Dear Friends,
I would like write tutorial on how to do simple dynamic analyses with IDA. I will use the same executable like the previous post where we will do debugging on the first 3 condition or check
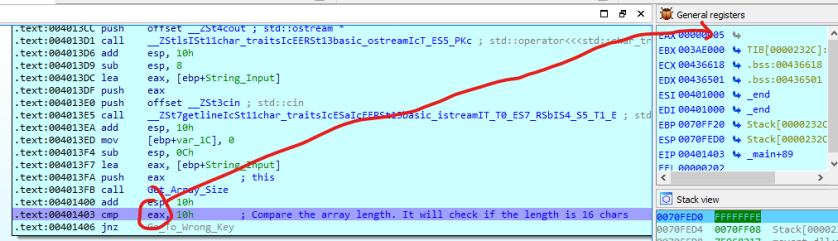
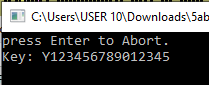
Lets go, first we have to set break point at the first check and run the application

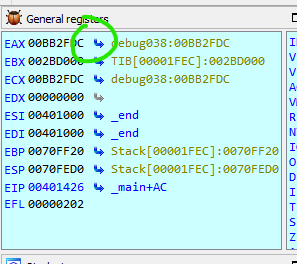
I only entered 5 char into the input. We can see that the Get_Array_Size return value that is stored in eax is equal to 5
Based on the condition that the application key shall be 16 chars so that with only 5 keys then the application will direct you to Go_To_Wrong_Key section
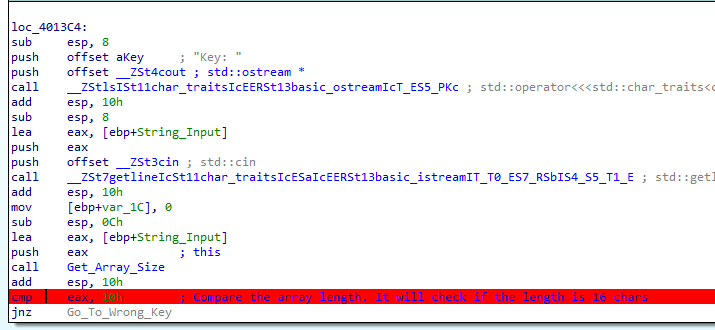
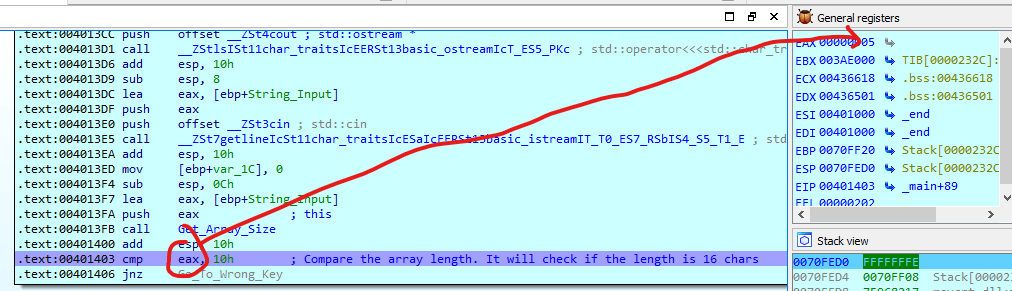
Lets move to the next condition and put the break point to it
let input this value Y123456789012345 to comply 16 char
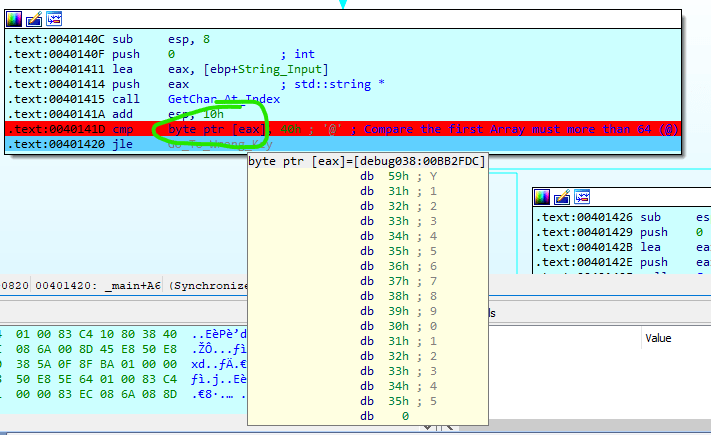
If we hover our mouse to byte ptr [eax] then we can see that the input value from the application as the picture shown above. the command cmp byte ptr [eax], 40h means it will compare the first char of the array is more that 64 where Y is 89 in decimal.
