Hi Friends,
Welcome to my blog again, Thank you for reading my blog. i would like to share a tutorial to analyze a .NET binary with DNSPY. I got the binary from Hack the box cascade that i would like to discuss about.
So during the penetration test for cascade box, you can finally get the shell to the box via evil-winrm at a particular stage. You will find an SQL lite database and binary. I assume that the binary will use the database for any of its operations.
if you open the database then there is an interesting account and password that you need to escalate yourself but the password is encoded base64 and ecrypted.

I believe the binary that use this database will do the decryption for this, so we can check the decryption string from the apps
So lets dig the binary
You can open the binary using dnspy
- File
- Open
- Select the exe that you would like to open

After the file opened then we can either go to the main function by expanding the tree like below

when you click the MainModule, the main function will be directly decompiled so that you can see the original code of C# .NET.
As part of the penetration test, We need to analyze what this binary is actually doing during its opeartion that maybe could benefit us to gather more information or escalate ourself
DNSpy is equiped with static and debugging capability that enable you even to go deeper for dynamic analyses.
Let start with static analyses first.

Decryption algorithm being used is AES with 128 block size

Based on the above facts, we found a variable called password to contain the decryption result as a return from the decryption function. There are two ways to decrypt the password: decrypting with online tools or running the application in debug mode.
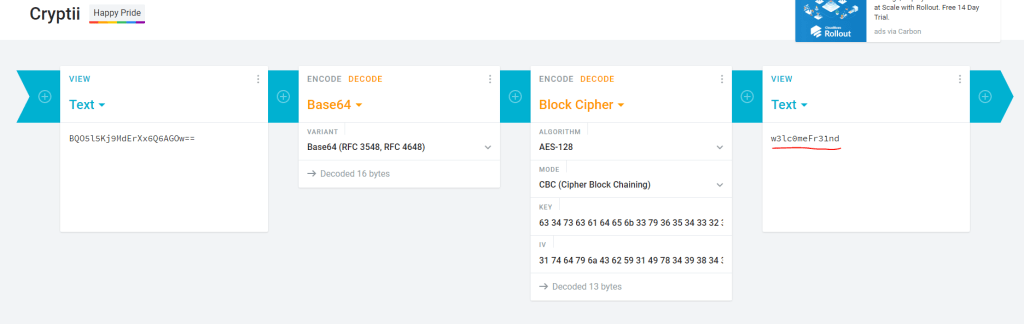
Lets run with online tools by providing the information we got from the code to this URL https://cryptii.com/
Dynamic Analyses
We can see that we have successfully decrypted the password from the database. We can also do the decryption by doing the dynamic analysis using debug mode. we can set a breakpoint at the decryption call like below by pressing F9 at the line

After we set the breakpoint, then we can run the debug. Run the application in debugging and wait until the breakpoint is hit. We can see all the variable has been set.
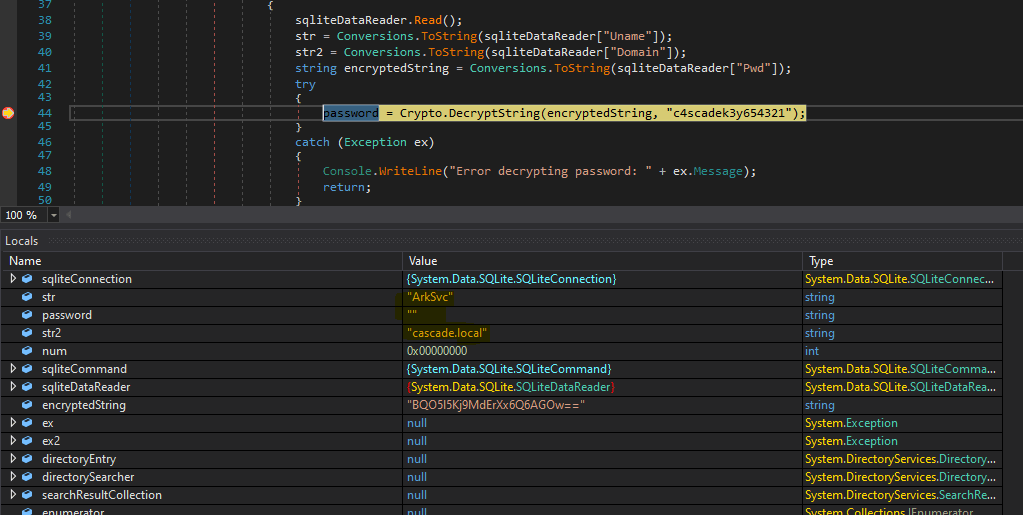
in the above the variable str = ArkSvc, str2 = cascade.local but the password is still null. We know that the Decryption function has not been invoked due to the breakpoint. Let step over the by pressing F10. Now the decryption function has been invoked and result of decryption is stored in the variable password. Now password has value = “w3lc0meFr31nd\0\0\0”

We have also successfully decrypted the password by doing the dynamic analyses.
Further analysis
There is a functionality that I would like to share that I usually use during static analyses. This function reminds me to Xref to and Xref from in IDA. It helps to analyze the function call and uses. Let’s explore the DecryptString function. You can right-click on the function name and select Analyze

We can see that DecryptString function is only be used or called by MainModule. We can also see that DecryptString uses a bunch of function
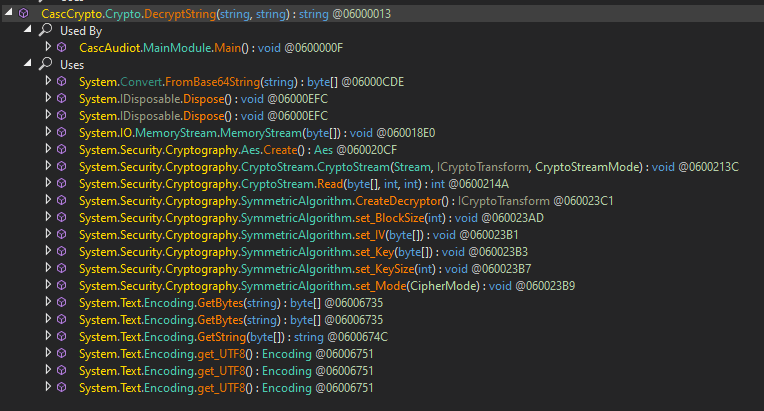
With analyze functionality will give you idea how this function work in the application.

Loved reading this thhank you