Hi Everyone,
It is like a week i did not post any article. Today I am going to share a simple way to enumerate web applications with Burpsuite intruder. There is no rocket science here. It is just basic knowledge on how to use burpsuite functionalities that could help you to get the job done quickly
First, I am going to use the vulnerability of an application called manage engine service plus that allow the attacker to enumerate user of the application.
This is how we can find it. Please ensure that you have set the browser and burpsuite all work together.
Lets go. First when open the web page of the application you will be prompted with username and password in order to login to the application.
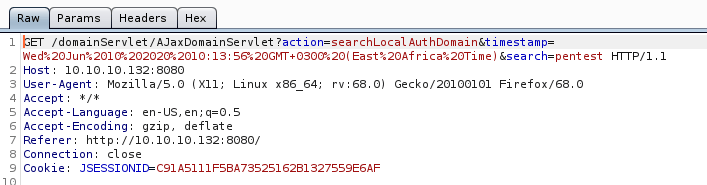
The application sends the username to the server for validation before you even press the login button. We can see at the back there is traffic captured in the burpsuite like this. Here I put user as pentest. The application sends a search request for the name pentest to the server
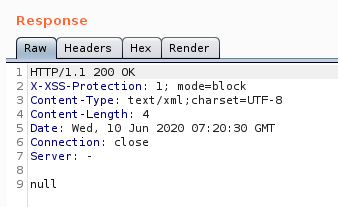
And the server will respond as below. The server will return with null value if the user is not found in the server.
With the above scenario, How do we automate the process so that we do not need to try one by one.
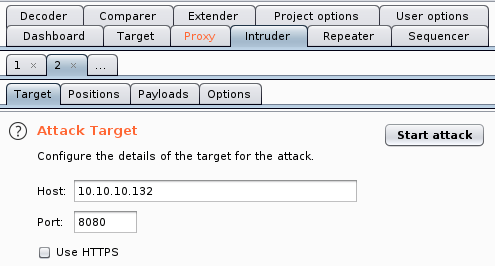
Lets do it. when you get the http GET request to the server like what i mentioned above, you can send it to the intruder for automation by pressing ctrl + i. And now you can go to intruder tab in burpsuite
The next step is to set where they payload will be automated. You need to go to position tab.

Burpsuite will automatically detect and highlight any possible position that can be automated for you. But in this case we only want to automate search variable. So, the next step is to press clear to remove the detection.

The next step is to highlight word “pentest” and press add. Burp will change the anotation from pentest to $pentest$.
The next step is to setup the payload. You need to go to payload tab
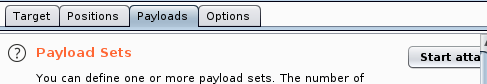
what you need to do in this tab is to set the payload for the burp to run the automation. So this payload will be read and put as a request to the server by changing the value $pentest$ that you have set in the position tab.
In this case, I would use simple dictionary attack. Here is the way I load the dictionary to the Burp