additionaly, we can see that byte ptr [eax] is pointing to memory 00BB2FDC, we can go jump there by two ways which are
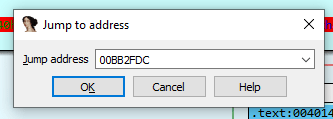
By using ‘g’ shortcut and put the memory that we want to inspect which is 00BB2FDC and press enter to OK
or the second way
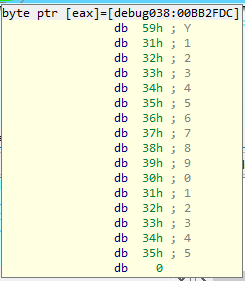
You will be directed to the memory address that will look like below
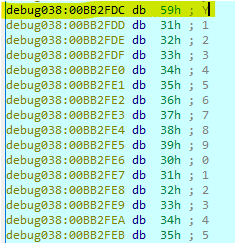
I would also like to inform you that IDA has capability to define series of memory to become string so that it is easier to read by selecting the memory address then right click or press A to make it as string
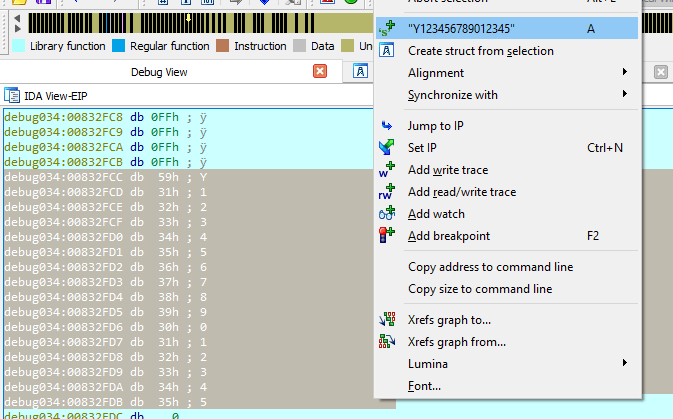
and become like

as the default, IDA will give it a variable name with the current value on it aY1234567890123 where you can rename it to a meaningful name for you by pressing n

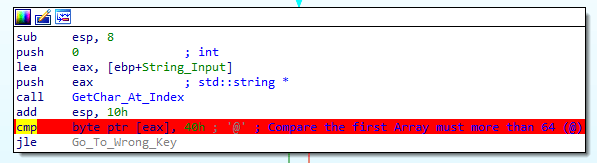
OK Next is to go to the third condition
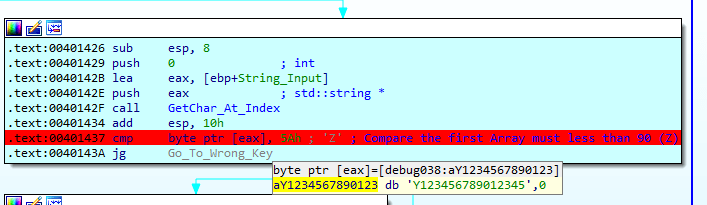
Here the check is to ensure that the first char is less than Z or 90
So now we can actually imagine the key would be like this Y***************
OK, I will post another program flow and check in the next post