the unique domain that the application you selected is contacting to. You can start to profile the domain with external Threat Intel information to find the bad domain

Besides that, we can also see how many times the application contacted each domain so that we can have an idea perhaps how many times the malware is downloading the payload to evade the detection, including the records of the difference variable GET or POST to that domain.
Most malware will download their payload in the second or third stage to evade the malware detection and sandbox. If you wished to find out the payload that has been downloaded, you could see it in the request and response detail window.
First you need to select the HTTP request that might interest you then analyze the server response

We can see that the above is Chrome downloaded a content with type application/msi lets analyze the request and response
Request Detail
We can see that Chrome download an application called putty-64bit-0.74-installer.msi from host the.earth.li

We can now analyze further what is the server responded to this request in the Response Detail window
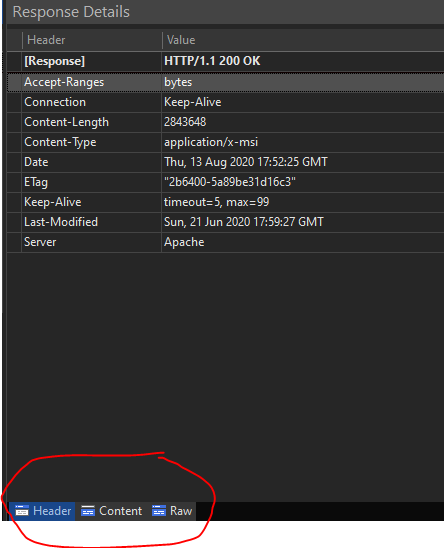
Extracting Payload
The server responded OK with status 200 at Specific date. We see that there are three subsection that we can use for analyzing the detail. We can also see the content that server delivered to the client in the content tab
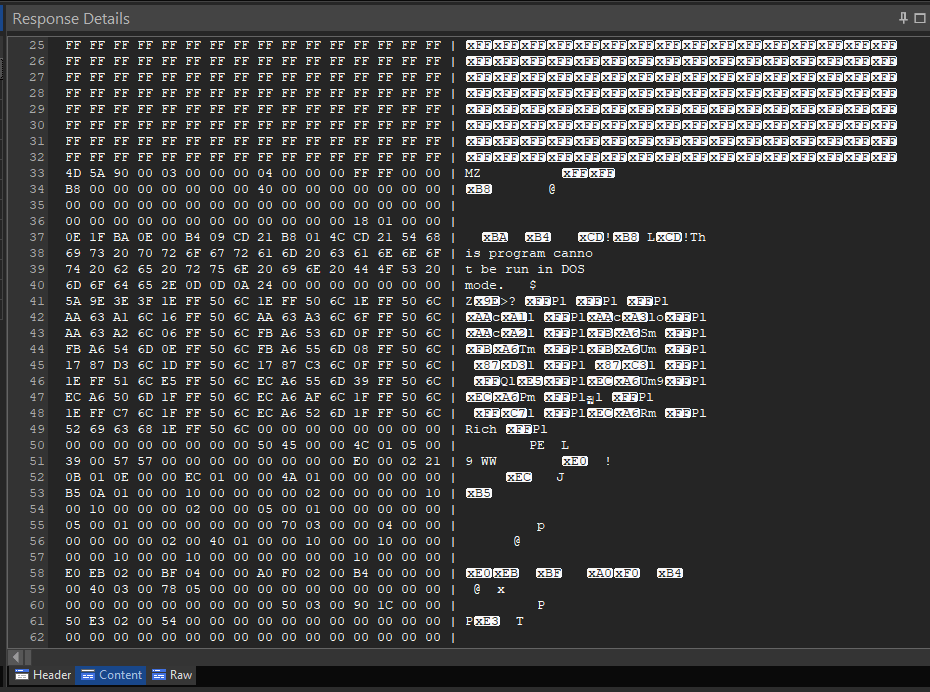
Interesting that as malware analyst, we can download this payload directly from here by right clicking in the window and choose save content


Lets try to execute the payload that we extracted from the http response

The HTTP Debugger is very halpful to gain a quick analysis to see what is going on in the system wide OS. It gives you a very easy installation and configuration to start the process.