In the above screen, press load. Then you need to specify where is your dictionary placed in the disk.
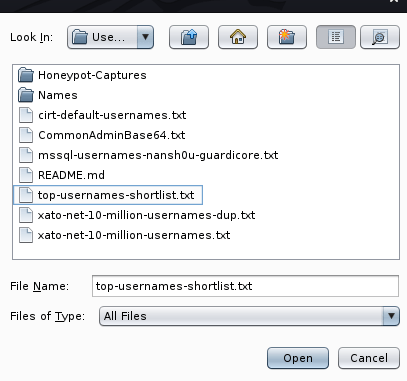
Press open after you selected the dictionary. Burp will load all the text within the text file you specified that will look like below
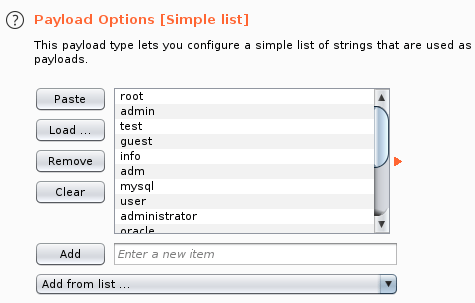
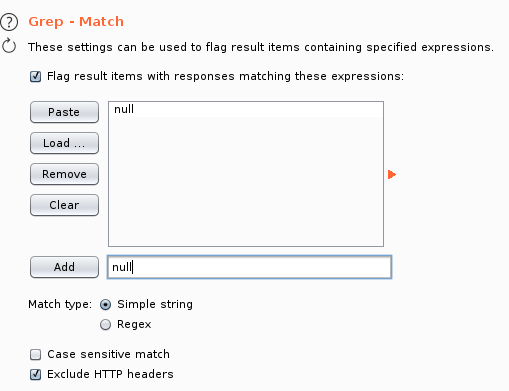
Then basically, you are ready to start the attack. But I encourage you to also set variable the options tab such as how many treads should burpsuite do to request the server at one time. There is one configuration that I highly recommend for you to set is to grep and flag the server respond in the below section
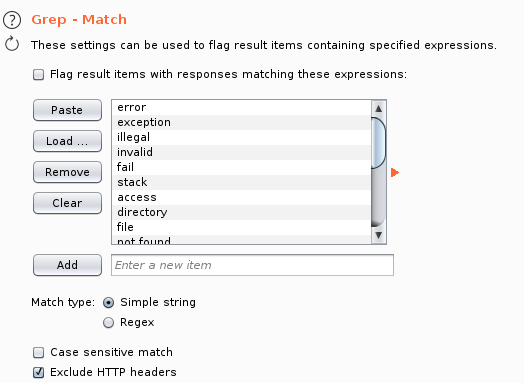
The above function will make your life easier to detect the server response. Remember that based on our analysis previously, the application will return null when it does not find the username in its database. So we can grep the null value and flag this for us.
First you need to press clear in order to remove all pre input value by Burp. You need to add new item ‘null’ in the field and press add like below
Now everything is set. You can start the attack by pressing the button start attack

A new windows will pop up that run the enumeration that send the payload to the server. After Burpsuite finished the enumeration. we can see the result in result tab.
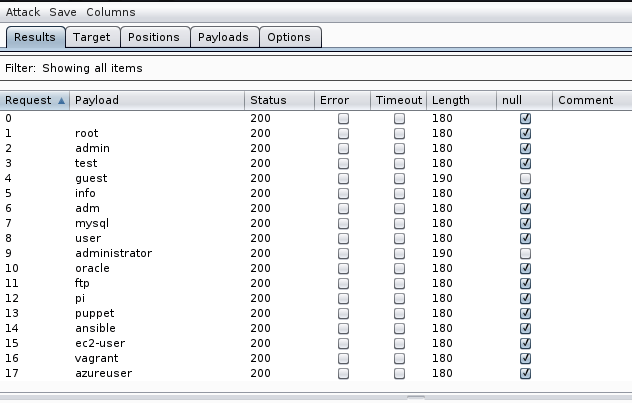
in the above screen you can see that there is a column call null. this column is telling us that actually burp flag the result that it find the null value in the server response.

In the null colum we can also find there is a line that is not tagged with null. it means that burpsuite does not find null value in the server response which is “Not in Domain”
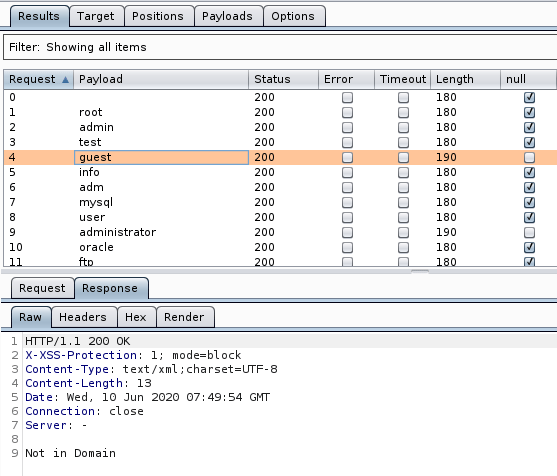
So with the tag is helping us to spot the difference between responses directly. So with this result, we can conclude that username guest and administrator are actually found in the database where we can use this information for further attack.
I don’t understand why you need to do this. Since a server always runs as root anyway and any code you inject into the backend will also be run as root, do you really need to know what users are on the system?
Hi Bro,
Thank you for reading my work.
There are two types of user, Application level or System level. They are running in the different context.
The enumertion that I described in the in the tutorial was about enumerating user at the web application level. I was not enumerating user at the system level.
You might correct that server service could be run as root or any lower level privilege user.