Hi All,
I would like to share a post related to buffer overflow, Why i pick this topic is because most critical vulnerability related to the operating system are still caused by this problem.
I would like to make this tutorial as easy as possible for the new learner who want to know about buffer overflow.
What basically make the buffer overflow become danger is because adversaries could ovewrite the return function of a stack to point to any other memory address which could be danger
Sample of application code that could lead to buffer overflow is like below
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
void showData(char * input){
char dest[50];
memcpy(dest, input, strlen(input));
printf("Print = %s\n", dest);
}
int main()
{
char input [1000];
gets(input);
showData(input);
return 0;
}
We can see that above, The user input is being copied to the another buffer that has different size where the original array (1000) is much larger to the destination buffer size (50).
Assembly level analysis
Buffer overflow is basically will impact to the stack and compromise the return address.
Lets analyze the normal stack when the user input the proper size of input
Payload AAAAAAAAAAAAAAAAAAAAAAAAABBBB (30 bytes)
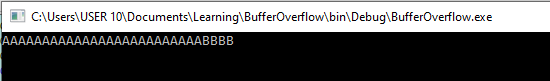
We can see that here is below the return address pushed to the stack. Now the return address is placed in the very top of the stack.
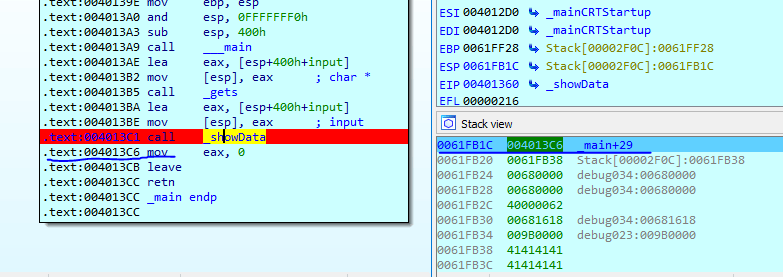
Let see analyse when the input has been copied to the new buffer. in the left picture below is the stack without the payload copied yet. But in the right is the stack with the payload copied after using the memcpy.
We can see the above return address of the stack is still good which point to the original address in the main function 004013C6. Now lets do overflow
I will use the same payload with much larger data
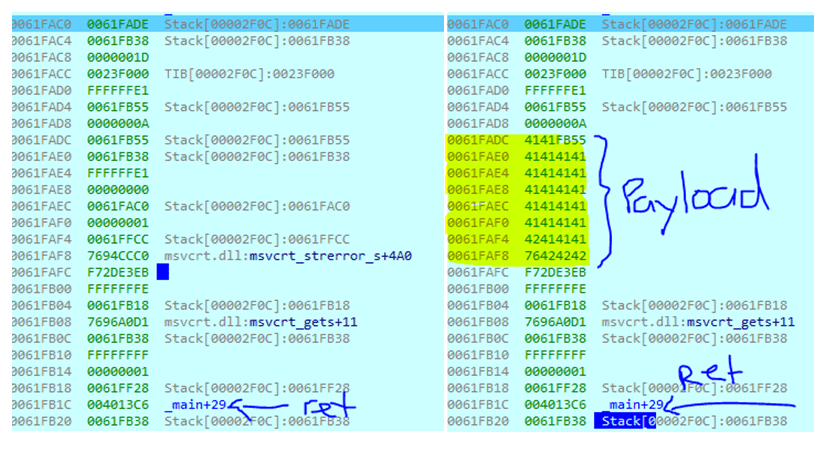
Payload AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABBBB (66 bytes)
We can see the below stack difference between my previous payload and second payload, with the bigger payload the overflow happen which is impacting the return address of stack which originally should point back to the main function 004013C6 but now the return address change to 42424242 which is our last 4 bytes of the payload (BBBB)
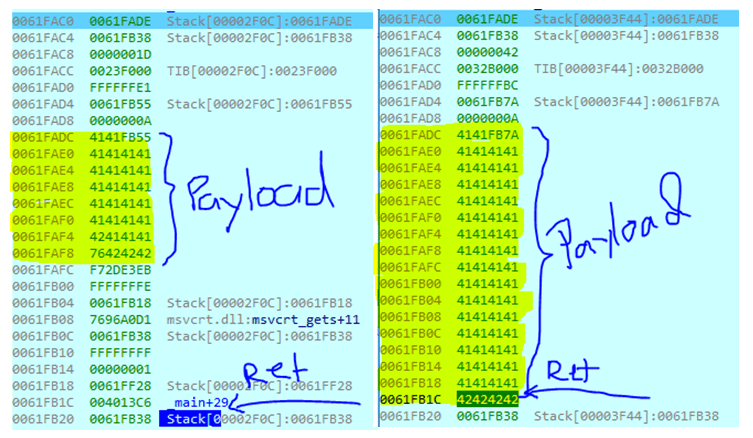
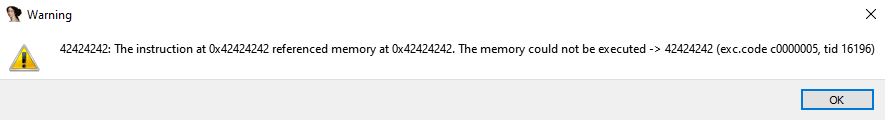
if we continue the debugging IDA will show the warning like below because memory address 0x42424242 does not exist when executing the return
with this vulnerability we can re-arrange the application flow by compromissing the return address of the stack to other address in the application.
Nice blog postt