Dear Friends,
Today, I am going to continue tutorial about the crack challenge. In the last post, We have discussed about the 5th condition. Next we will solve the next code and by reversing some code.

The next code that we can see above is all about looping. I divide the code into two parts. In the first part we can see that there is variable assignment mov [ebp+CharCollected_1], 0 it does mean that CharCollected_1 is being assigned 0 as the initial value. And also, the is another variable assignment with 0 that is mov [ebp+Iterator], 0 to initiat Iterator
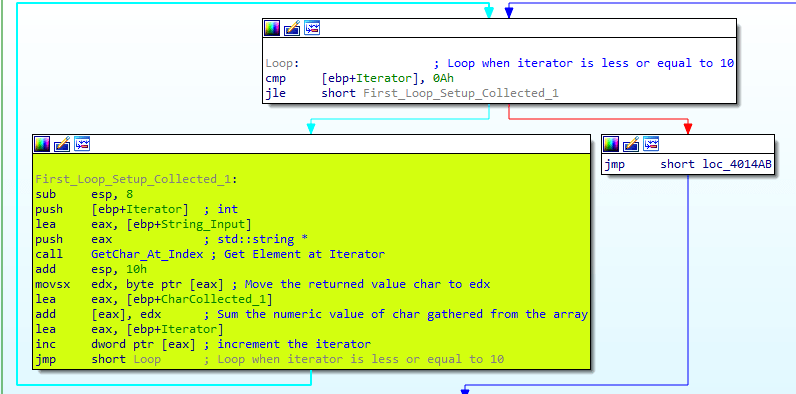
In the second part, We start the loop process. We can see that the iterator is being checked if the iterator is less than 0Ah which is 10 in decimal. You can click on the value and press ‘?’ to show the evaluate expression dialog.

So basically from the above code that the loop will finish 10 rounds where interator 0 to 9. the condition it self is cmp [ebp+Iterator], 0Ah followed by jle First_Loop_Setup_Collected_1. Comparison use jle (jump less equal) it instruct to jump if the iterator value is less than or equal to 0Ah (10)
Next we go into the loop where it is called loop body, I would like to split this loop body become 3 parts just like below

The first part of the loop body is process to get the element of the array based on the loop iterator. We can see that GetChar_At_Index will receive two parameters where the first parameter is the string array and the second part is index and returning the char at specified index
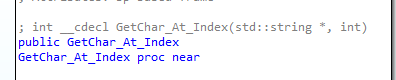
As usual, parameter will be passed to the function in reverse so that we can see in the code that push [ebp+Iterator] (passing index) is done prior push eax (passing array). The next code is GetChar_At_Index function is called
The second part of the loop body would process the returned value from the function, movsx edx, byte pointer [eax] is assigning the returned value of the function which is as default stored in eax to edx.
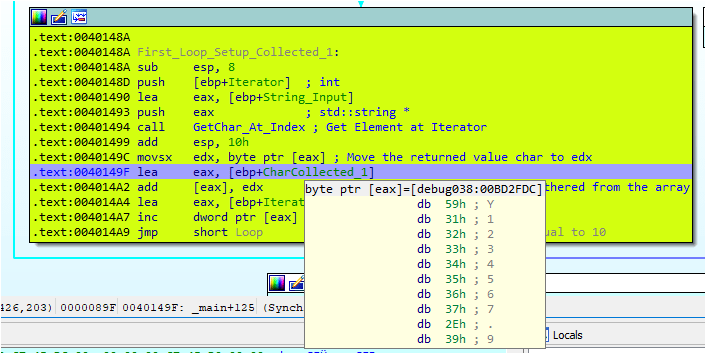
Below, we can see that now EDX is holding the value 59 which is the first decimal of first char Y.

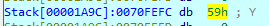
The next code is lea eax, [ebp+CharCollected_1]. This code instruction is assigning the memory reference of CharCollected_1 to eax so that eax can be used for process at next instruction. We can see that the CharCollected_1 is assigned memory address 0070FEFC
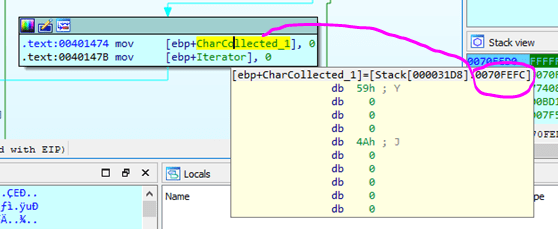
we can see right after lea eax, [ebp+CharCollected_1] then eax is holding the memory address of CharCollected_1 which is 0070FEFC. 0070FEFC is holding value 59h


The next code is add [eax], edx. This code will add the value in edx to the value in eax and store the result in EAX. We can see from below register that edx is holding value 31h (49) and EAX is holding value 59h = 89

After the add [eax], edx, eax will hold new value which is 89+ 49 = 138 which can be seen the new value in 0070FEFC or CharCollected_1 is 138

So the loop will actually sum up the input value gathered untill the loop finish 10 iteration
We input to the application as below

Y = 89 ( CharCollected_1 =89)
1 = 49 ( CharCollected_1 = 138)
2 = 50 ( CharCollected_1 = 188)
3 = 51 ( CharCollected_1 =239)
4 = 52 ( CharCollected_1 = 35) since the value can be stored is only 0-255 (256 char) the sum of 239 + 52 = 291 which overflow the capability of unsigned char which can only hold value 8 bits wide so that CharCollected_1 will recycle from 0 which point to 35 where the result of 291 – 256 = 35
5 = 53 ( CharCollected_1 = 88)
6 = 54 ( CharCollected_1 = 142)
7 = 55 ( CharCollected_1 = 197)
. = 46 ( CharCollected_1 = 243)
9=57 ( CharCollected_1 = 44) recycle due to 300 – 256 = 44
0=48 ( CharCollected_1 = 92)
Coming to the last part of the loop is lea eax, [ebp+Iterator]. This instruction is to load the effective memory address of Iterator to eax for further process. We can see the next process is inc dword ptr [eax] will add 1 to the value of iterator. This value is the loop indicator

OK, I think that is all for now. In the next post I will post about the next instruction of the challenge
